In the cybersecurity profession we serve to secure organizations such as corporations or SME businesses from threats. These threats are ever changing and are doing so faster than ever, so it's paramount to stay ahead of the curve if you are to adequately protect your organizations.
One of the best ways to stay up to date on the threats we face in the corporate sphere is via the most recently published surveys and reports summarizing the experiences of industry leaders, researchers and practitioners working and serving in this space. By analyzing these reports, we're able to quickly learn from the experience of others and make sure we reduce our blind spots.
Companies like Microsoft, IBM, Palo Alto and more share their compiled observations and data from the most recent year to help shed light on how the threat landscape is changing. Year on year, we see trends we need to be aware of to improve our defenses and best allocate our resources.
Further, aided by their professional presentation and explanations geared towards an audience broader than only cyber technicians, they are useful as tools to be shared with more stakeholders in the corporate environment to help them better understand today's cyber challenges.
Note that we present here our preference for reports with actual insights and learning to be had that advances knowledge forward for cybersecurity workers, rather than surveys that just circle around "executives opinions on the latest shiny buzzwords".
At the same time, few of us have the time to read all of the top 20+ best annual reviews we survey every year, so here in this blog post we make recommendations as to which might be the best for you to check out based on your needs and position. Let's hit the list!
Another note, we aren't the first to review or think about comparing all of the available cybersecurity annual reports, and most notably a great resource is Jacob Wilson's comprehensive list of all them all found and gathered in one place: https://github.com/jacobdjwilson/awesome-annual-security-reports
In our review, we don't cover them all, rather we pick and choose among the best (from our perspective and needs) and only include ones here we actually recommend checking out.
Microsoft
Title: Microsoft Digital Defense Report 2025 (MDDR)
Link: https://www.microsoft.com/en-us/corporate-responsibility/cybersecurity/microsoft-digital-defense-report-2025/
Great for:
A sober overview based on perhaps one of the largest available datasets of their huge customer base and systems. Very good detail with specific examples of tactics, techniques and procedures and calling out and informing about which malware tools like ClickFix have been the worst offenders and which CVE vulnerabilities like the SimpleHelp RCE chain had the most impact throughout the year.
The MDDR report is also quite good at including clear and actionable policy and technical recommendations. This report is really a great resource we highly recommend reading in its entirety if can make the time, 5 out of 5 stars.
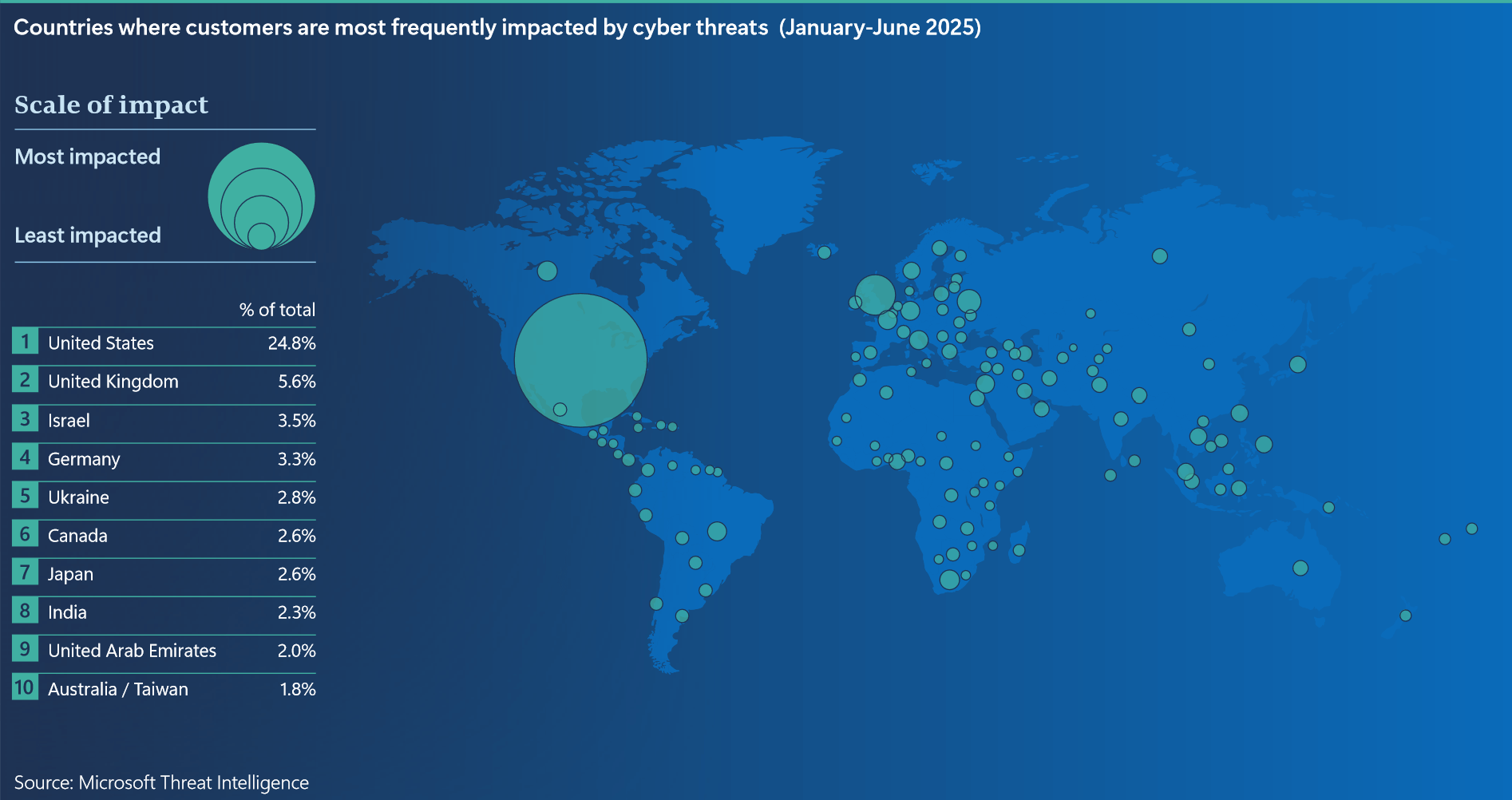
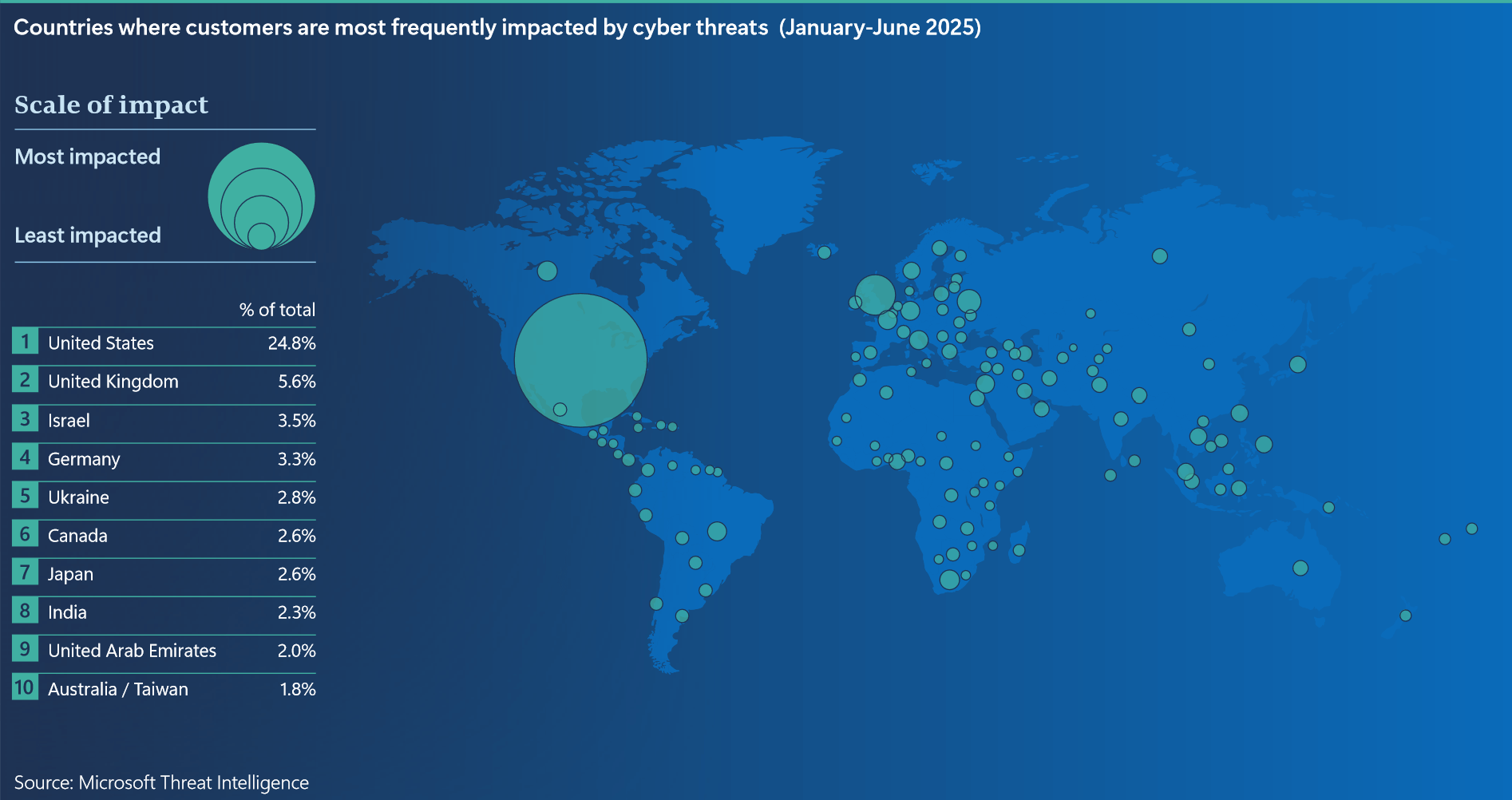
Microsoft - Countries Most Often Impacted by Cyber Attacks
Sample takeaways:
- 97% of identity attacks were password spray attacks. Even as more sophisticated tactics evolve, most identity attackers exploit the common problem of weak and overused passwords.
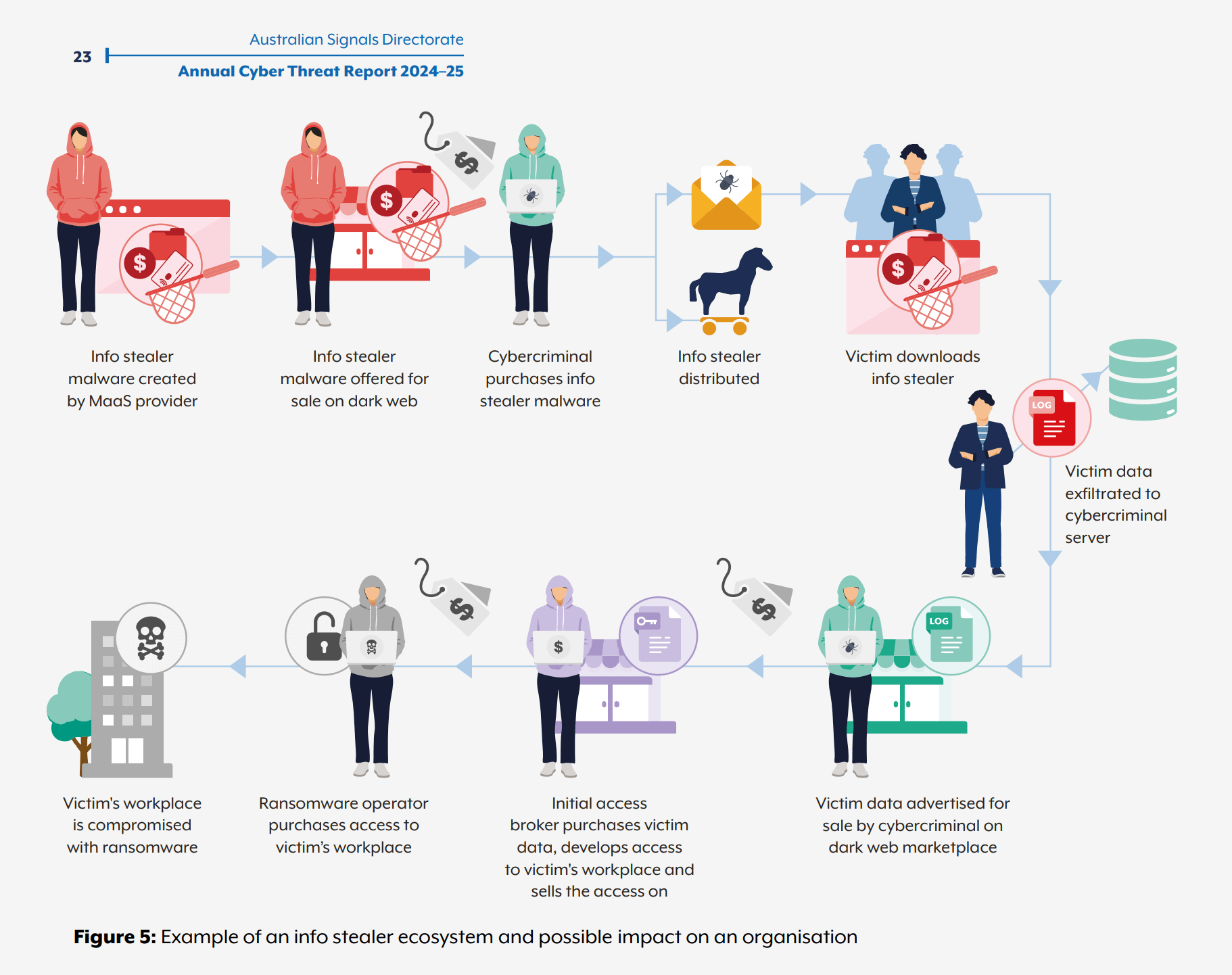
- Lumma Stealer was the most prevalent infostealer observed between October 2024 and October 2025. A sophisticated malware-as-a-service (MaaS) platform, Lumma Stealer can retrieve sensitive data from various browsers and applications, such as cryptocurrency wallets. This data is then sold to access brokers through dark web forums and Telegram channels. Ultimately, other cyber criminals like ransomware operators can use the data to access target networks.
- ClickFix was the most common initial social engineering access method that Microsoft Defender Experts observed in Defender Expert notifications in the last year, accounting for 47% of attacks.
- Incident response investigations found that 28% of breaches were initiated through phishing or social engineering, 18% were via unpatched web assets, and 12% leveraged exposed remote services.
- Autonomous System Numbers (ASNs) are unique identifiers for collections of IP networks managed by single organizations. While over 50,000 ASNs carry authentication traffic daily, just 20 ASNs — only 0.04% — account for more than 80% of malicious password spray activity. This concentration underscores the importance of targeted threat intelligence and infrastructure-aware defenses.
- AI-automated phishing emails achieved 54% click-through rates compared to 12% for standard attempts—a 4.5x increase. AI enables more targeted phishing and better phishing lures.
IBM
Title: Cost of a Data Breach Report 2025
Link: https://www.ibm.com/reports/data-breach
Great for:
Understanding the costs associated with data breaches (obviously, from the name) but it really details the costs well and is a good tool for driving home the understanding of the value of investing in security. Has good info on factors and implementations that can help decrease (or unfortunately increase) the costs involved in a data breach. Is light on specific technical implementation recommendations but is a good high level snapshot. 4 out of 5 stars.
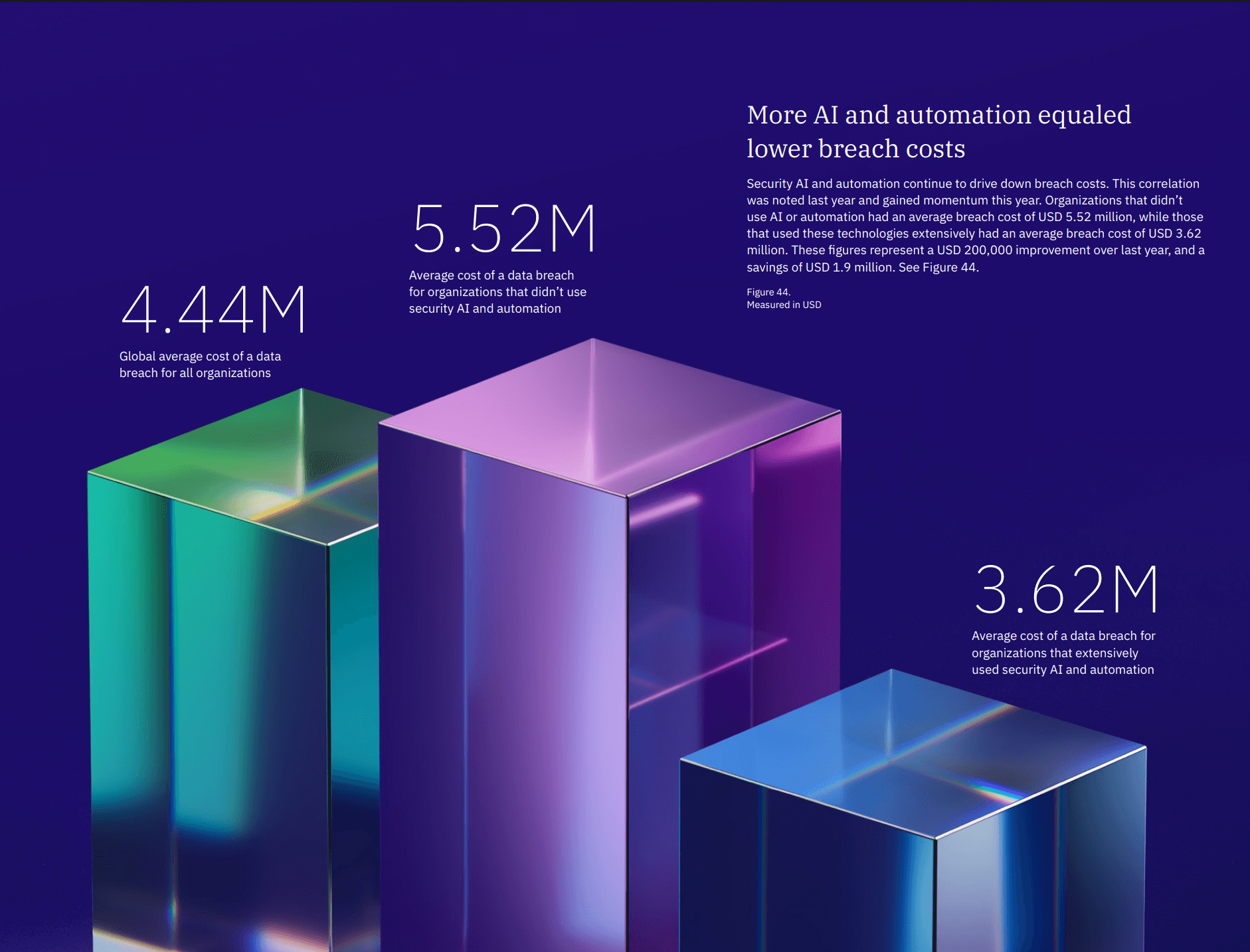
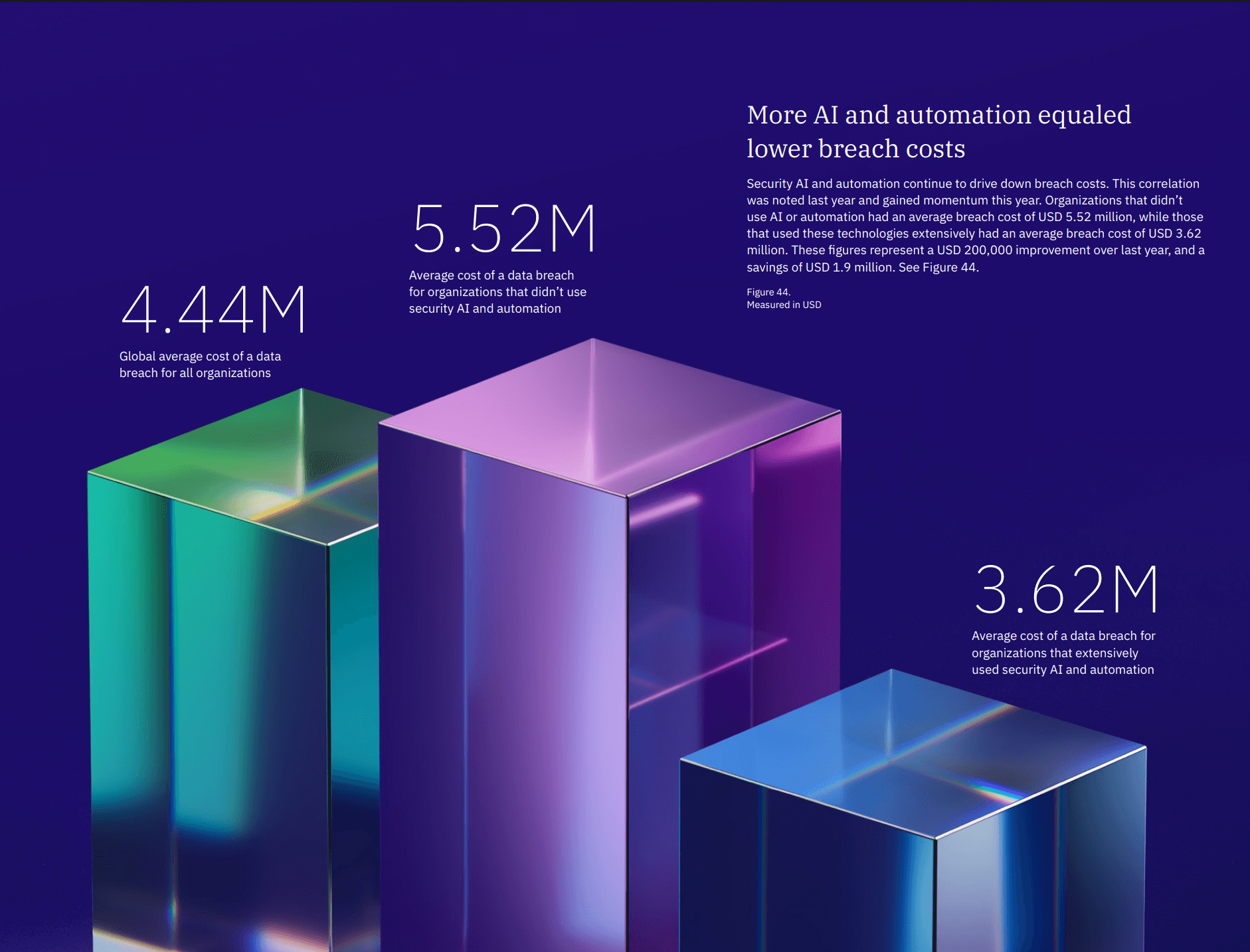
IBM - More AI and Security Automation lowered breach costs
Sample takeaways:
- The global average cost of a data breach dropped to USD 4.44 million from USD 4.88 million in 2024, a 9% decrease and a return to 2023 cost levels. Faster identification and containment of breaches—much of it from organizations’ own security and security service teams, with help from AI and automation—drove this decline.
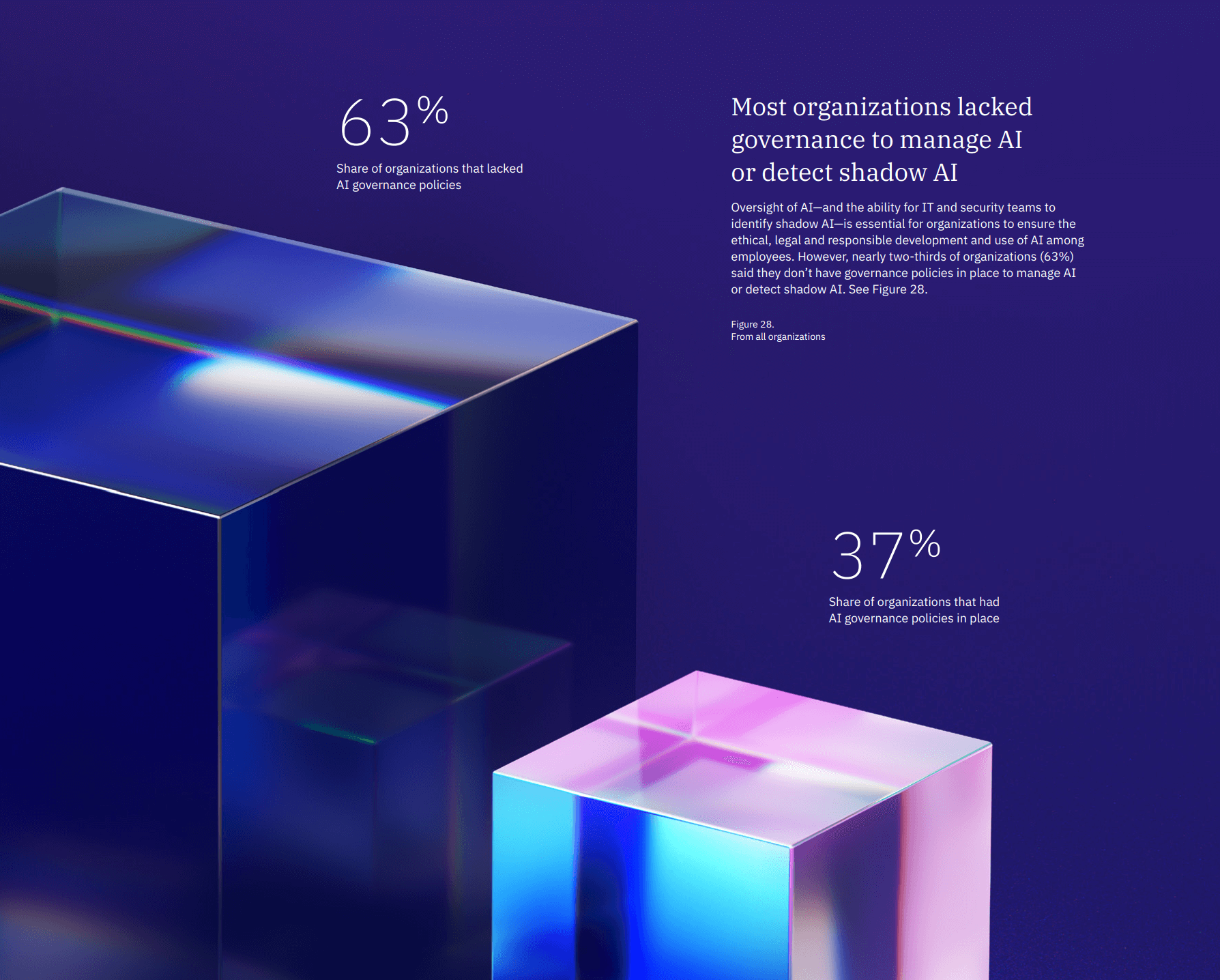
- Security incidents involving an organization’s AI remain limited — for now. On average, 13% of organizations reported breaches that involved their AI models or applications. However, among those that did, almost all (97%) lacked proper AI access controls. The most common of these security incidents occurred in the AI supply chain, through compromised apps, APIs or plug-ins. These incidents had a ripple effect: they led to broad data compromise (60%) and operational disruption (31%). The findings suggest AI is emerging as a high-value target.
- More ransomware victims refused to pay a ransom in 2025 (63%) than 2024 (59%). However, the average cost of an extortion or ransomware incident remains high, particularly when disclosed by an attacker (USD 5.08 million). At the same time, fewer ransomware victims reported involving law enforcement — 40% of organizations this year versus 53% last year.
- At USD 7.42 million, healthcare recorded the highest average breach cost among industries for the 12th consecutive year—even as it saw a sharp reduction from last year (USD 9.77 million). Attackers continue to value and target the industry’s patient personal identification information (PII), which can be used for identity theft, insurance fraud and other financial crimes. Healthcare breaches took the longest to identify and contain at 279 days. That’s more than five weeks longer than the global average.
IBM
Title: IBM X-Force 2025 Threat Intelligence Index
Link: https://www.ibm.com/reports/threat-intelligence
Great for:
Clear observations on all the main attack vectors (not just the result, like Ransomware or Data Breach, but how it happened, like via Infostealer or technical vulnerablities) and the how and why they have increased or decreased over time as prominent threats. Very good detail into each attack vector which gives a somewhat good sense of where to not fail in your security. Good definitions and overviews of the main attack vectors, it is a good document to share with IT folks to get them up to speed on what the actual current threats are. It's a very good read for threat intelligence, 5 out of 5 stars.
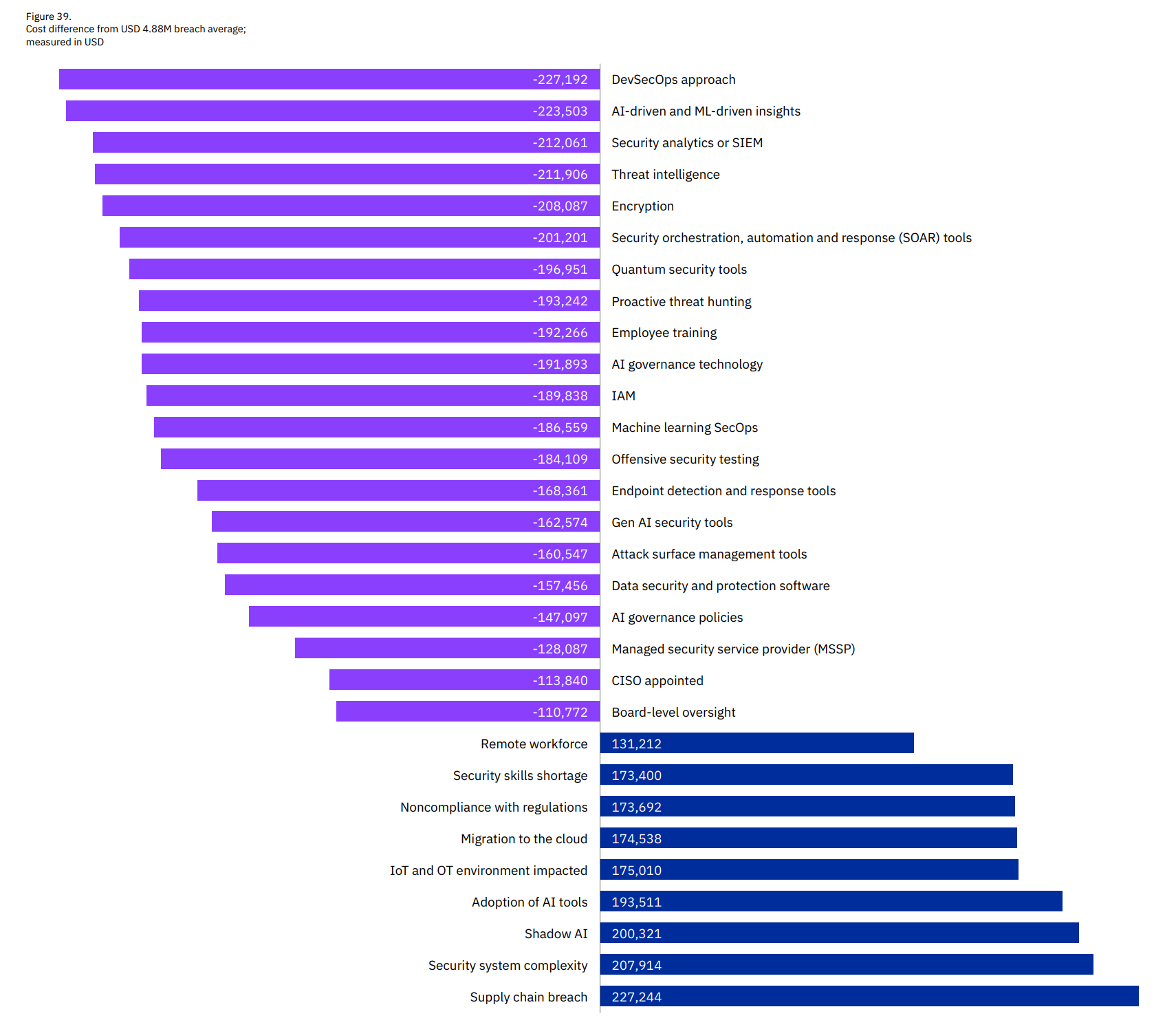
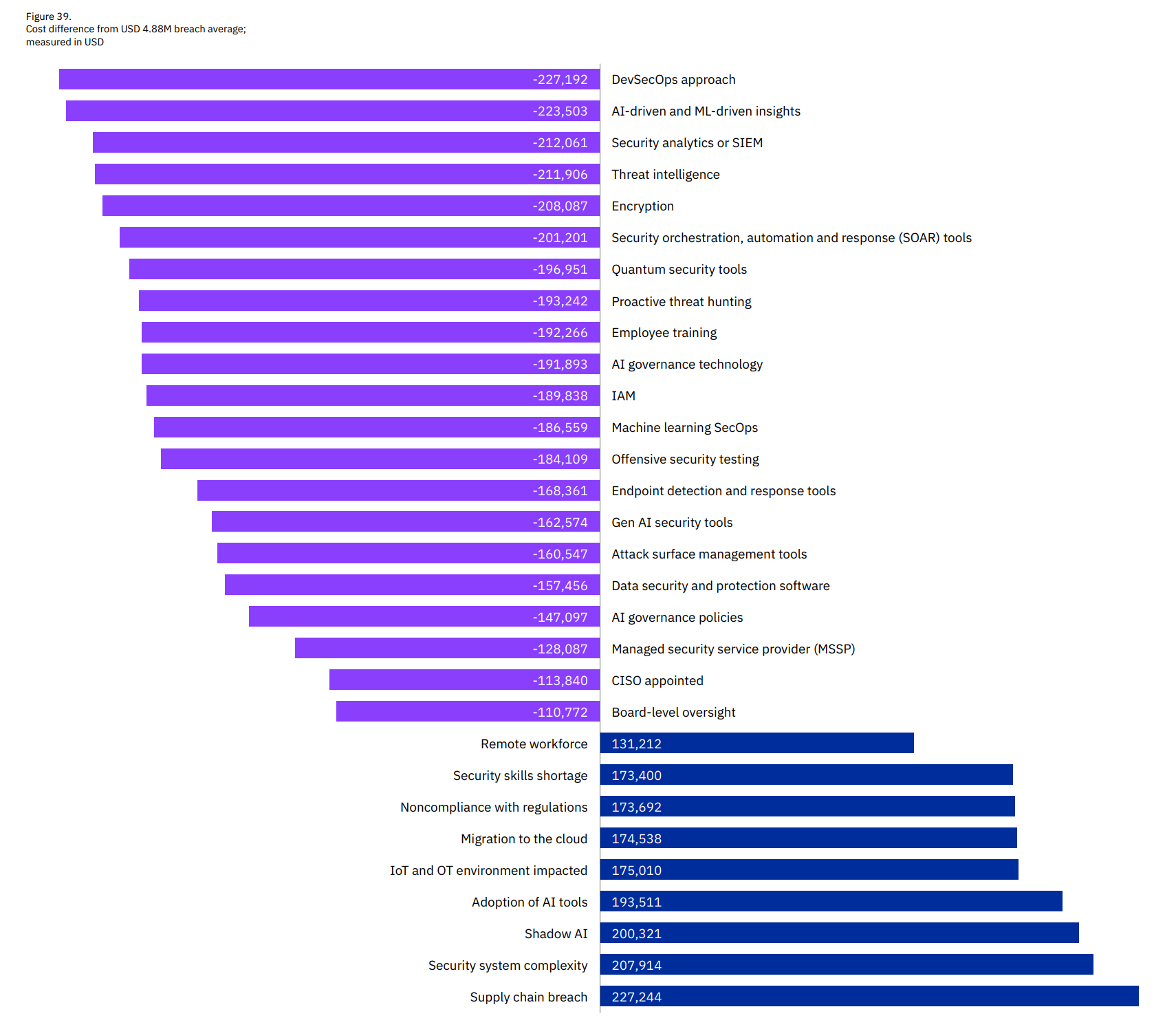
IBM - Effects of different factors on breach cost impacts
Sample takeaways:
- Number of infostealers delivered via phishing emails per week increases by 84%. Year-over-year, X-Force is seeing a rise in infostealers delivered via phishing emails and credential phishing. Both result in active credentials that may be used in follow-on, identity-based attacks. Phishing has emerged as a shadow infection vector for valid account compromises. By clicking on links that seem legitimate, users can unknowingly open the door to infostealer malware that siphons sensitive data from victims.
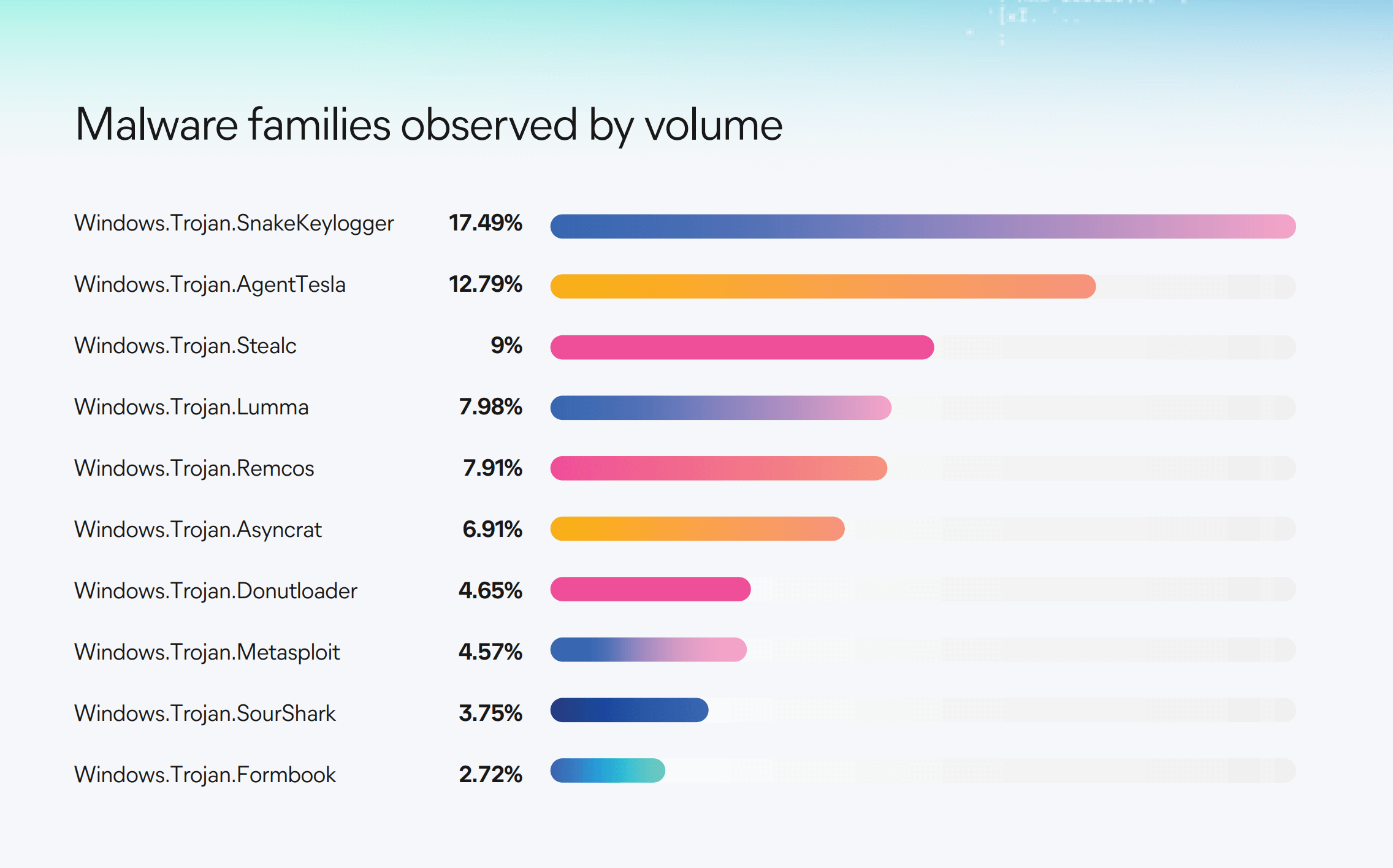
- The most common infostealer malware distributed directly via phishing was AgentTesla, followed by FormBook, SnakeKeylogger, and PureLogs Stealer. We also observed an increase in Hive0145 email campaigns distributing the Strela Stealer infostealer.
- The second change we observed in 2024 is an increase in credential phishing. Malicious URLs redirect victims to fake login sites for popular applications and harvest credentials.Both credential phishing and infostealer malware harvest active credentials for use in follow-on attacks. For second-stage attacks, the vector is use of valid accounts, one of the most common initial access vectors during the last two years.
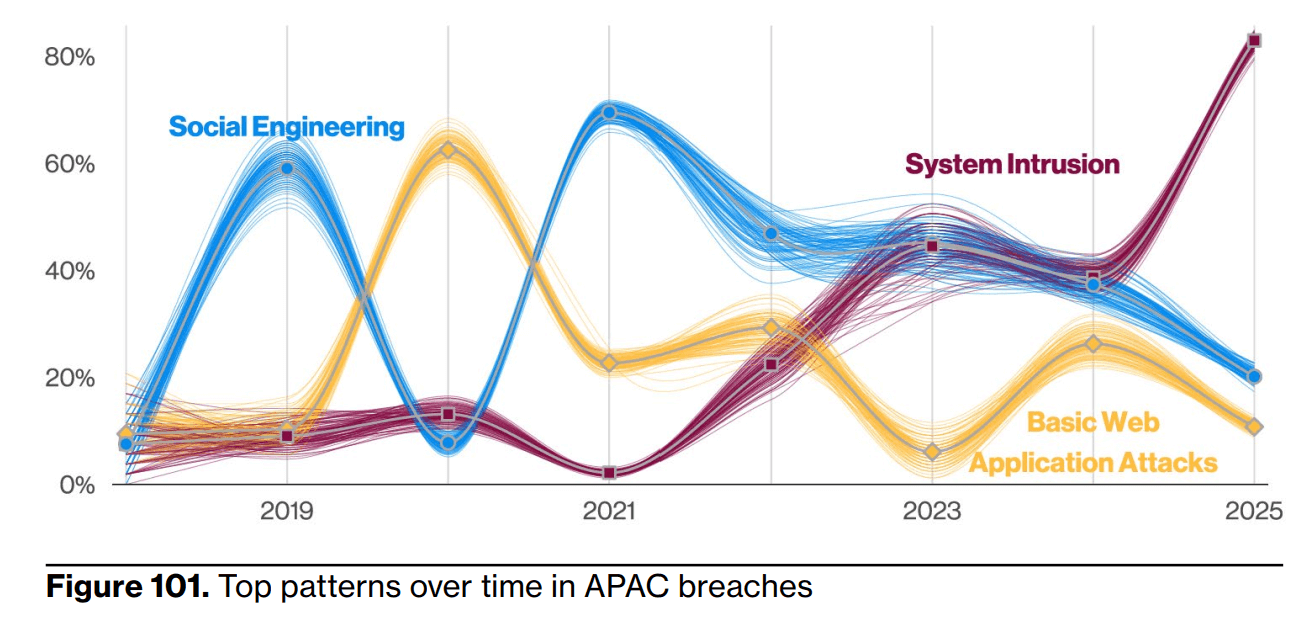
- Asia-Pacific region sees a 13% increase in attacks. Asia-Pacific (APAC) experienced the largest share of incidents in 2024 (34%). This underscores APAC’s growing exposure to cyberthreats, likely due to its critical role in global supply chains and its position as a technology and manufacturing hub.
- For the APAC region, key impacts—the intended or realized effect of an action on the victim—included data theft (12%), credential harvesting (10%), and extortion (10%). These reflect the sector’s susceptibility to attacks targeting sensitive data and operational disruption. The manufacturing sector remained the most targeted industry, representing 40% of incidents, followed by finance and insurance (16%) and transportation (11%).
- Manufacturing is the #1-targeted industry, four years in a row. Manufacturing organizations continued to experience significant impacts from attacks, including extortion (29%) and data theft (24%), targeting financial assets and intellectual property. Defying the declining trend in malware, manufacturing had the highest number of ransomware cases in 2024 as attackers continue to exploit outdated legacy technology in this industry.
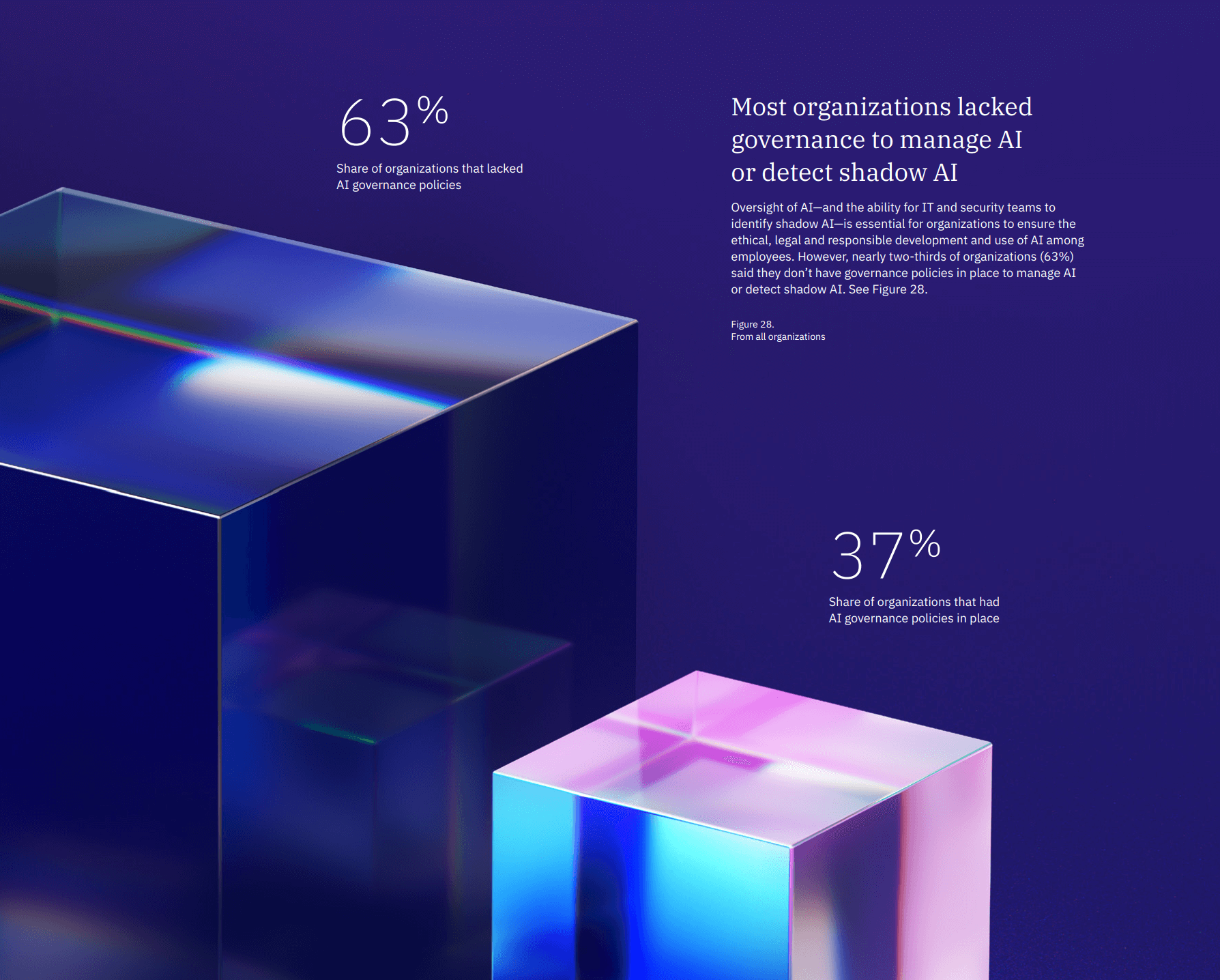
IBM - Lack of AI Governance
Verizon
Title: 2025 Data Breach Investigations Report
Link: https://www.verizon.com/business/resources/reports/dbir/
Great for:
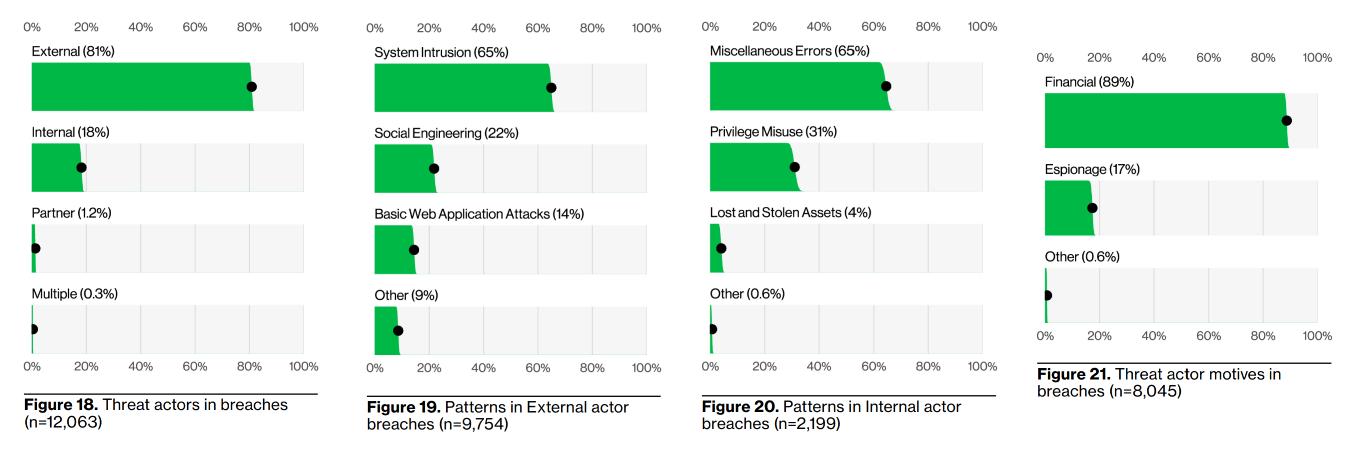
As the name applies, it's assessing a big dataset and research on actual data breaches, so it's a very good snapshot in trends of actual activity and threats. Though a predominantly US company, their data does cover 139 countries. It is written with a lot of tongue in cheek and dry humor, so they really jazz up a dry topic. They do cover recommendations to help mitigate threats with specific references to CIS controls. Overall, it's very good at covering the landscape of threats, 4 out of 5 stars.
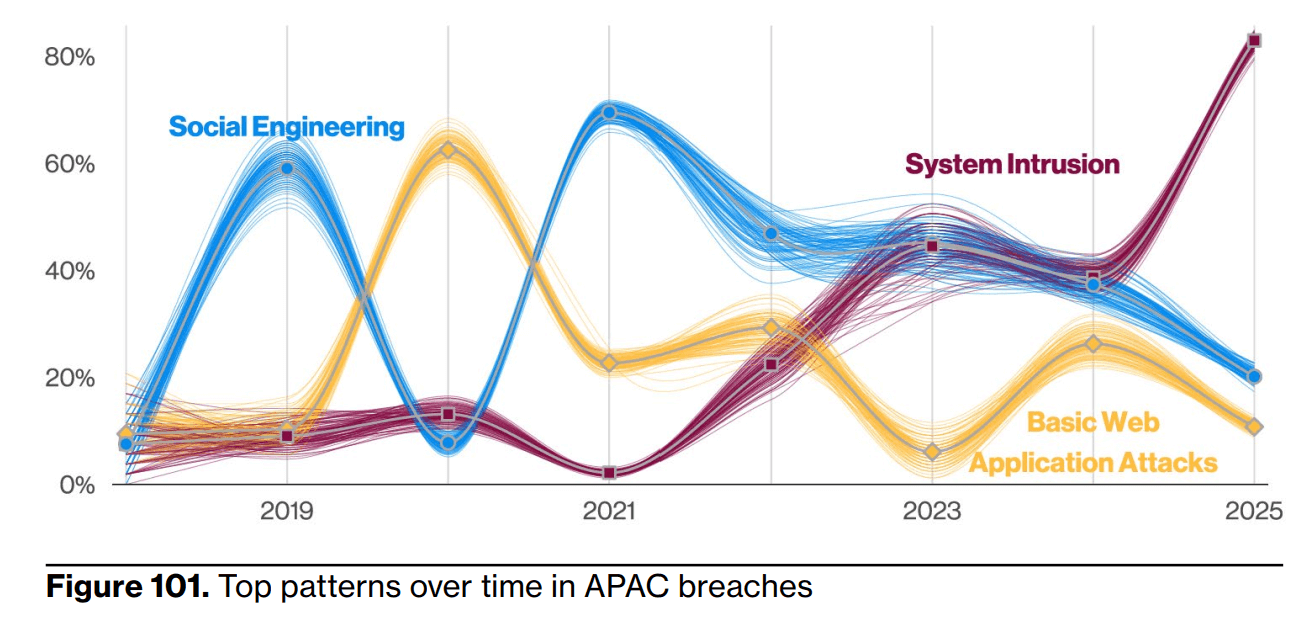
Verizon - Main attack vectors in Asia Pacific
Sample takeaways:
- Ransomware is disproportionally affecting small organizations. In larger organizations, ransomware is a component of 39% of breaches, while SMBs experienced ransomware-related breaches to the tune of 88% overall.
- The exploitation of vulnerabilities saw another year of growth as an initial access vector for breaches, reaching 20%. This value approaches that of credential abuse, which is still the most common vector. This was an increase of 34% in relation to last year’s report and was supported, in part, by zero-day exploits targeting edge devices and VPNs.
- An emerging threat from AI is the potential for corporate-sensitive data leakage to the GenAI platforms themselves, as 15% of employees were routinely accessing GenAI systems on their corporate devices (at least once every 15 days). Even more concerning, a large number of those were either using non-corporate emails as the identifiers of their accounts (72%) or were using their corporate emails without integrated authentication systems in place (17%), most likely suggesting use outside of corporate policy.
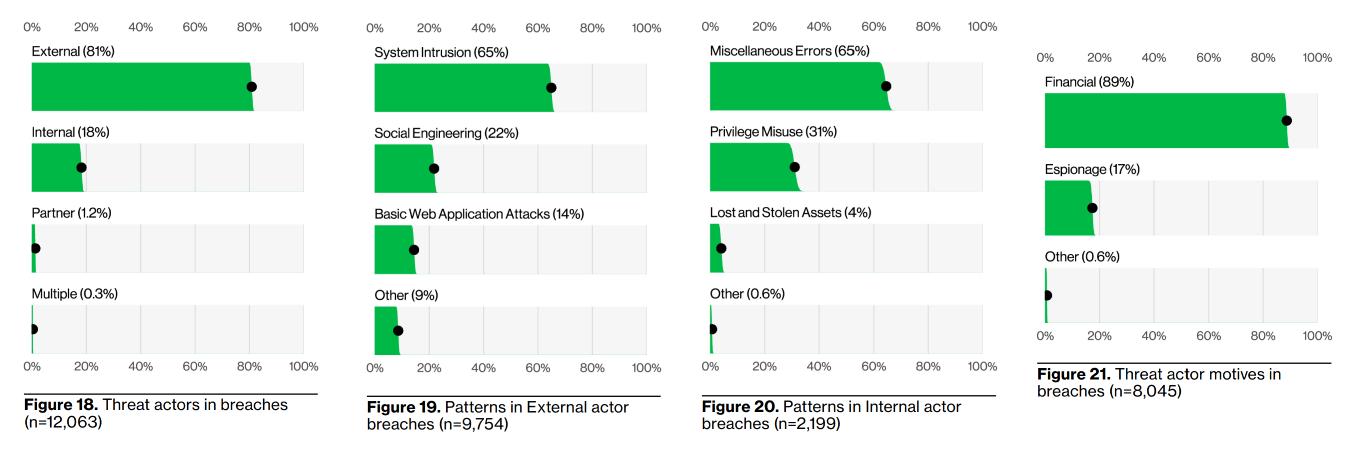
Verizon - Key survey statistics
Cisco
Title: The State of AI Security 2025
Link: https://www.cisco.com/c/en/us/products/security/state-of-ai-security.html
Great for:
Better than other Cisco annual cyber reports that are glaze over the eyes surveys of executive feelings, this report delivers as a great synopsis of the current AI-related threats and recent developments in policy and tech. Includes good explanations and ideas on the many AI threat vectors, and lots of detail on specific and noteworthy attacks in particular. Highly recommended read for the topic, 5 out of 5 stars.
Sample takeaways:
- Most AI threats and vulnerabilities are low to medium risk by themselves, but those risks combined with the increased velocity of AI adoption and the lagging development, implementation, and adherence to accompanying security practices will ultimately increase organizational risks and magnify potential negative impacts (e.g., financial loss, reputational damage, or violations of laws and regulations).
- The AI ecosystem's reliance on shared models, datasets, and libraries expands the attack surface into the AI supply chain. Supply chain attacks exploit the trust organizations place in third-party components—whether they be pre-trained models, open-source libraries, or datasets used to train AI systems. When parts of the supply chain are compromised, it can introduce hidden vulnerabilities that may not be discovered until significant damage has been done.
- Developers frequently integrate pre-trained models, software libraries, and datasets from external sources, which can create several risks, such as backdoored models, where attackers embed a hidden functionality into a pre-trained model, allowing them to manipulate outputs under specific conditions or run arbitrary code when the model is loaded.
- Cybercriminals that cannot or do not wish to bypass security built into legitimate LLMs sometimes opt to build their own. Cybercriminal-designed LLMs do not include any of the restrictions against malicious use. In fact, some of these LLMs are specifically designed to facilitate criminal activity, including applications like GhostGPT, DarkBard, DarkGPT, and FraudGPT. Most of these LLMs are advertised for sale to cybercriminals on hacking forums.
- Agentic AI systems (models that can act autonomously to achieve goals without the need for constant human guidance) could imperil organizations that are neither prepared nor equipped to handle agentic systems and their potential for compromise. At least 14 distinct threat vectors have been identified with agentic systems, including: memory poisoning, where false or misleading data is introduced into an AI’s memory systems to exploit the agent’s context; misaligned and deceptive behaviors, where an AI agent is used to conduct harmful or disallowed actions; and unexpected remote code execution and code attacks, where attackers inject malicious code or execute unauthorized scripts.
Crowdstrike
Title: CrowdStrike 2025 Global Threat Report
Link: https://www.crowdstrike.com/en-us/global-threat-report/
Great for:
A very concise and easy to read overview of the current threat landscape, with little fluff and distraction. It is, however, replete with pitches for their own services, which is understandable but distracting from the valuable info. Multiple relevant case studies are cited and detailed which helps puts all the takeaways in a clear context. 4 out of 5 stars, recommended to look at.
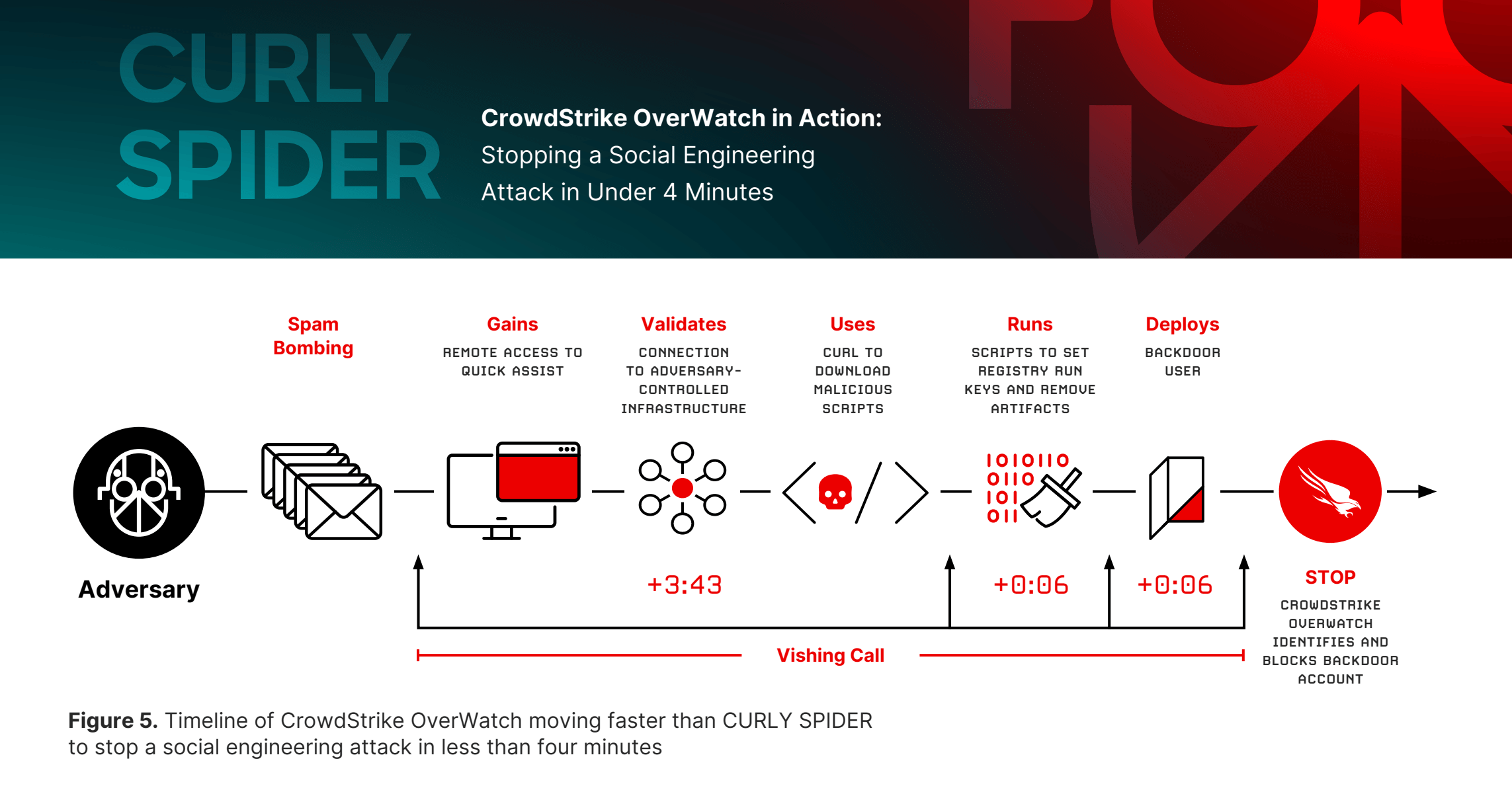
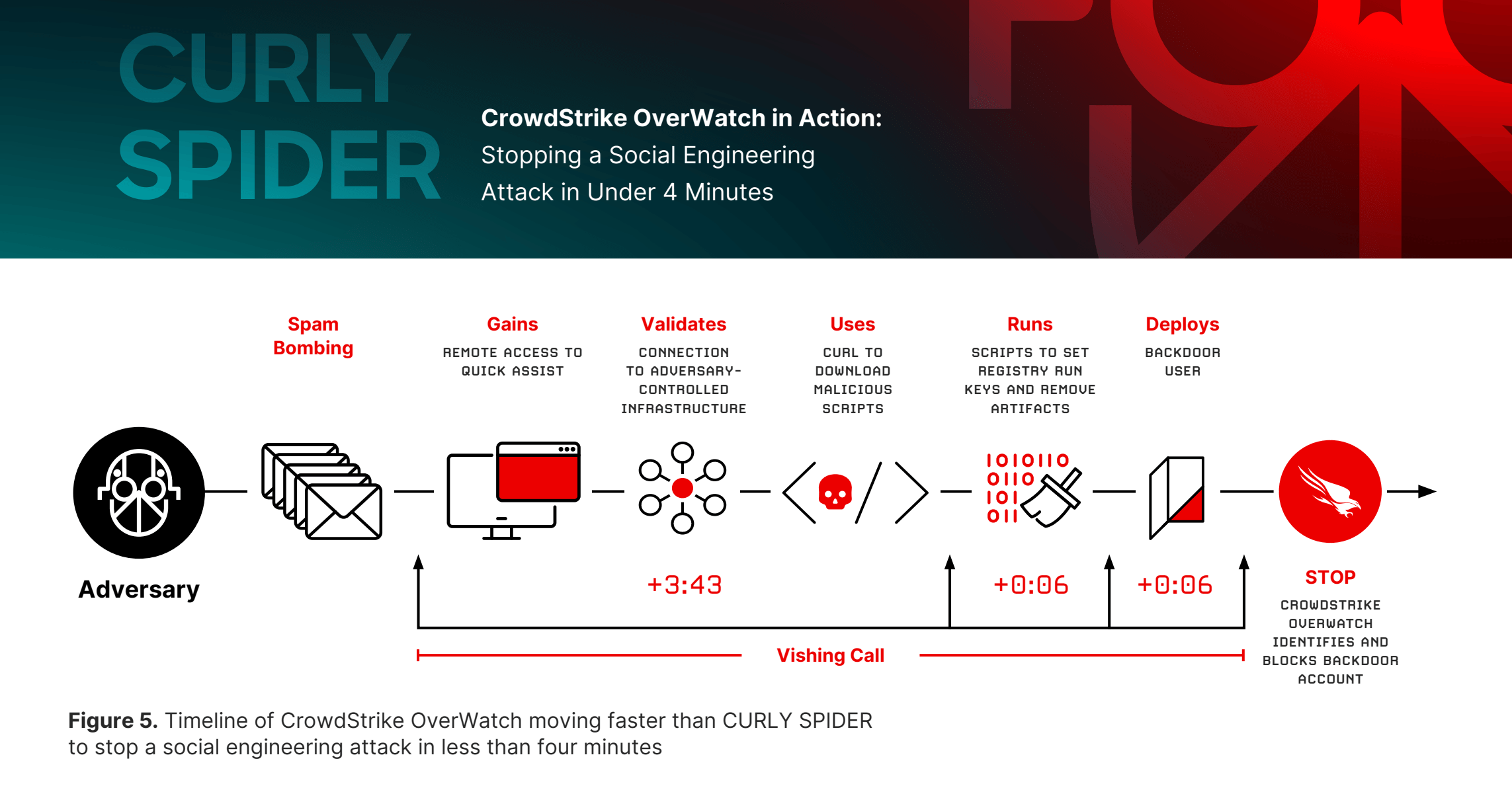
Crowdstrike - Attack method of Curly Spider
Sample takeaways:
- Breakout time — how long it takes for an adversary to start moving laterally across your network — reached an all-time low in the past year: The average fell to 48 minutes, and the fastest breakout time we observed dropped to a mere 51 seconds.
- Voice phishing (vishing) attacks, where adversaries call victims to amplify their activities with persuasive social engineering techniques, saw explosive growth — up 442% between the first and second half of 2024.
- Attacks related to initial access boomed, accounting for 52% of vulnerabilities observed by CrowdStrike in 2024. Providing access as a service became a thriving business, as advertisements for access brokers increased 50% year-over-year.
- GenAI played a pivotal role in sophisticated cyberattack campaigns in 2024. It enabled FAMOUS CHOLLIMA to create highly convincing fake IT job candidates that infiltrated victim organizations, and it helped China-, Russia-, and Iran-affiliated threat actors conduct AI-driven disinformation and influence operations to disrupt elections
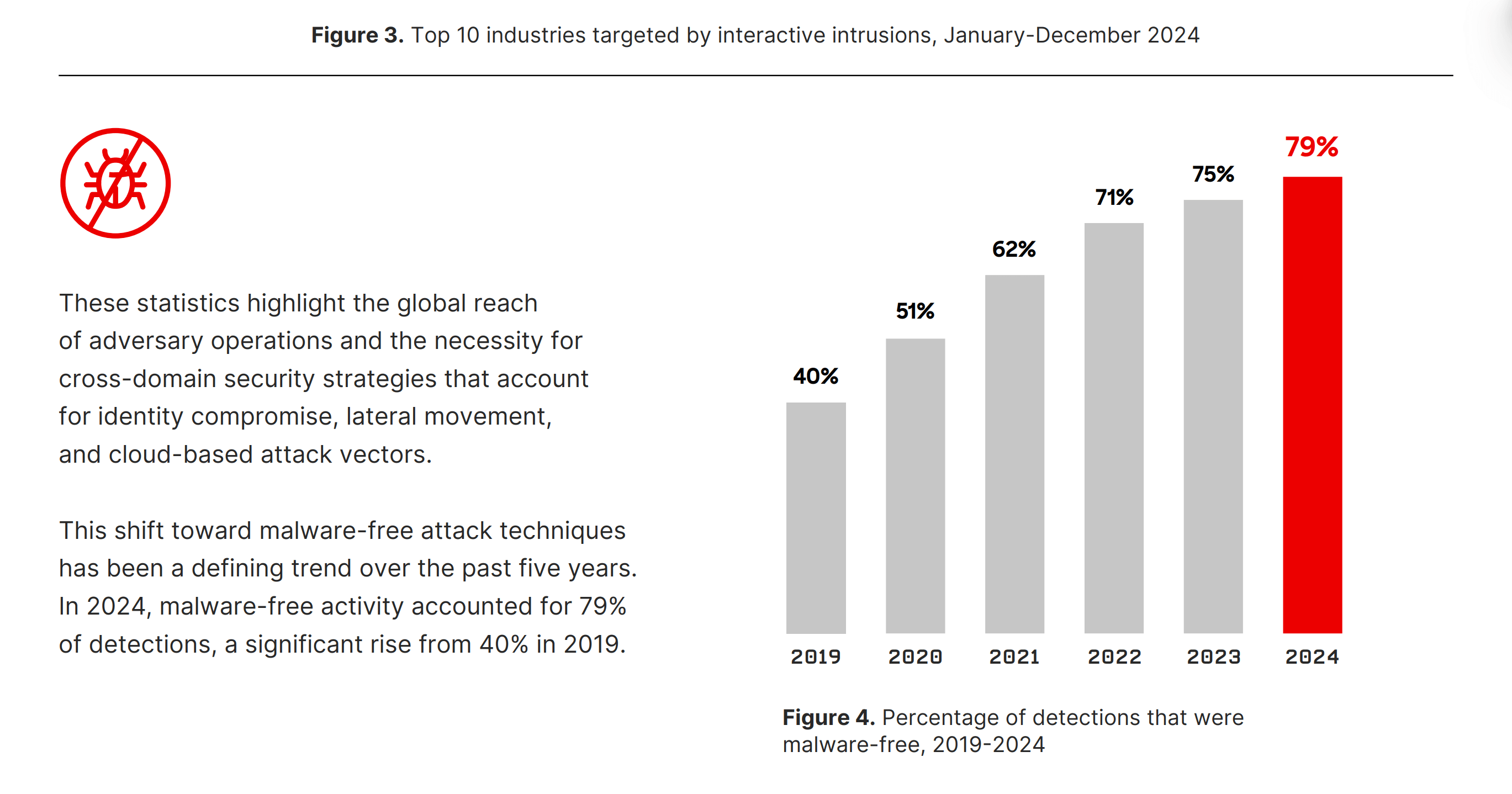
- Rather than delivering malware, eCrime adversaries are increasingly leveraging legitimate remote monitoring and management (RMM) tools to access a victim’s system — and therefore making malware non-essential for successful operations.
- Every breach starts with initial access, and identity-based attacks are among the most effective entry methods. Instead of traditional malware, adversaries favor faster and stealthier methods such as vishing, social engineering, access broker services, and trusted relationship abuse. A major driver behind this shift is the rise of access brokers: specialists who acquire access to organizations and sell it to other threat actors, including ransomware operators.
- Modern cyber threats are increasingly dominated by “interactive intrusion” techniques, where adversaries execute hands-on-keyboard actions to achieve objectives. Unlike traditional malware attacks, these intrusions rely on human adversaries mimicking legitimate user or administrator behavior, making them exceptionally difficult to detect. In 2024, CrowdStrike observed a 35% year-over-year increase in interactive intrusion campaigns.
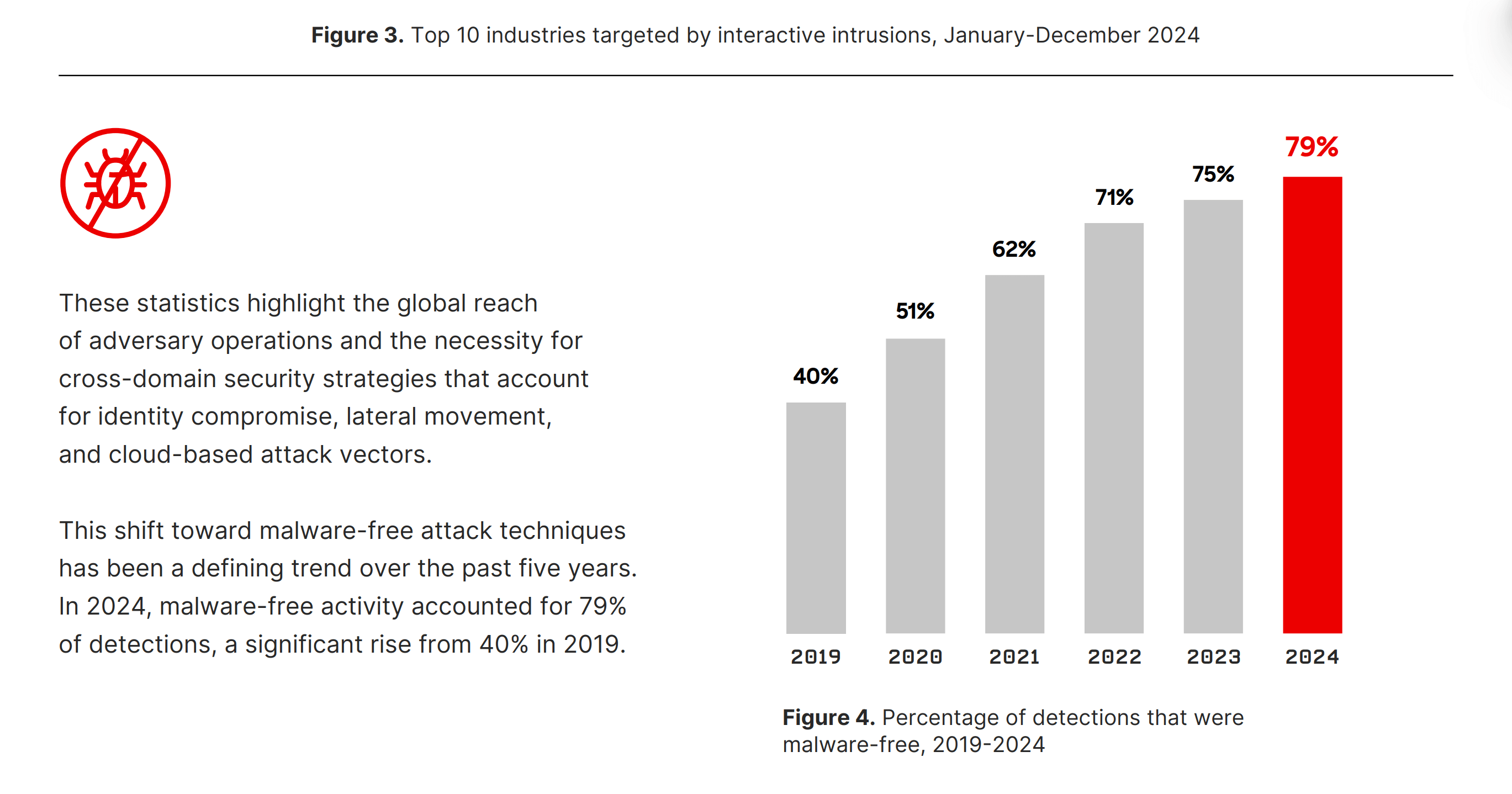
Crowdstrike - Rise in Malware-free attacks
Palo Alto Unit 42
Title: Global Incident Response Report 2025
Link: https://www.paloaltonetworks.com/resources/research/unit-42-incident-response-report
Great for:
Very clear description of trends in threats, describing how they have changed over time and why. Good document for sharing with IT-adjacent executives for an overall understanding of the cyber landscape. 5 out of 5 stars and recommended for its great content, ease of understanding of all concepts, and good case studies as reference.
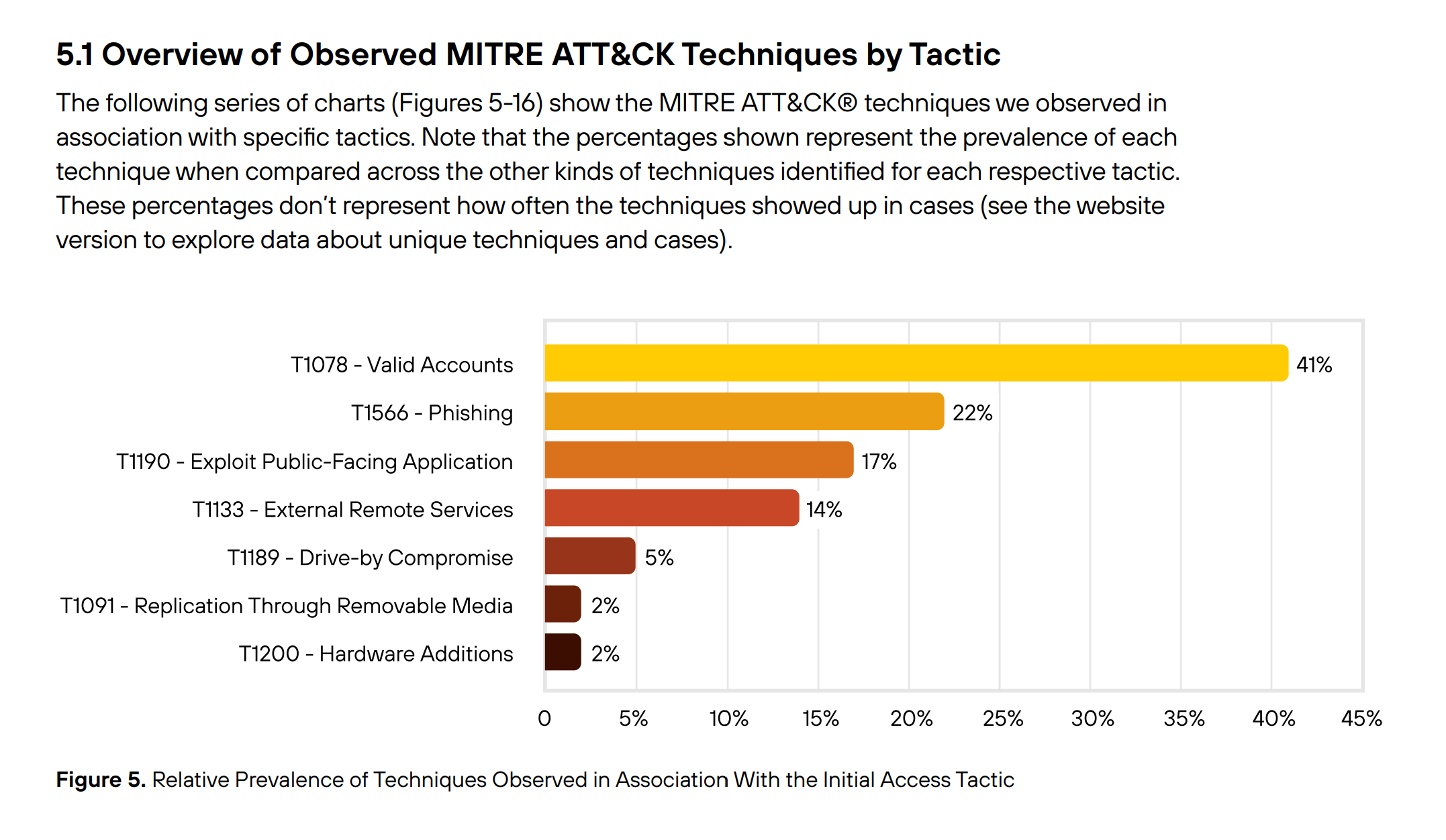
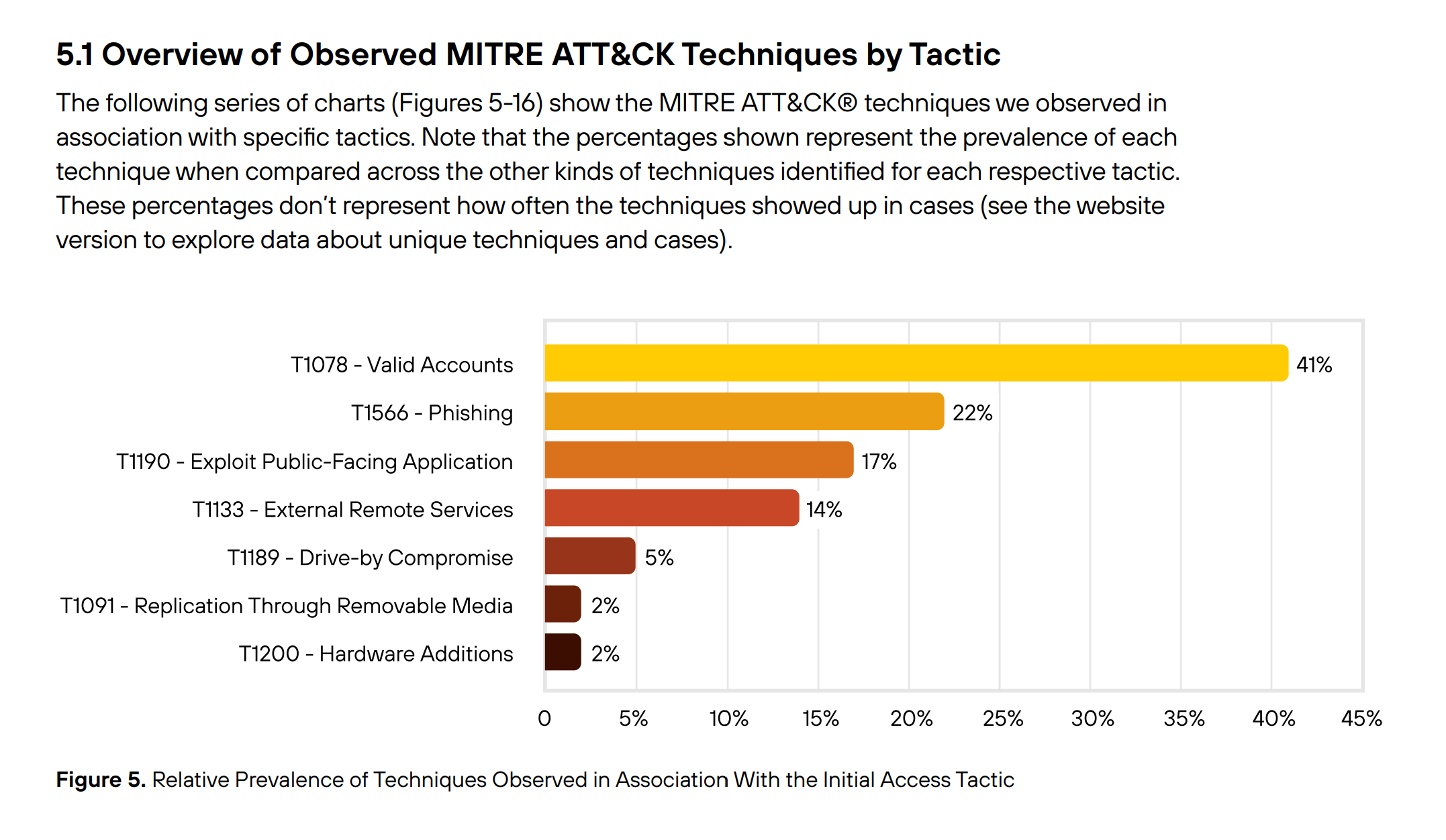
Palo Alto - Prevalence of Techniques in Initial Access
Sample takeaways:
- Threat actors are augmenting traditional ransomware and extortion with attacks designed to intentionally disrupt operations. In 2024, 86% of incidents that Unit 42 responded to involved business disruption — spanning operational downtime, reputational damage or both.
- Software supply chain and cloud attacks are growing in both frequency and sophistication. In the cloud, threat actors often embed within misconfigured environments to scan vast networks for valuable data. In one campaign, attackers scanned more than 230 million unique targets for sensitive information.
- The increasing speed of intrusions — amplified by automation and streamlined hacker toolkits — gives defenders minimal time to detect and respond. In nearly one in five cases, data exfiltration took place within the first hour of compromise.
- Organizations face an elevated risk of insider threats via malicious intent job applicants securing positions, as nation-states like North Korea target organizations to steal information and fund national initiatives. North Korean threat actors exploit traditional hiring processes with stolen or synthetic identities backed by detailed technical portfolios. These portfolios can include legitimate references obtained through identity manipulation and previous real work histories that pass basic verification. Such cases tied to North Korea tripled in 2024.
- Attackers are now more sophisticated, often combining encryption with data theft and double extortion threats, but encryption itself is still a go-to tactic. In fact, Unit 42’s latest incident response data shows that encryption remains the most common tactic used in extortion cases, holding relatively steady over the past 4 years.
- Over time, as organizations have improved their data backup practices, encryption as the sole extortion tactic has become less effective. Backups have helped more organizations recover faster — nearly half (49.5%) of impacted victims were able to restore from backup in 2024. As seen in Figure 1, this is about five times as many as in 2022, when only 11% of victims were able to restore from backup.
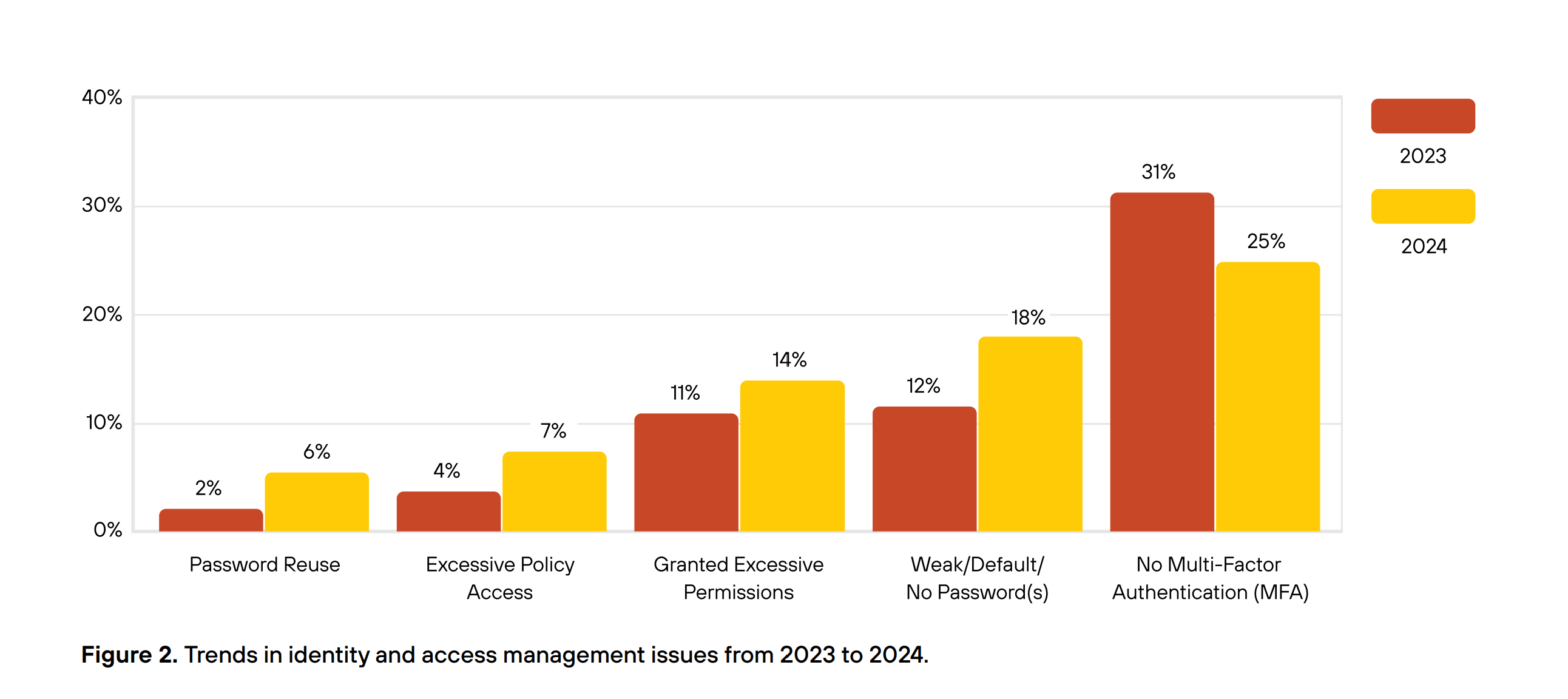
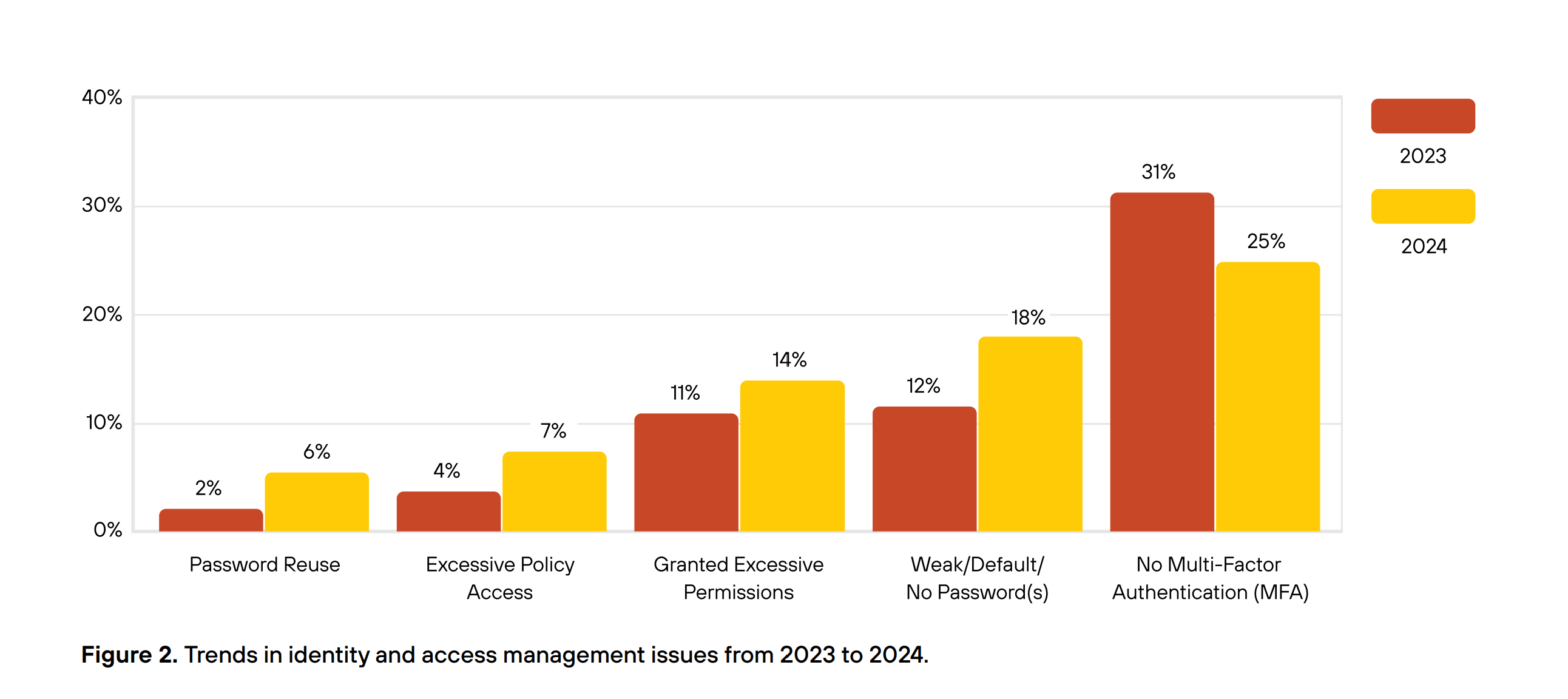
Palo Alto - Trends in IAM attack issues
Elastic
Title: 2025 Elastic Global Threat Report
Link: https://www.elastic.co/resources/security/report/global-threat-report
Great for:
Good at the outset at tying trends and issues in the current landscape to practical improvements in mitigations an organization can directly work on. Later on in the majority of sections it might read as a little dry, with many sections feeling like lists of data, but there are some gems of insight in there. There is a lot of good specific data in there, which could be especially useful if you are working on System Hardening and checking through to make sure all settings are optimized for security. 4 out of 5 stars, good to take a look at and if you need very detailed specific data on some details.
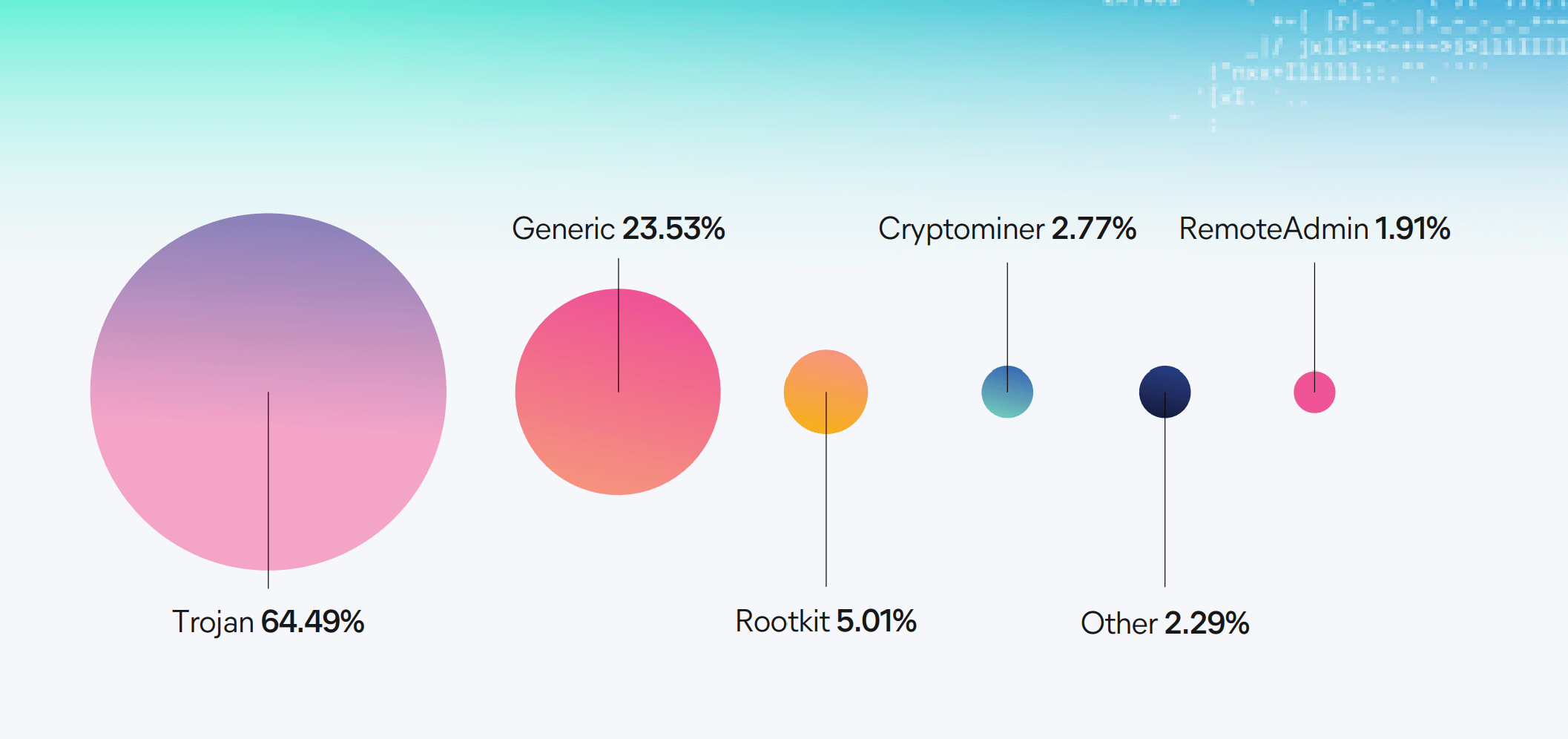
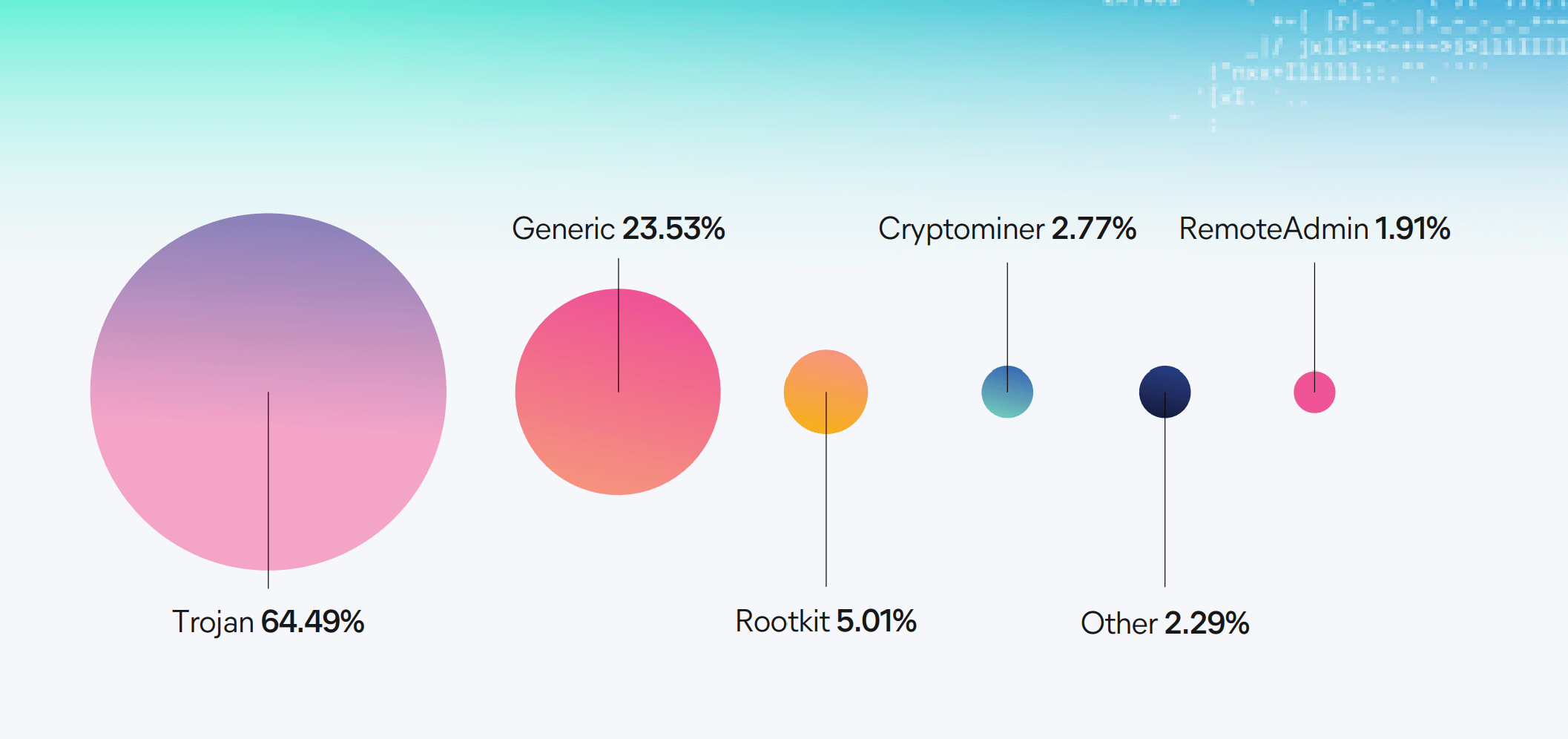
Elastic - Malware by category
Sample takeaways:
- The adversary’s playbook has fundamentally changed. The era of slow, methodical intrusion has been replaced by a new model of high-velocity attacks that prioritize speed and efficiency. Attackers are now exploiting the trusted tools and workflows of the modern enterprise — cloud accounts, developer platforms, and browsers — making their actions harder than ever to distinguish from normal activity.
- Data leaks in GitHub can occur when users accidentally commit credentials, API keys, tokens, or other exploitable information directly into their code. These secrets, if exposed in a public repository, can be immediately scraped by automated bots. Malicious actors can then use these stolen secrets to gain unauthorized access to internal systems, cloud infrastructure, or confidential data. Even in private repositories, a secret leak can be a significant issue, as it increases the risk of an insider threat or exposure if the repository is ever compromised. The sheer volume of code and the rapid pace of development make it a constant challenge to prevent these leaks from happening.
- Adopt automation with human-in-the-loop oversight: AI-assisted detection and response helps to accelerate decisions, but it is not a standalone replacement to human analysts and responders. Enterprises should deploy automation that speeds defenders while maintaining human judgment at key points.
- Strengthen browser defenses: Browser credential stores remain a high-value target. Enterprises should harden plugins, extensions, and third-party integrations while expanding visibility into credential theft attempts.
- Elevate identity validation: Adversaries increasingly exploit weak authentication and impersonation technologies. Continue to invest in strong identity verification, reinforce know-your-customer (KYC) practices, and make identity assurance a first-class security control.
- Prioritize memory protection: Attackers continue to weaponize memory-based techniques. Enterprises should emphasize sensors and detections that monitor memory for injection, obfuscation, and other stealthy behaviors.
- Secure the development and supply chain ecosystem: Threats against IDEs, package managers, and third-party libraries highlight the importance of continuous controls around developer tools and supply chain observation and detection.
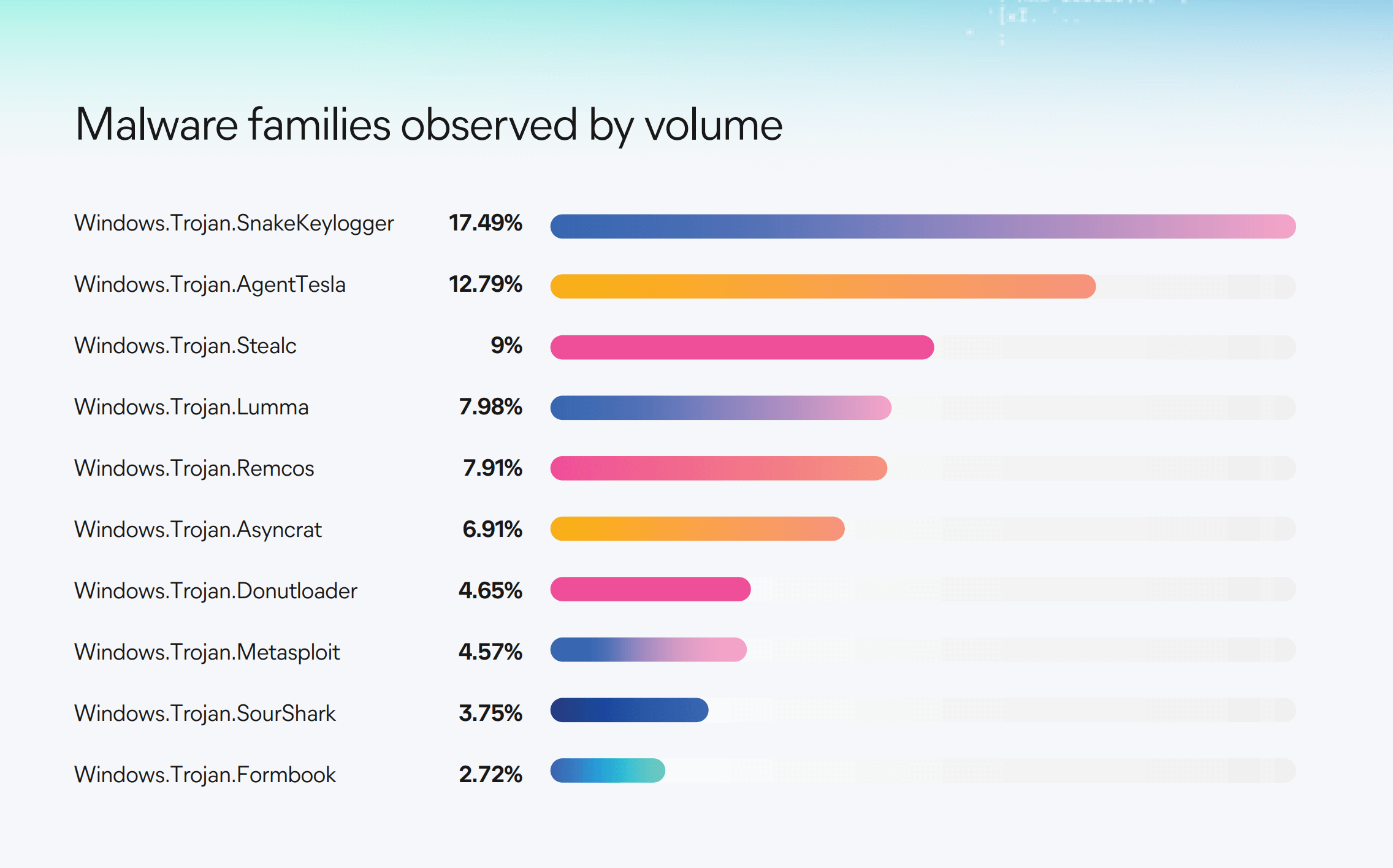
Elastic - Malware families by volume
ESET
Title: ESET Threat Report H2 2025
Link: https://www.welivesecurity.com/en/eset-research/eset-threat-report-h2-2025/
Great for:
Detailed insights from specific and relevant case studies that are really helpful to much better understand all attack vector topics at a deeper level. At a recommendation level it might be general, but the concepts to improve defenses and staff training are there. It gets deep into the weeds about each case study, so it's more a read for practitioners looking for in-depth research rather than executives looking for the broad trends.
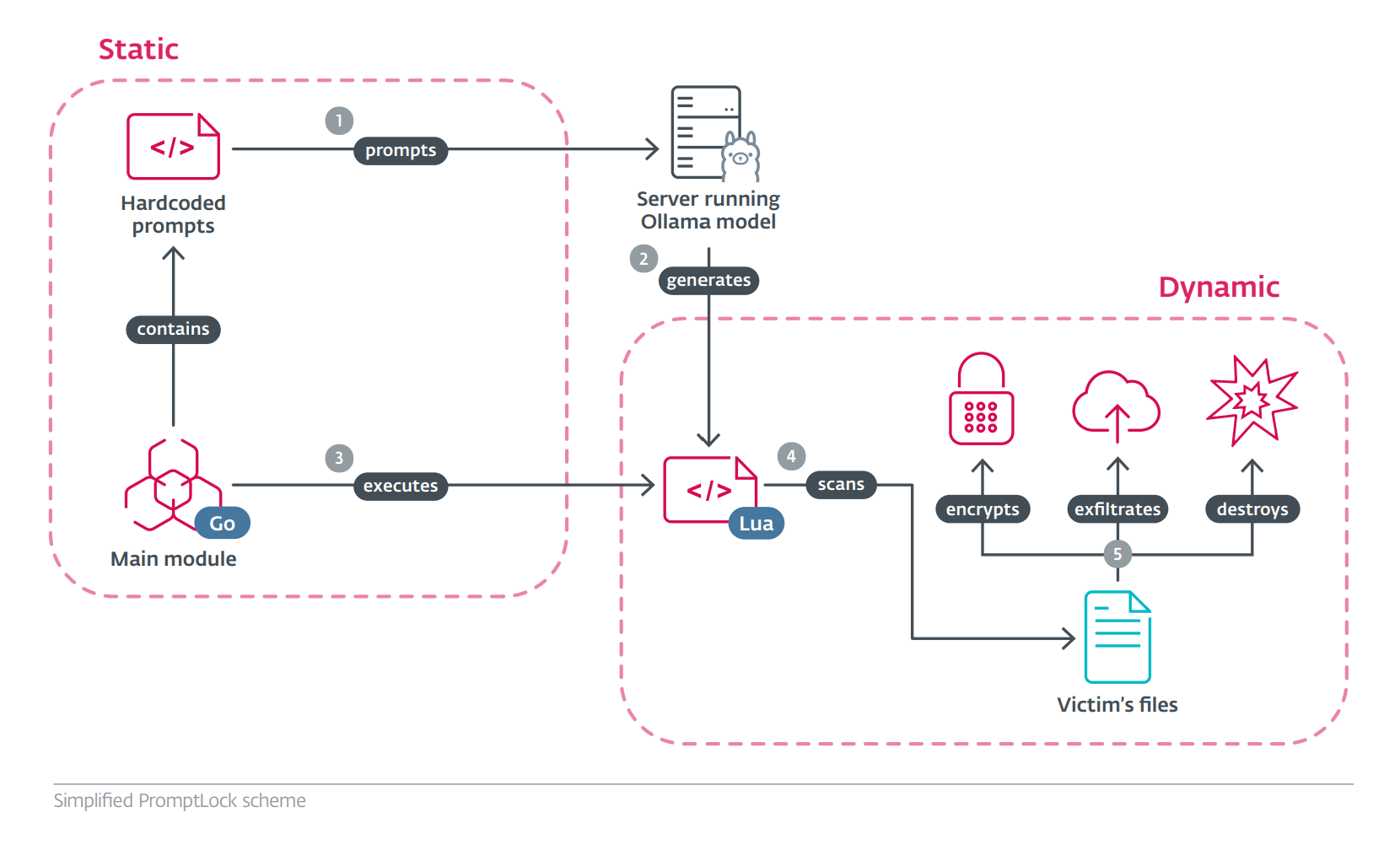
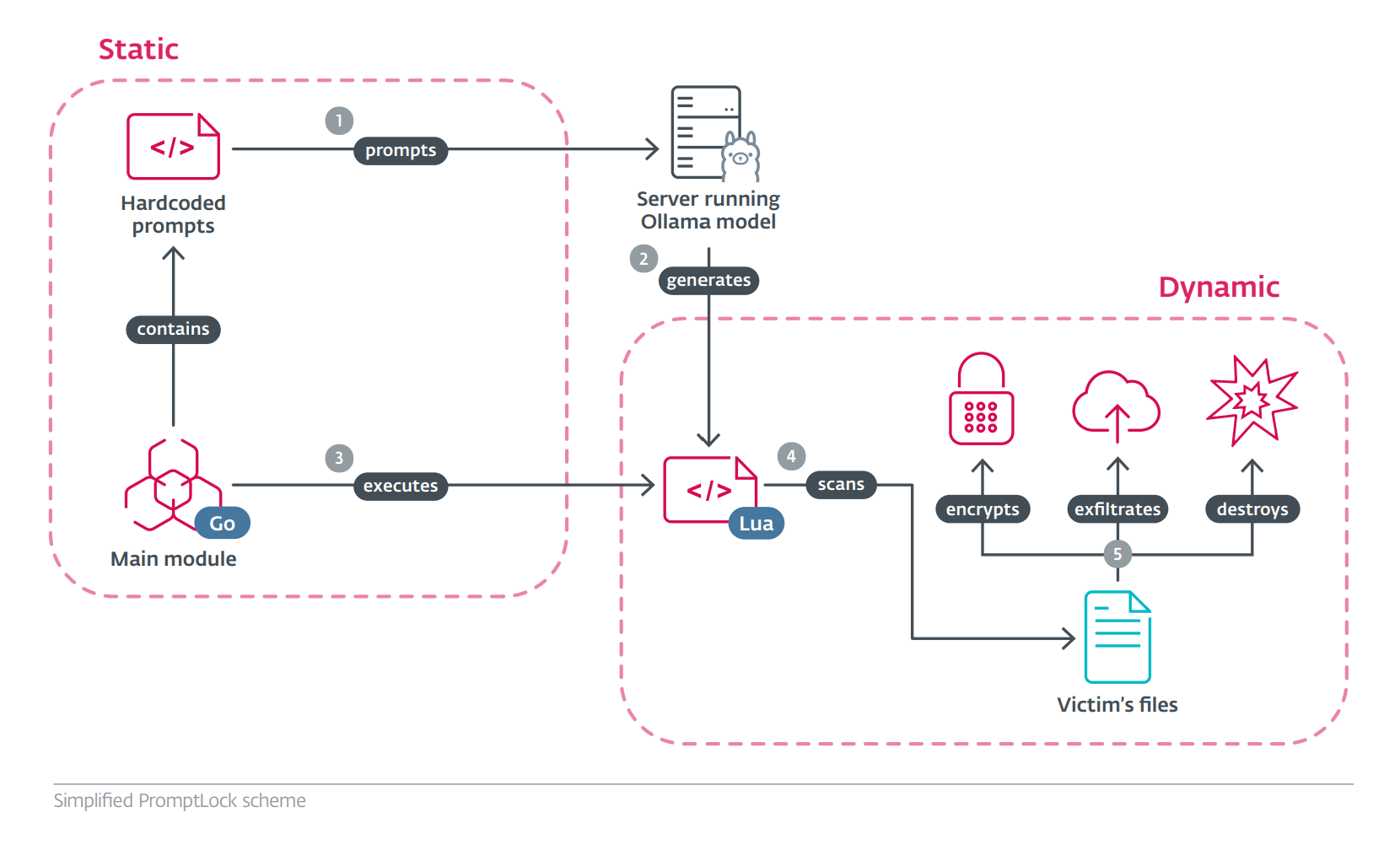
ESET - Promptlock AI Ransomware process detail
Sample takeaways:
- AI-powered malware moved from theory to reality in H2 2025, as ESET discovered PromptLock, the first known AI-driven ransomware, capable of generating malicious scripts on the fly. While AI is still mainly used for crafting convincing phishing and scam content, PromptLock – and the handful of other AI-driven threats identified to this day – signal a new era of threats. What makes PromptLock stand out compared to previous findings that claimed to describe AI threats is its use of an OpenAI model, via the Ollama API, to generate malicious scripts on the fly, which it then executes.
- Based on PromptLock, we expect that AI tools can and will be used to automate various stages of ransomware attacks, from reconnaissance to data exfiltration, and at a speed and scale once thought impossible. In a broader perspective, AI-powered malware represents a new frontier in cyberattacks, as it can be designed to morph and adapt to the environment of each victim.
- After its global disruption in May, Lumma Stealer managed to briefly resurface – twice – but its glory days are most likely over. Detections plummeted by 86% in H2 2025 compared to the first half of the year, and a significant distribution vector of Lumma Stealer – HTML/FakeCaptcha trojan, used in ClickFix attacks – nearly vanished from our telemetry.
- CloudEyE, also known as GuLoader, surged into prominence, skyrocketing almost thirtyfold in ESET telemetry. Distributed via malicious email campaigns, this malware-as-a-service downloader and cryptor is used to deploy other malware, including ransomware, as well as infostealer juggernauts such as Rescoms, Formbook, and Agent Tesla.
- On the ransomware scene, victim numbers surpassed 2024 totals well before year’s end, with ESET Research projections pointing to a 40% year-over-year increase. Akira and Qilin now dominate the ransomware-as-a-service market, while low-profile newcomer Warlock introduced innovative evasion techniques.
- EDR killers continued to proliferate, highlighting that endpoint detection and response tools remain a significant obstacle for ransomware operators. Over the last three months, ESET Research discovered over a dozen new tools of this kind in the wild, mostly used by affiliates of the Akira and Qilin gangs, followed by Warlock.
- H2 2025 also brought an unpleasant flashback to the Petya/NotPetya ransomware, when ESET researchers uncovered HybridPetya – a new derivate of the infamous malware capable of compromising modern UEFI-based systems.
- On the Android platform, NFC threats continued to grow in scale and sophistication, with an 87% increase in ESET telemetry and several notable upgrades and campaigns observed in H2 2025.
- Fraudsters behind the Nomani investment scams have also refined their techniques – we have observed higher-quality deepfakes, signs of AI-generated phishing sites, and increasingly short-lived ad campaigns to avoid detection. In ESET telemetry, detections of Nomani scams grew 62% year-over-year.
Delinea
Title: 2025 State of Ransomware Report
Link: https://delinea.com/resources/2025-ransomware-survey-report
Great for:
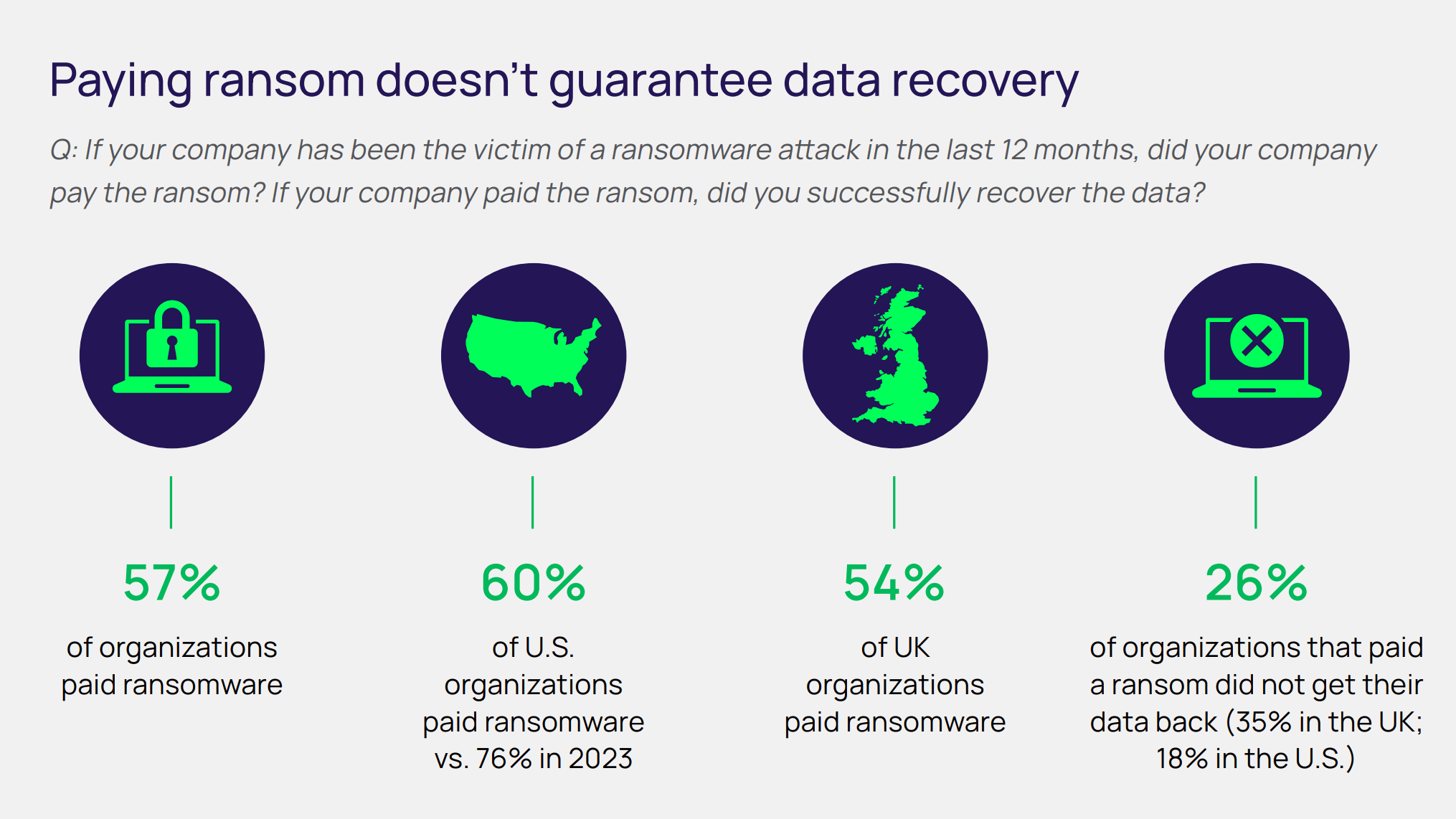
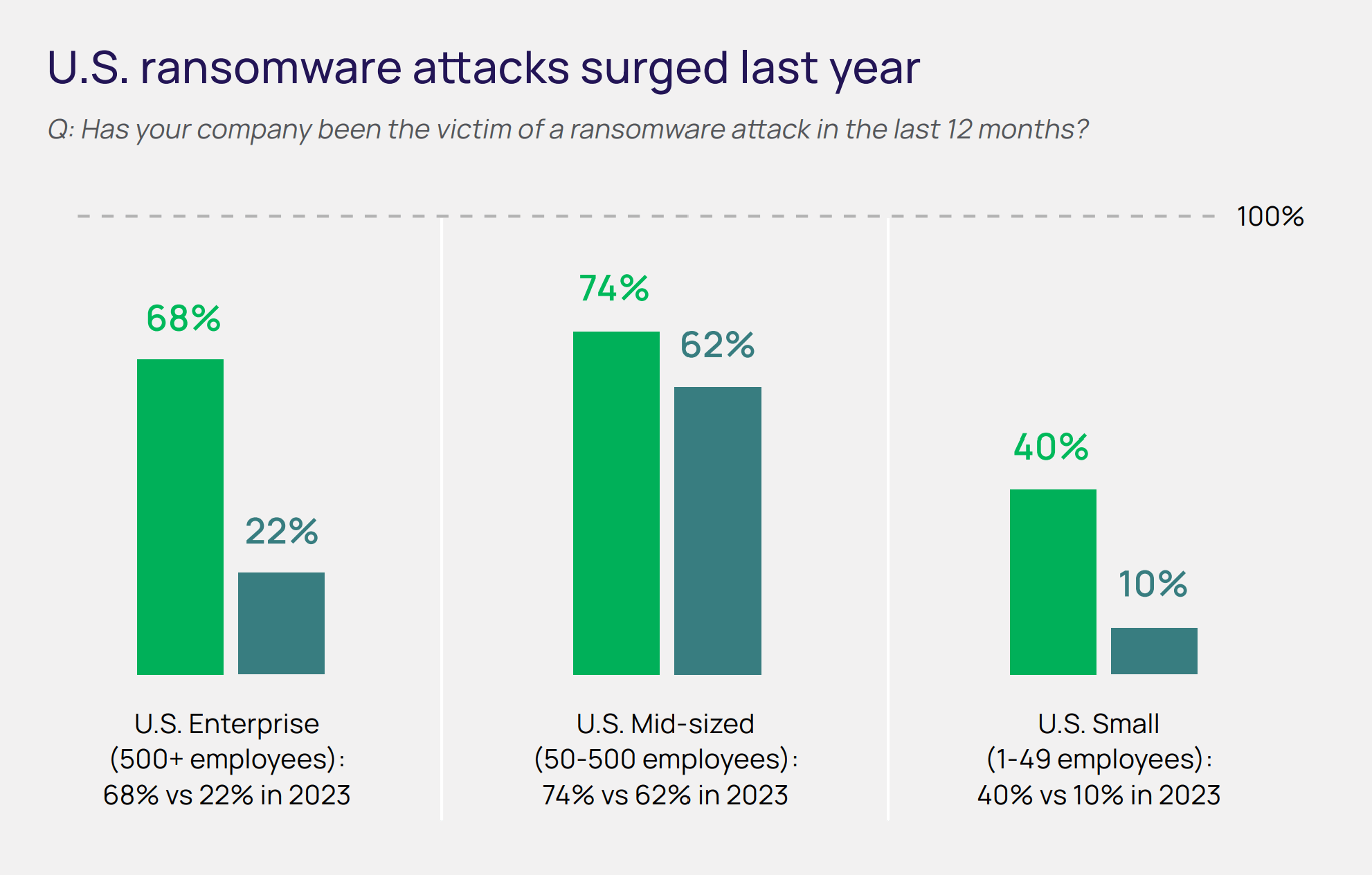
Does a good job of connecting causes and effects in the trends analyzed and suggesting mitigation recommendations. Good quick look at the trends in ransomware and a good reminder of how it has changed and the important shifts organizations need to take in response. Good for a quick look at the trends in ransomware and as a checklist to make sure not leaving any defense measures unattended, 4 out of 5 stars.
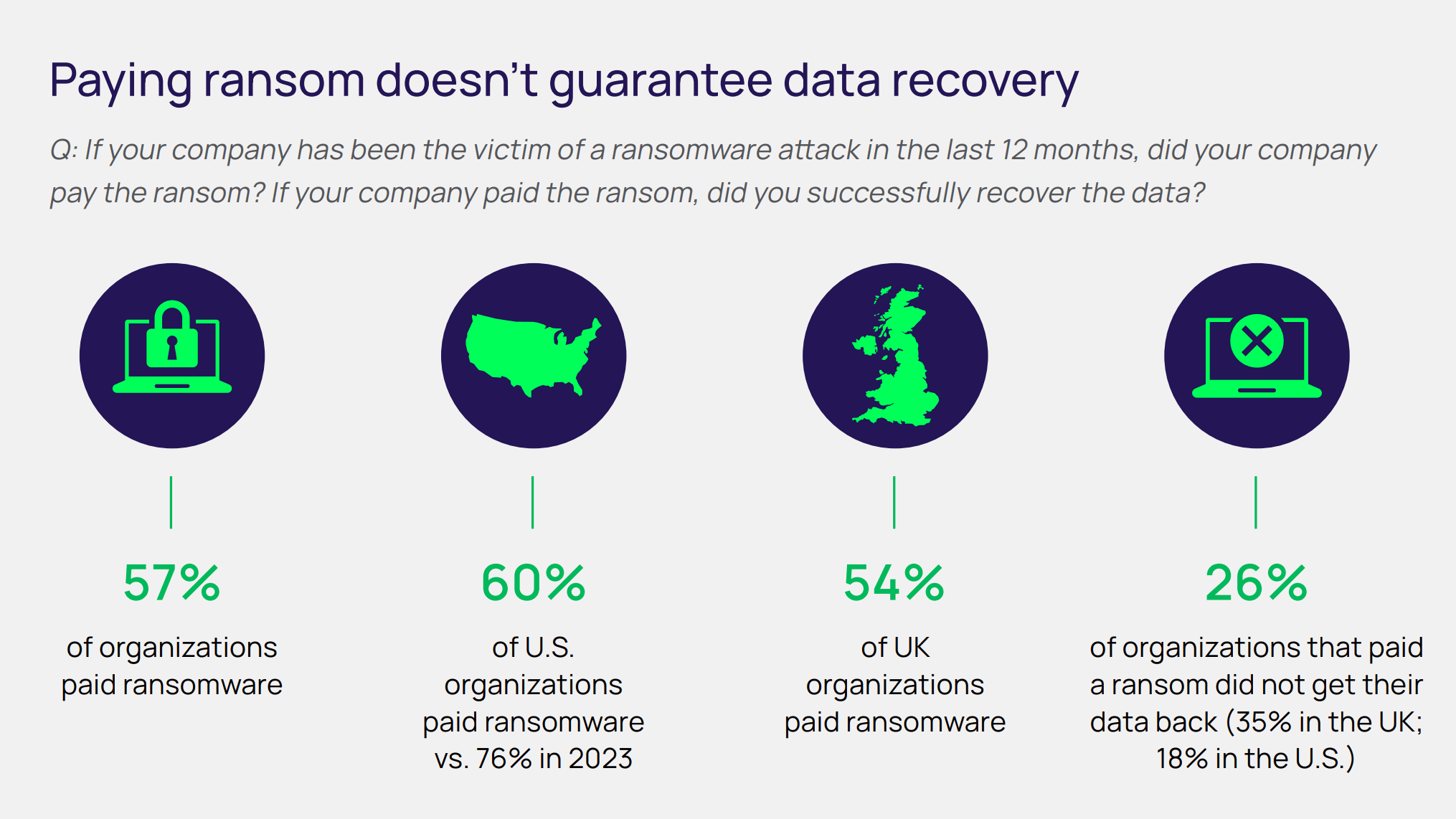
Delinea - Ransom payments results
Sample takeaways:
- Ransomware breaches continue to rise even as fewer victims pay. Ransomware is pervasive, with 69% of firms breached and over a quarter hit more than once. 60% of ransomware now features data theft-related extortion. Fewer (57%) companies are paying
- The top 5 ransomware groups according to Delinea's research:
- RansomHub: A rebranded version of Knight focused on extortion primarily via data theft is a major RaaS group.
- LockBit: A notorious and prolific RaaS group since 2019, which uses sophisticated encryption techniques. It persists in a reduced capacity, despite arrests and takedowns
- Play: Active since 2022, it uses intermittent encryption as part of its double extortion tactics, which speeds up the scrambling of victims’ files
- Akira: An aggressive group which appeared in 2023 and is affiliated with the defunct Conti group
- Hunters International: Another RaaS group, notable for its sophisticated malware and believed to be an offshoot of the dismantled Hive ransomware group
- Most ransomware today includes data theft extortion. Delinea researchers indicate that most of the main ransomware groups now follow a double extortion model. This is corroborated by this study, with 60% of ransomware victims surveyed claiming they experienced a data breach, and 85% stating they were threatened with having their data published or sold. If extortion is now predominantly focused on information theft, then backing up is a less useful mitigation strategy if used in isolation. Organizations must instead have a variety of defensive techniques at their disposal. The emphasis must be on proactive, preventative security that blocks data theft from happening in the first place.
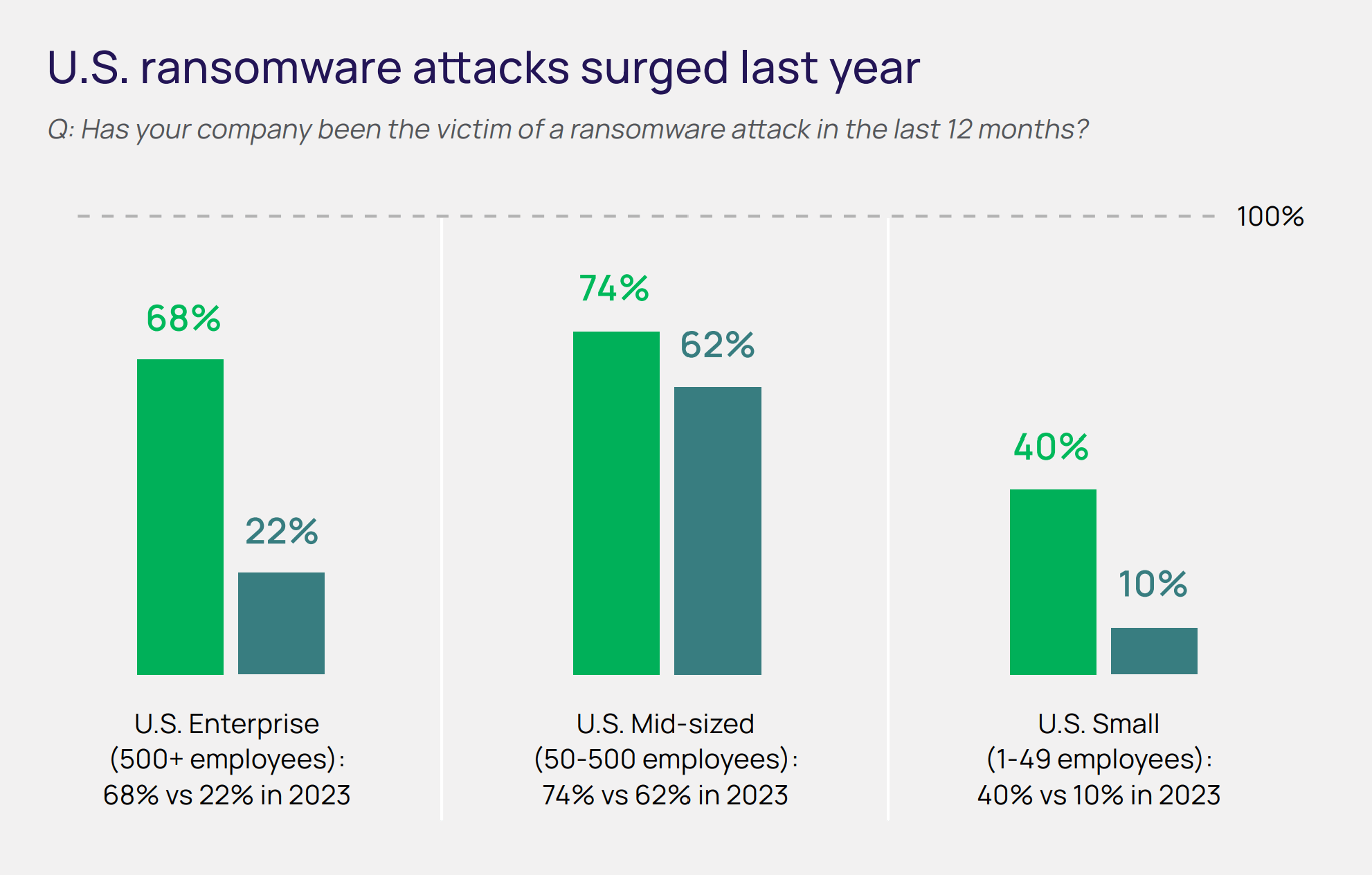
Delinea - Increase in ransomware attacks by company size
Fortinet
Title: 2025 Global Threat Landscape Report
Link: https://www.fortinet.com/resources/reports/threat-landscape-report
Great for:
Very practical, trends-to-action connected thought process presentation of their information which helps to readily convert the takeaways from the report into immediate improvements that could be made. Includes good and unique observations from the dark web and malicious AI usage methods that is worth a look. Overall does a good job of covering many specific threats by name and how they operate. 5 out of 5 stars.

Fortinet - Report cover
Sample takeaways:
- Reconnaissance is surging. Cybercriminals are deploying automated scanning at a global scale. Active scanning in cyberspace reached unprecedented levels in 2024, rising by 16.7% worldwide. FortiGuard Labs observed billions of scan attempts each month, equating to 36,000 scans per second, revealing an intensified focus on mapping exposed services, such as SIP and RDP, and OT/IoT protocols like Modbus TCP. Tools like SIPVicious and commercial scanning tools are weaponized to identify soft targets before patches can be applied, signaling a significant “left-of-boom” shift in adversary strategy.
- CaaS is fueling initial access at scale. The underground economy for stolen credentials and direct corporate access has exploded. FortiGuard Labs observed a 42% increase in compromised credentials for sale and a rise in Initial Access Broker (IAB) activity offering VPNs, RDPs, and admin panels. Infostealers like Redline and Vidar drove a 500% increase in credential logs on darknet forums.
- Post-exploitation tactics are getting stealthier. Despite the number of CVEs growing 39% from 2023 to 2024, zero-day attacks only account for a small percentage of observed threats. Cybercriminals increasingly “live off the land,” using trusted tools and protocols to escalate privileges and persist undetected. FortiGuard Labs has identified advanced post-compromise behaviors, including Active Directory (AD) manipulation (such as DCShadow and DCSync), RDP-based lateral movement, and encrypted C2 via DNS and SS.
- A call to action: "shift left, act fast, and reduce exposure" because as attackers invest heavily in automation, reconnaissance, and scalable operations. Their playbooks emphasize speed, stealth, and scalability, while far too many organizations remain overburdened with reactive patch cycles and static security strategies. Defenders must shift from traditional threat detection toward Continuous Threat Exposure Management (CTEM) to counter this asymmetry. This proactive approach emphasizes the following:
- Continuous attack surface monitoring
- Real-world emulation of adversary behavior
- Risk-based prioritization of remediation
- Automation of detection and defense responses
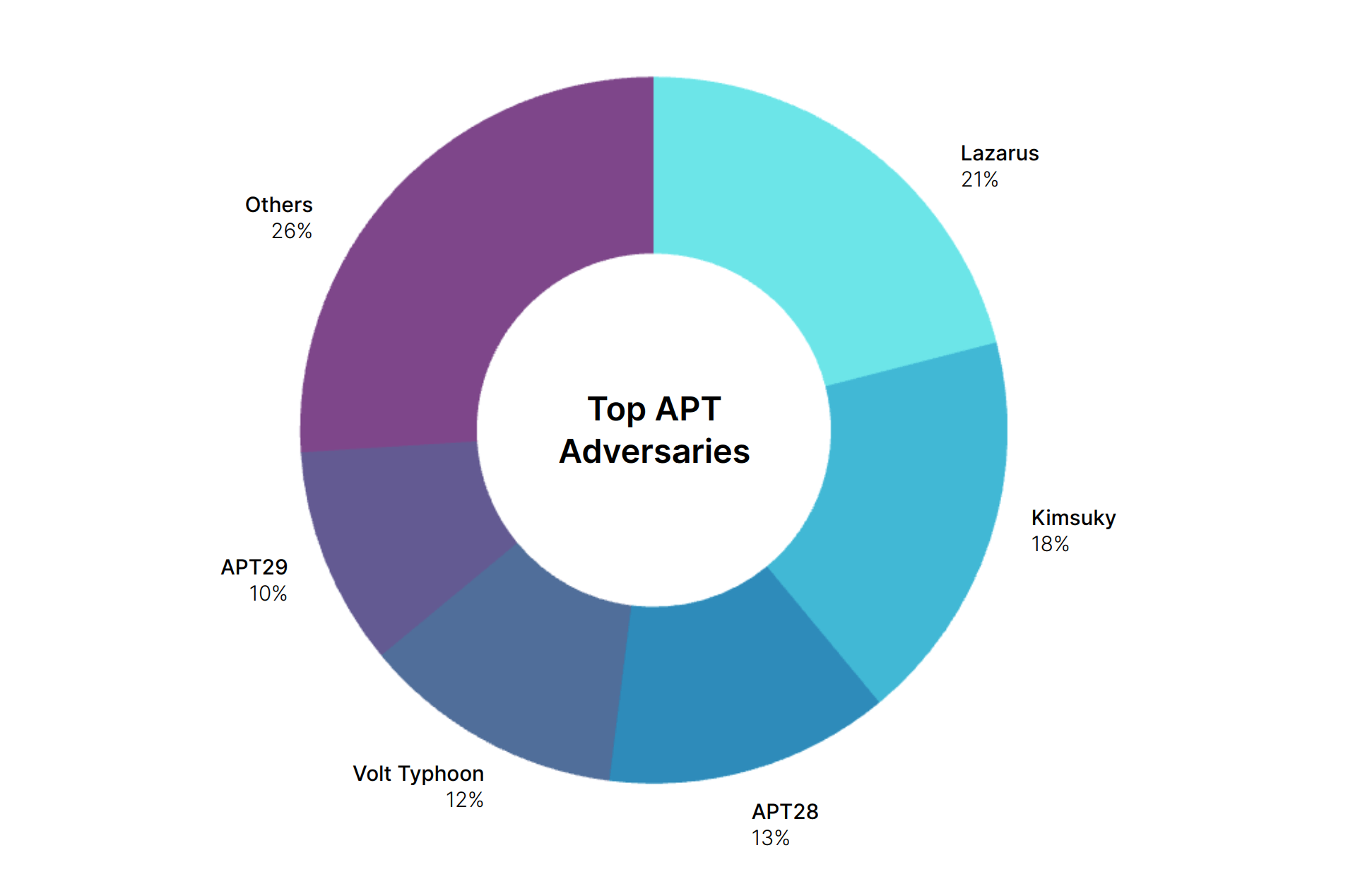
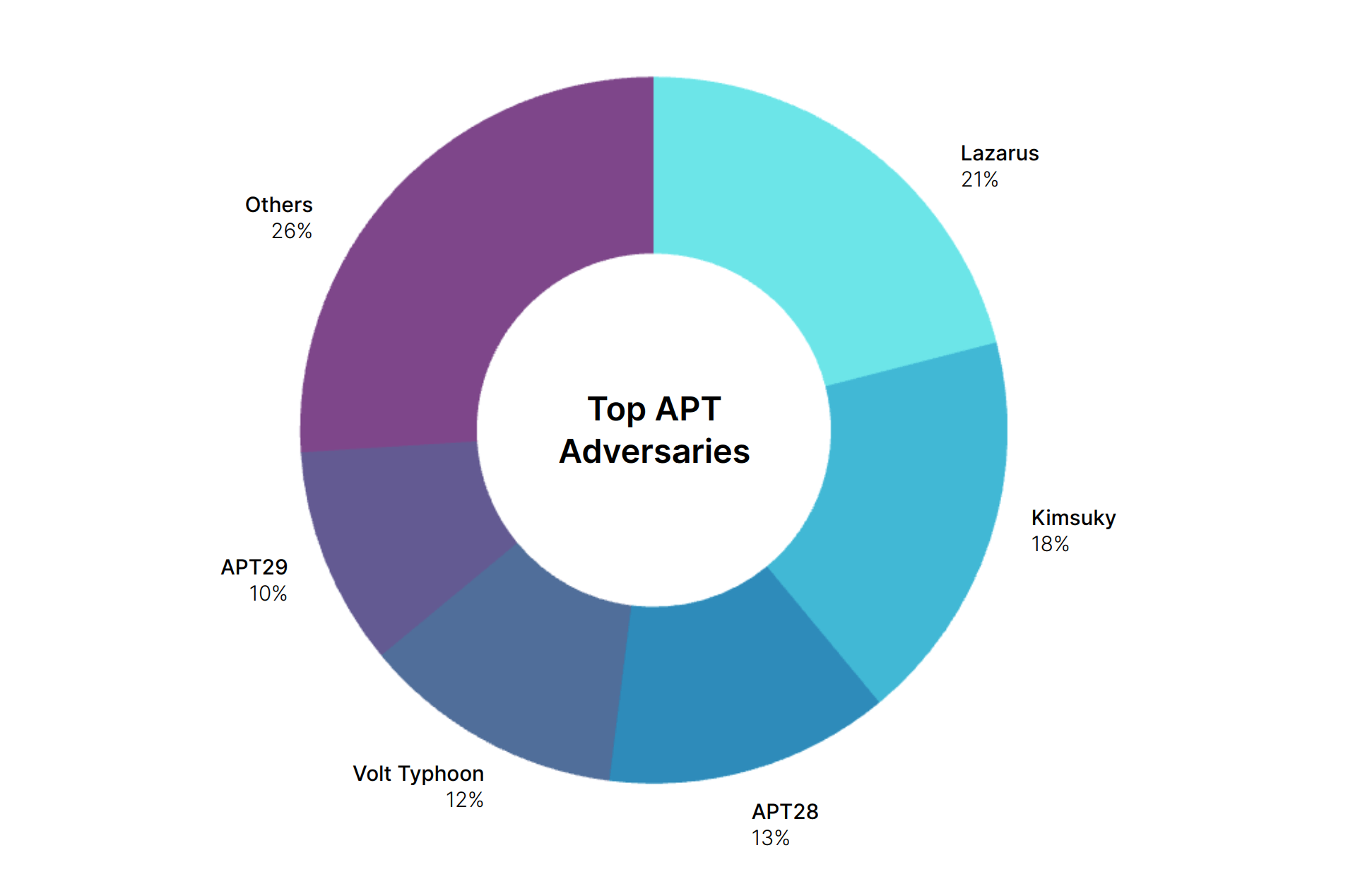
Fortinet - Top APT groups
Sophos
Title: Sophos Annual Threat Report: Cybercrime on Main Street 2025
Link: https://www.sophos.com/en-us/blog/the-sophos-annual-threat-report-cybercrime-on-main-street-2025
Great for:
Comes from a perspective focusing on small and medium businesses, which is helpful for many practitioners with more limited mitigation budgets.
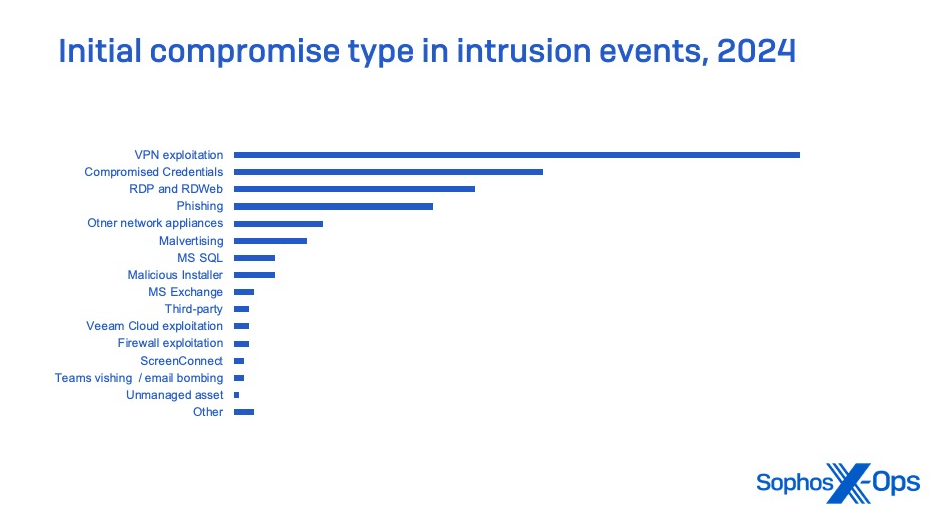
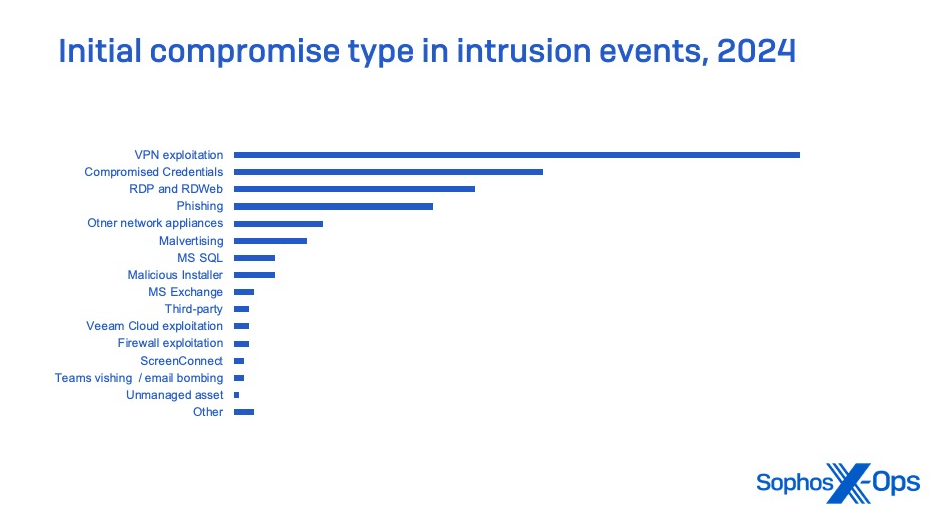
Sophos - Initial compromise types
Sample takeaways:
- Compromised network edge devices—firewalls, virtual private network appliances, and other access devices—account for a quarter of the initial compromises of businesses in cases that could be confirmed from telemetry, and is likely much higher.
- Software-as-a-service platforms, which were widely adopted by organizations during the COVD pandemic to support remote work and to improve overall security posture, continue to be abused in new ways for social engineering, initial compromise, and malware deployment.
- Business email compromise activity is a growing proportion of the overall initial compromises in cybersecurity incidents—leveraged for malware delivery, credential theft, and social engineering for a variety of criminal purposes.
- One of the drivers of business email compromise is the phishing of credentials with adversary-in-the-middle multifactor authentication MFA) token capture, a constantly evolving threat.
- Fraudulent applications carrying malware, or tied to scams and social engineering through SMS and messaging applications, lead to mobile threats for small and midsize businesses.
- Whether simply misconfigured, using weak credential policies, or running on vulnerable software or firmware, systems on the network edge are the initial point of compromise for over a third of all incidents involving intrusion into smaller organizations. Obsolete and unpatched hardware and software constitutes an ever-growing source of security vulnerabilities, a phenomenon referred to as “digital detritus.ˮ
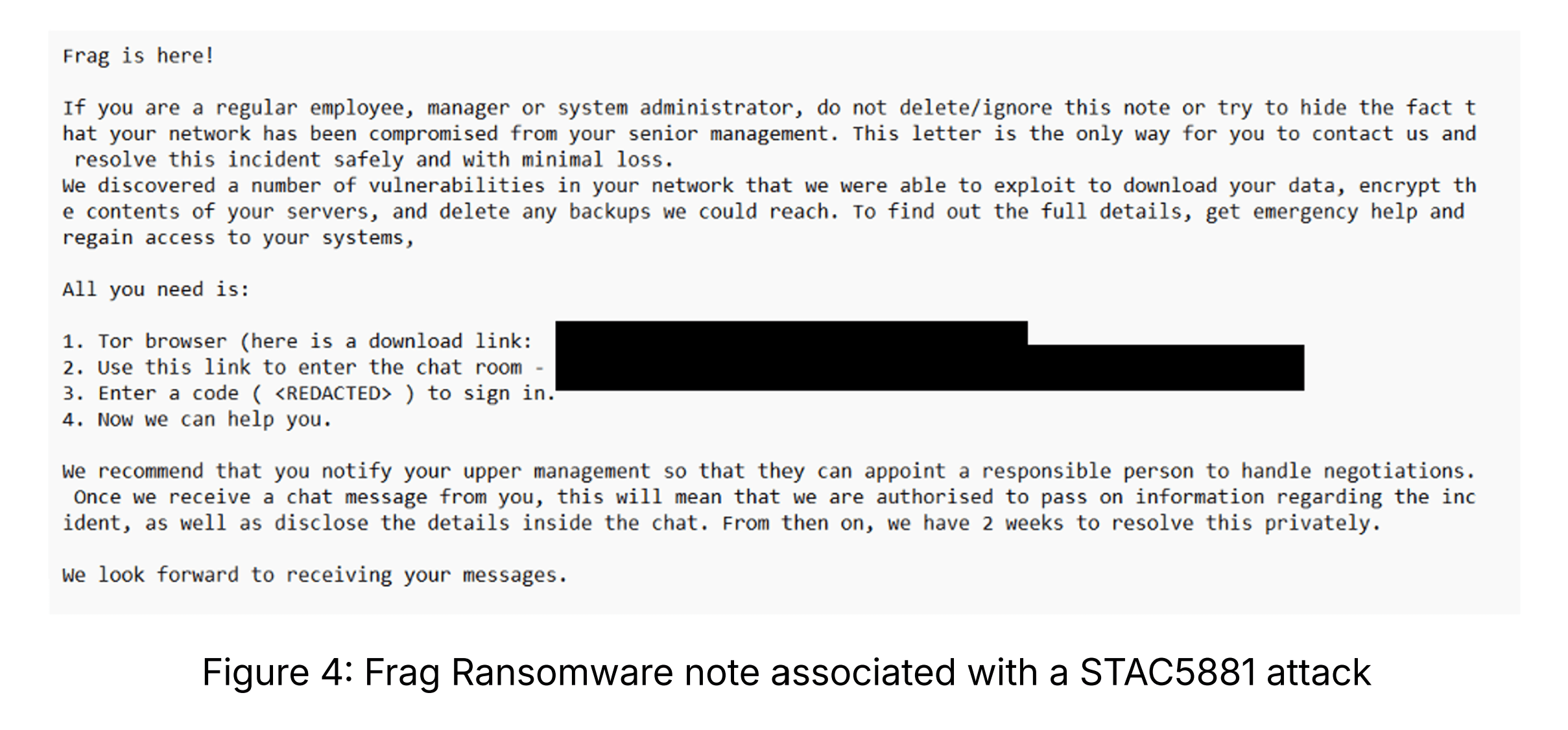
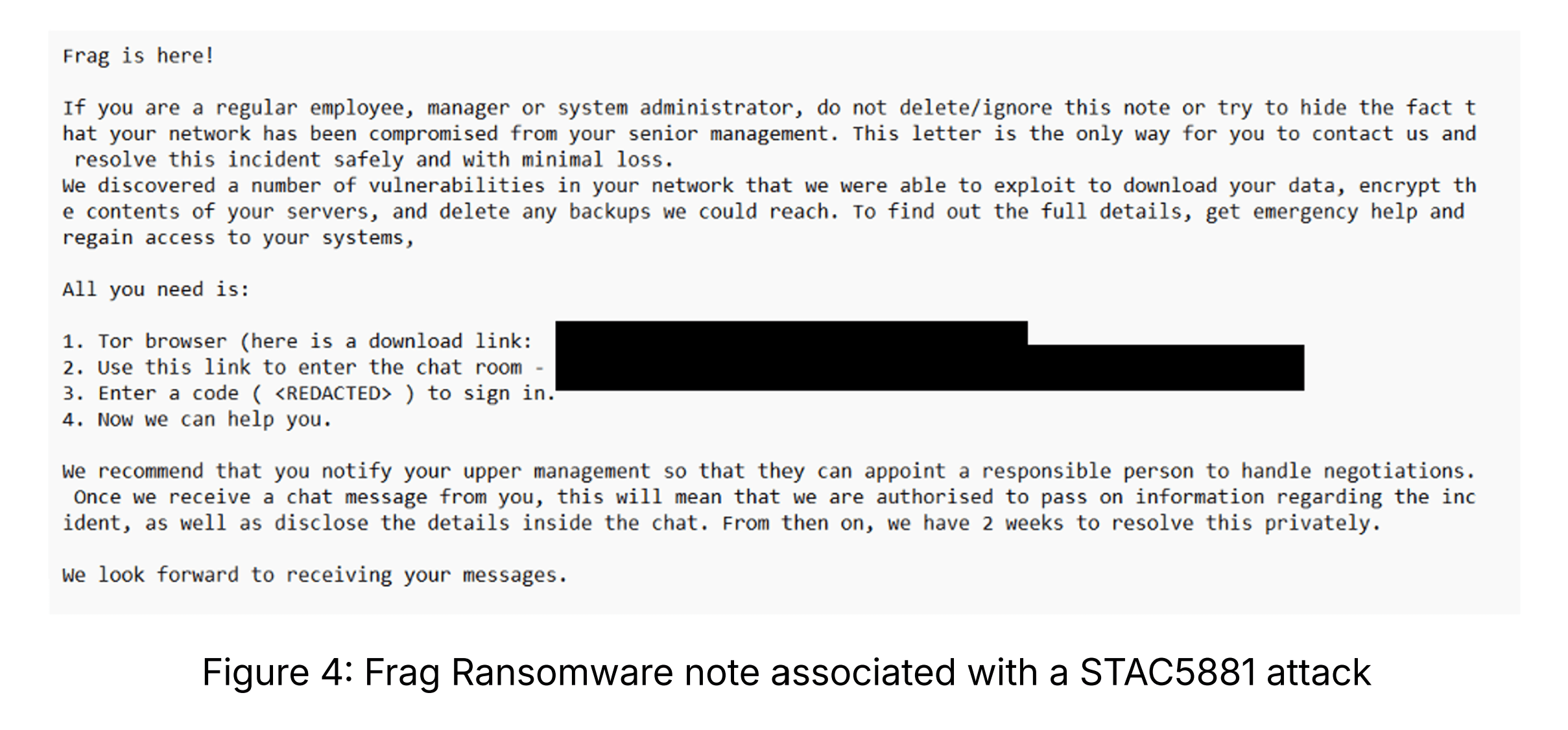
Sophos - Sample ransomware note
Accenture
Title: State of Cybersecurity Resilience 2025
Link: https://www.accenture.com/us-en/insights/security/state-cybersecurity-2025
Great for:
It has a lot of generic "executive survey" input and discussion which always feels more on the marketing speak side than being super practical, but it does actually point to good directions of change and action for organizations to pay attention to so there is value there. Once you get past the "consultant speak" there is a great deal of practical and valuable advice in the report. A lot of time is spent discussing AI risks and defining the challenges, and a good internal checklist for an organization from this doc of everything an org should do to stay ahead of AI risks. 4.5 out of 5 stars and worth a look.
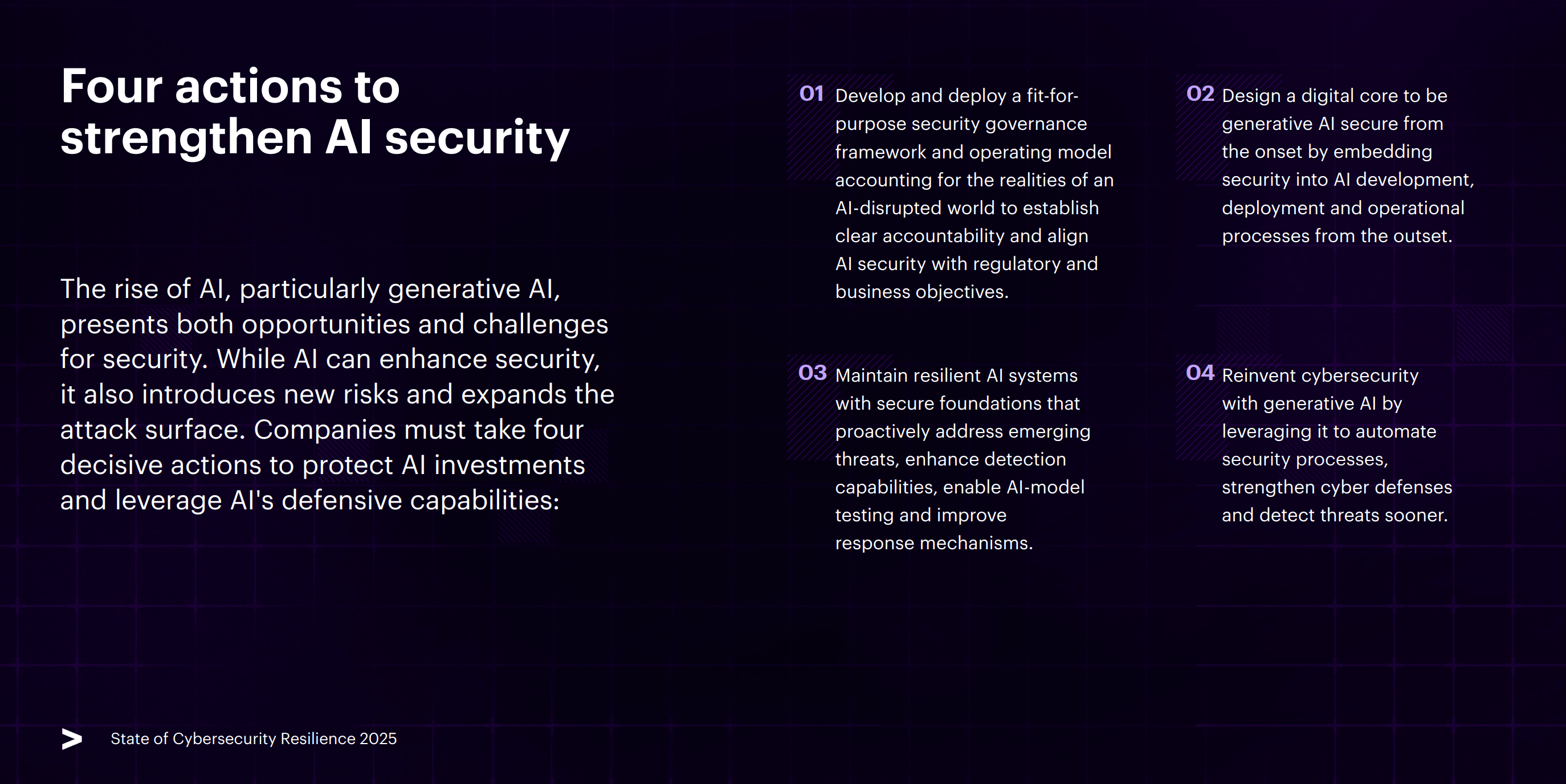
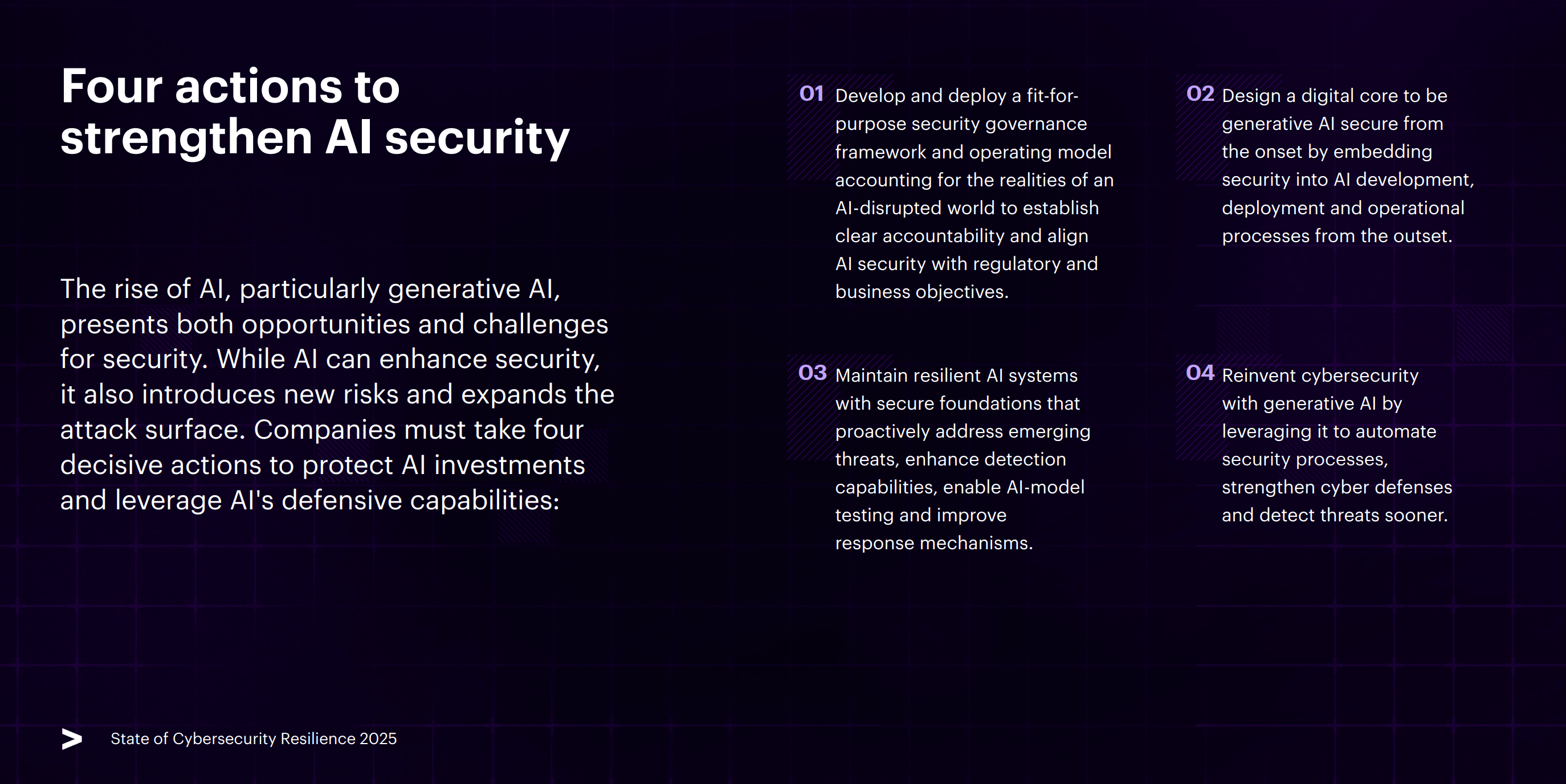
Accenture - Actions to strengthen AI exposure
Sample takeaways:
- The rise of AI, particularly generative AI, presents both opportunities and challenges for security. While AI can enhance security, it also introduces new risks and expands the attack surface. Companies must take four decisive actions to protect AI investments and leverage AI's defensive capabilities:
- Develop and deploy a fit-for- purpose security governance framework and operating model accounting for the realities of an AI-disrupted world to establish clear accountability and align AI security with regulatory and business objectives.
- Design a digital core to be generative AI secure from the onset by embedding security into AI development, deployment and operational processes from the outset.
- Maintain resilient AI systems with secure foundations that proactively address emerging threats, enhance detection capabilities, enable AI-model testing and improve response mechanisms.
- Reinvent cybersecurity with generative AI by leveraging it to automate security processes, strengthen cyber defenses and detect threats sooner.
- Cloud misconfigurations are one of the biggest risks to AI security, giving attackers an entry point to manipulate training data, extract sensitive information and compromise AI models. The best defense is embedding security from the start—not treating it as an afterthought. Establish dedicated and segmented Secure AI environments, which can facilitate prototyping and experimentation at speed under controlled conditions.
- Emerging technologies such as serverless architectures, low-code/no-code platforms and generative AI-powered applications introduce new risks that traditional security frameworks may not fully address.
Mandiant / Google
Title: M-Trends 2025 Report
Link: https://cloud.google.com/security/resources/m-trends
Great for:
Good basic overview of trends, coupled with some relevant deep dives, including a good look into malicious North Korean IT worker scams and Infostealers, for example. Has some good reading on a history of the most exploited vulnerabilities in its time period, but the reading is dry. Lots of good basic facts like on access factors, dwell times etc. knowing baselines. It's chockfull of definitions and helpful summaries, so it's a good refresher or for anyone adjacent to the industry. It's a good read overall to get a good understanding of the cybersecurity landscape, 5 out of 5 stars, recommended to read.
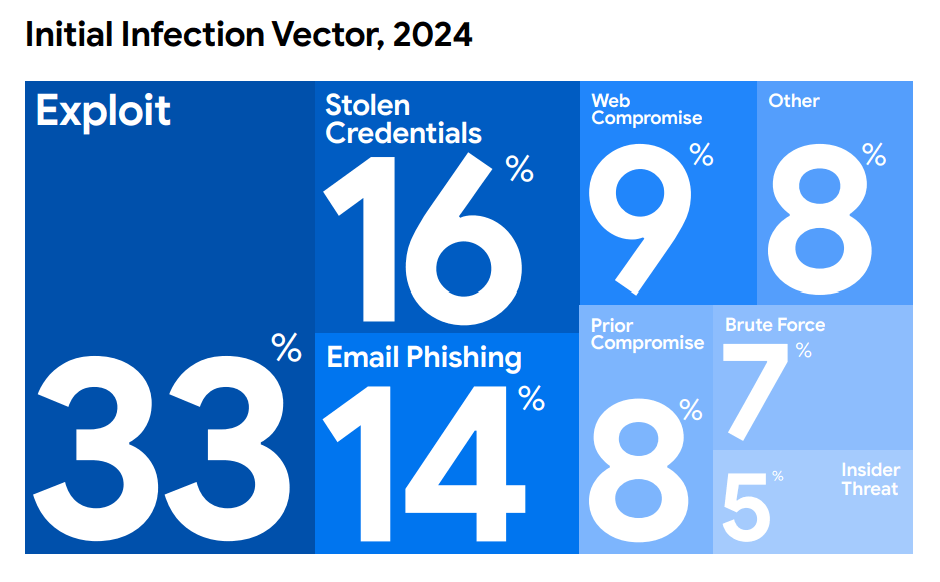
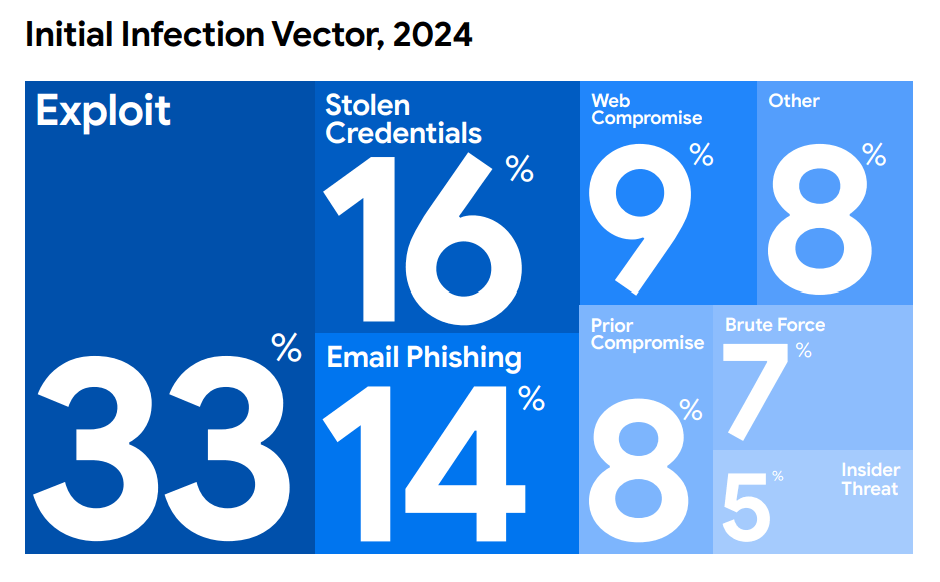
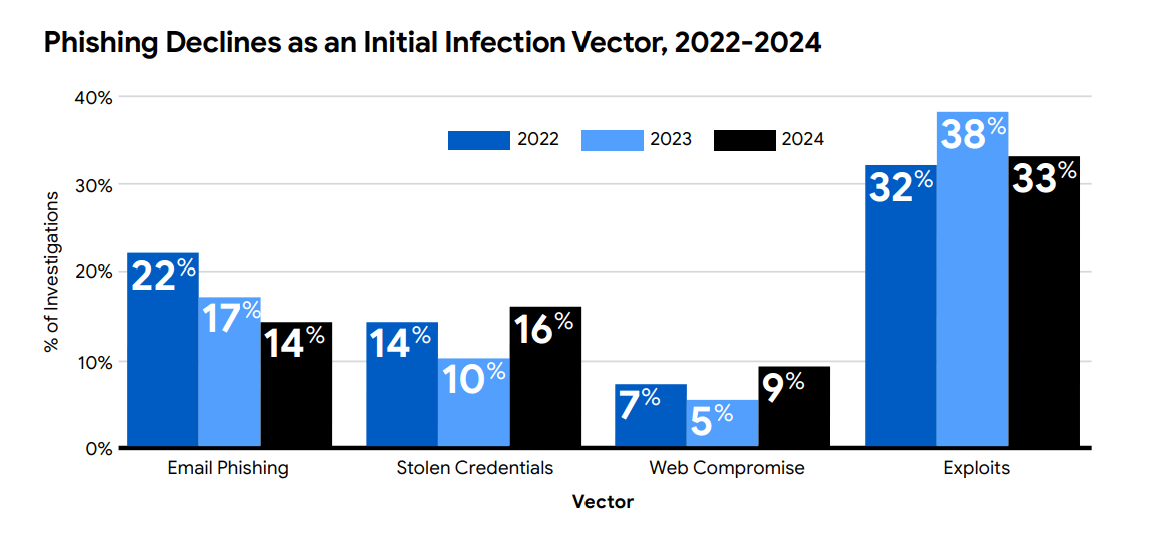
Mandiant - Initial access vectors
Sample takeaways:
- A key takeaway from M-Trends 2025 is that attackers are seizing every opportunity to further their objectives. One way they are doing this is through the use of infostealer malware, which is increasingly being used to enable intrusions using stolen credentials.
- Another growing trend is the targeting of unsecured data repositories, which is brought on by the lack of basic security hygiene. Additionally, attackers are exploiting the gaps and risks introduced as organizations continue their migrations to the cloud.
- Mandiant has tracked a threat cluster it refers to as UNC5267, which represents the DPRK’s efforts to place thousands of its citizens in countries outside of North Korea to pose as remote IT contractors for Western companies. These citizens, commonly referred to as “DPRK IT workers,” are directed to seek employment in high-tech companies headquartered among Western countries and funnel salaries back to the DPRK.
- DPRK IT workers most commonly work through job placement services and recruiters but have been observed pursuing direct employment as well. Their operations are supported through a broad network of false or stolen identities and third-party accomplices. Outside the fraudulent activity necessary to place a DPRK IT worker in a Western organization, Mandiant identified evidence of direct malicious activity in fewer than five investigations in 2024. However, the access to corporate infrastructure necessary for the high-tech jobs that DPRK IT workers pursue places organizations at heightened risks of extortion, espionage, data theft, and disruption.
- Throughout 2024, Mandiant observed attackers increasingly eschewing traditional on-premises network infiltration in favor of targeting cloud-based stores of centralized authority, such as single sign-on (SSO) web portals. When successful, these centralized authorities could grant a threat actor broad-scale access to an environment. In the past, attackers would have to compromise a single system and move laterally through an environment before finally acquiring high-privilege access, such as domain admin credentials. The centralized nature of cloud identity and access management (IAM) technologies can provide a shortcut with fewer opportunities for exposure. High-value accounts can often be used to bridge access between cloud and on-premises environments.
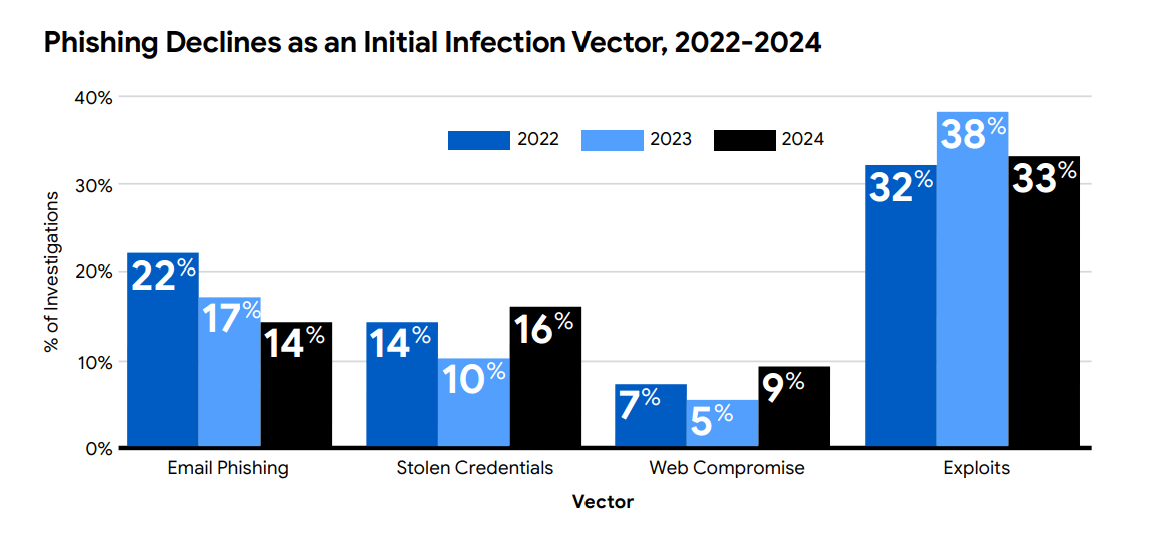
Mandiant - Phishing declines as an asset vector
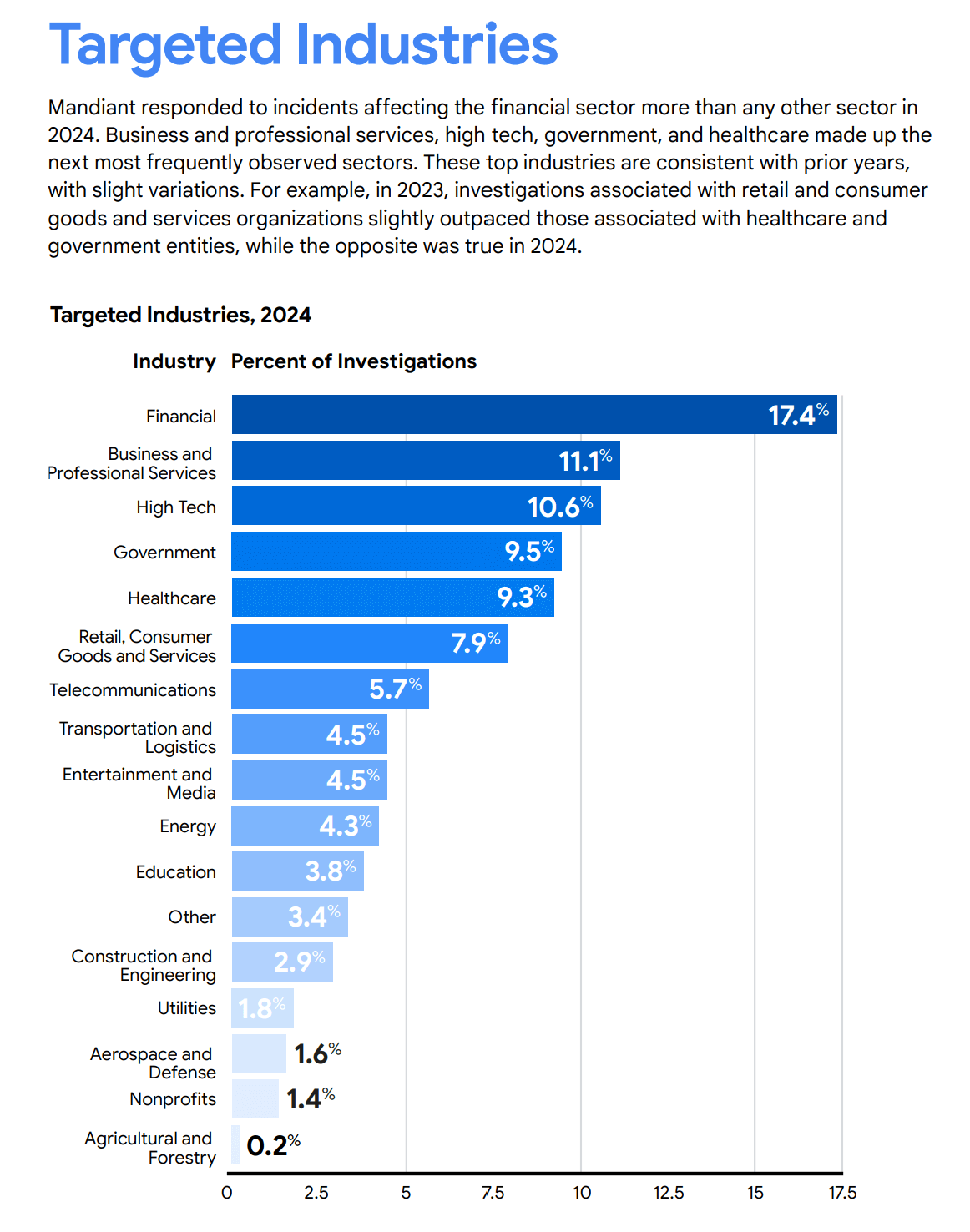
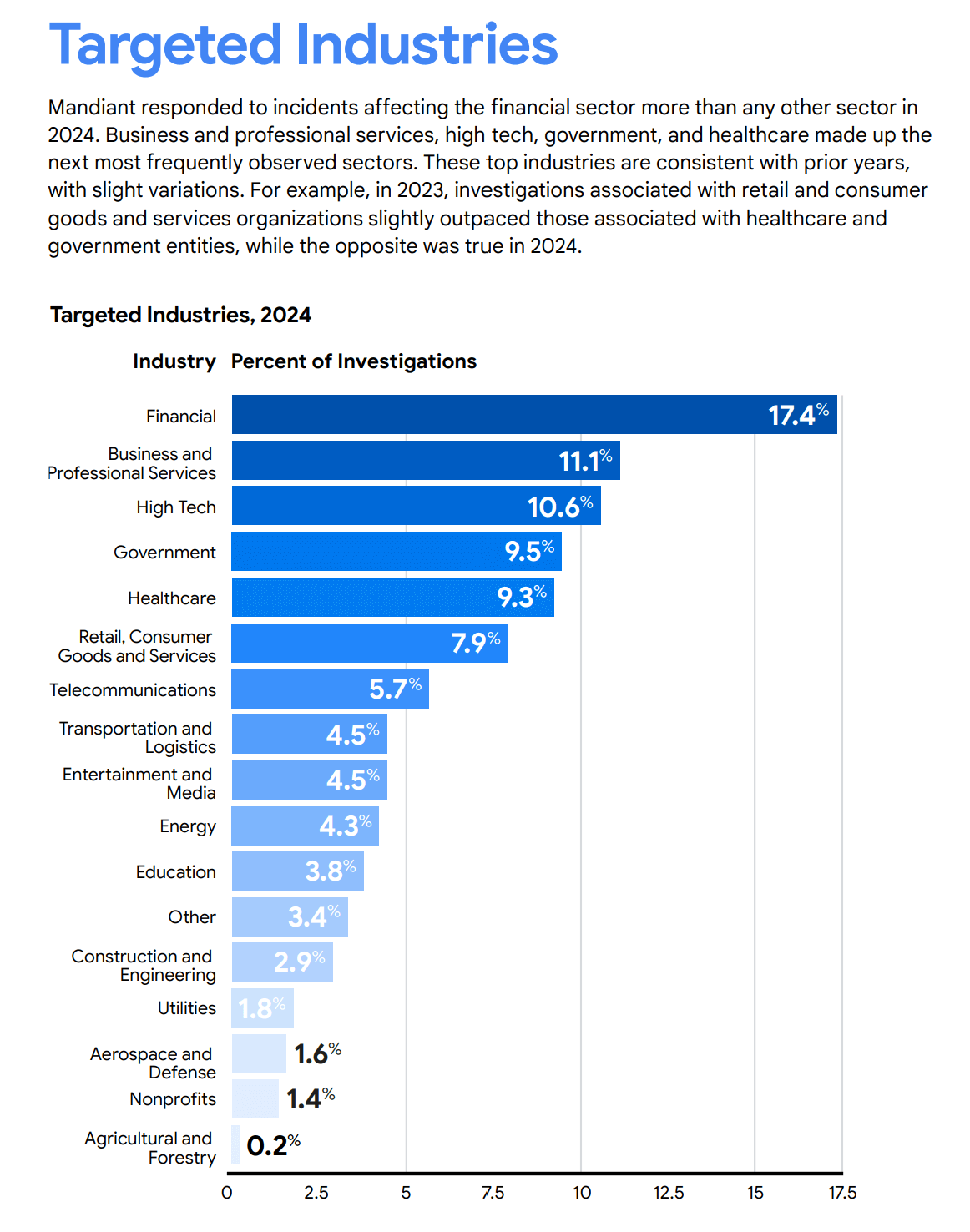
Mandiant - Targeted industries
ENISA
Title: ENISA Threat Landscape 2025
Link: https://www.enisa.europa.eu/publications/enisa-threat-landscape-2025
Great for:
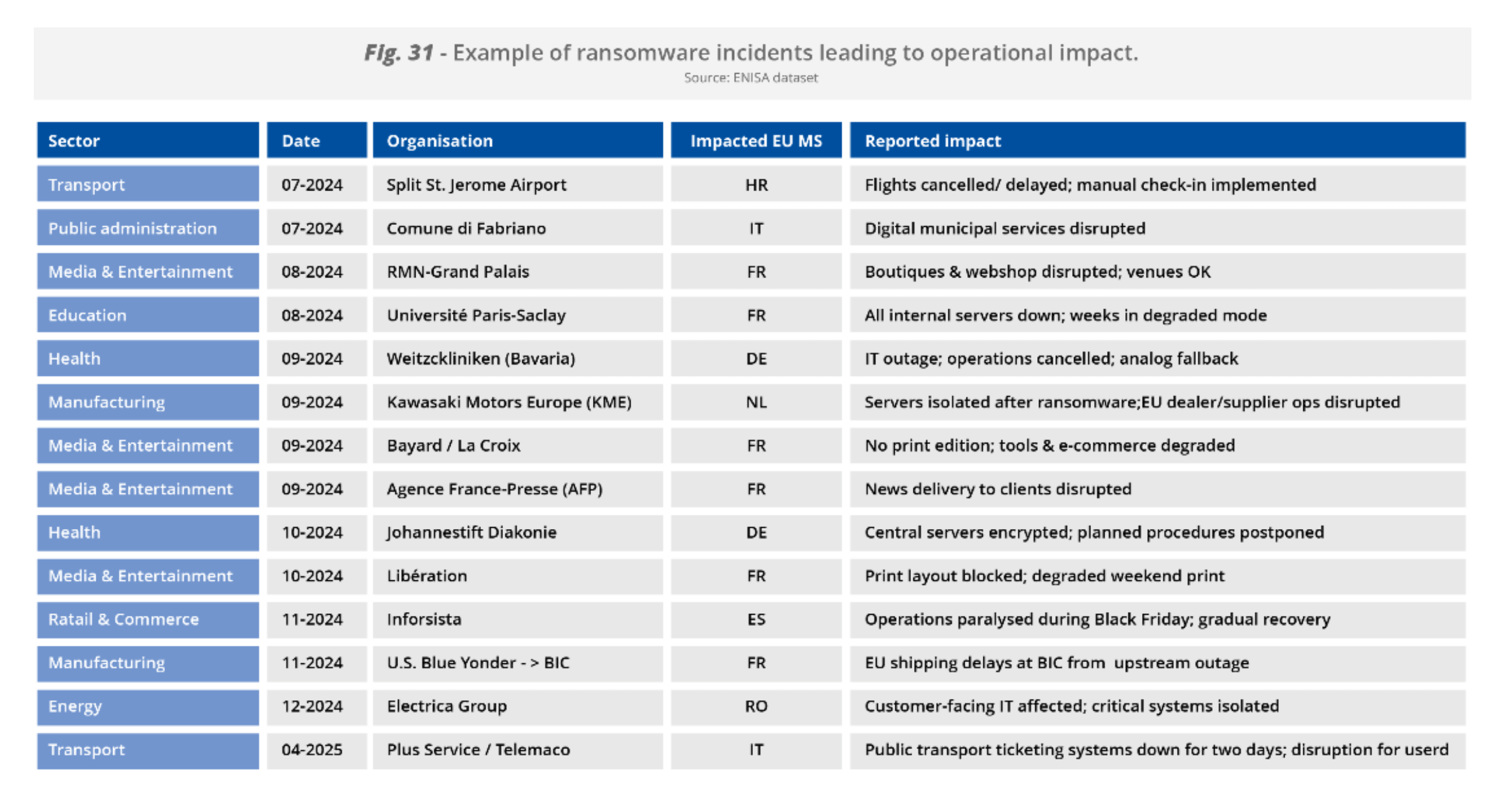
Understanding threats and risks by their scale and impact via the European dataset and experience. The dataset really does seem to differ compared to the global experience (showing a lot more hackitivism and DDoS attacks, for example) so it is very interesting info to compare. The presentation is very cut and dry so it's ideal for gathering insight quickly free of corporate marketing speak. It does a very good job of going through many case studies at a surface level, so it's a good history of what occurred in 2025.
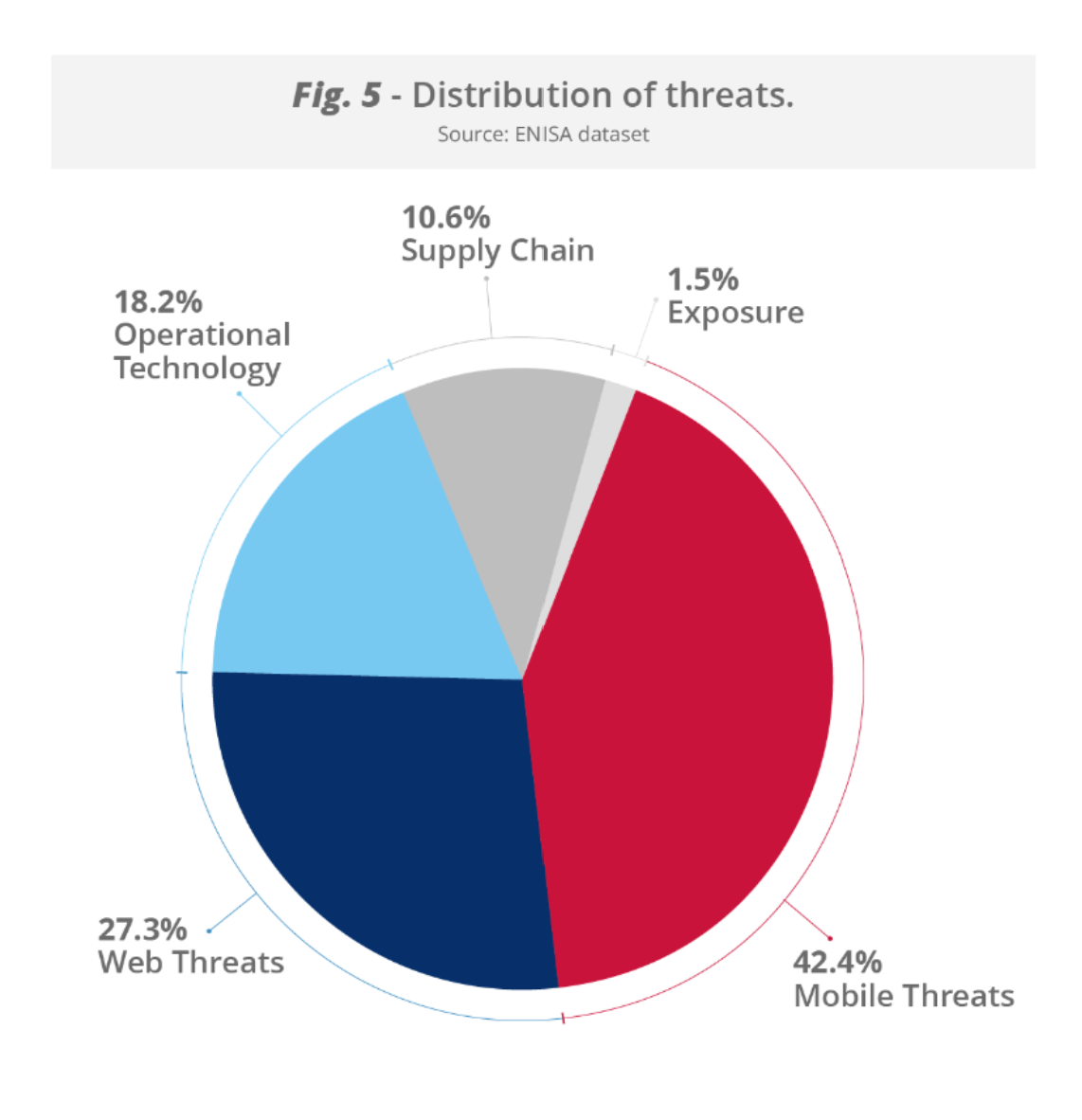
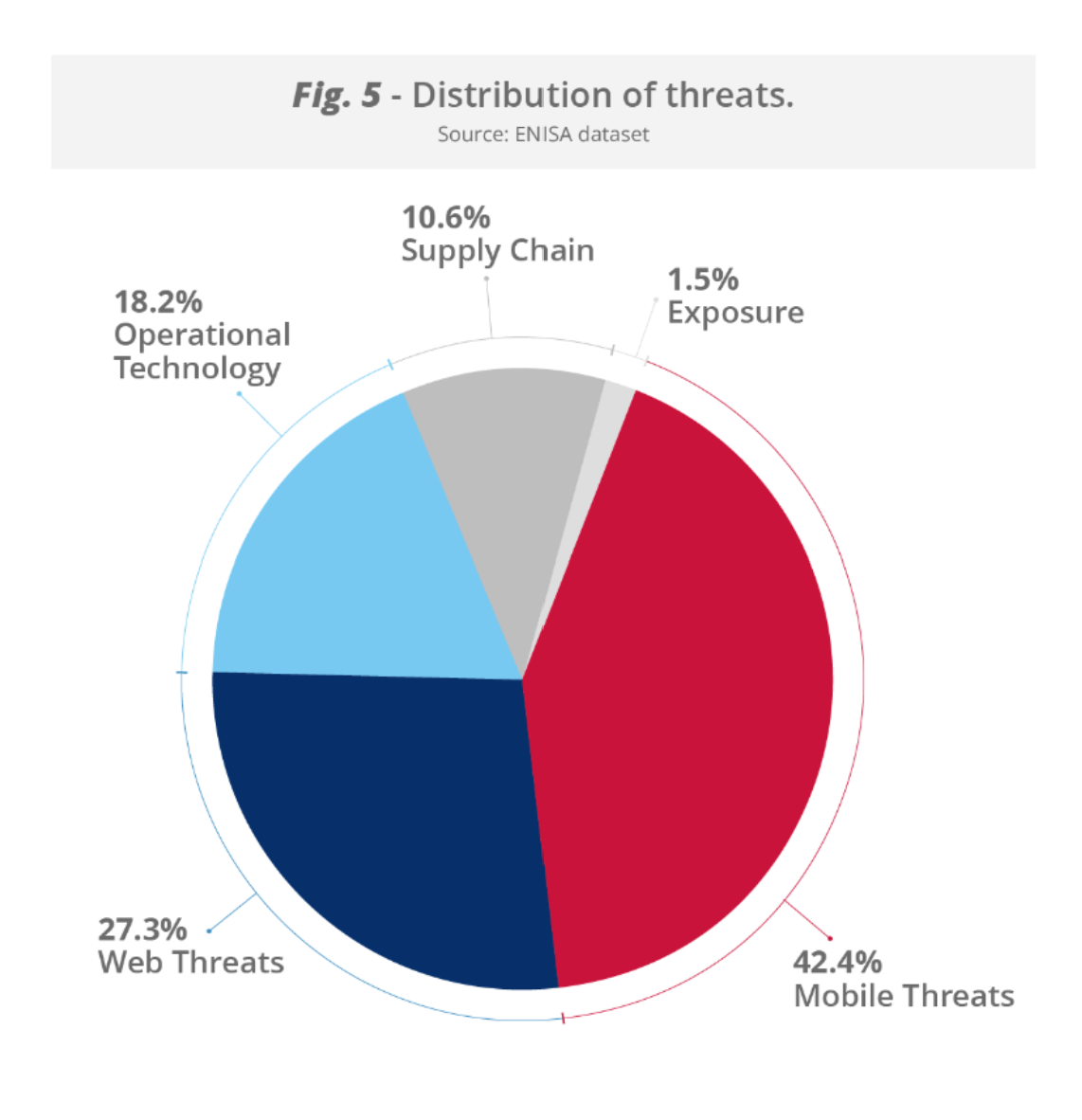
ENISA - Distribution of threat categories
Sample takeaways:
- State-aligned threat groups intensified their long-term cyberespionage campaigns against the telecommunications, logistics networks and manufacturing sectors in the EU, demonstrating advanced tradecraft such as supply chain compromise, stealthy malware frameworks and abuse of signed drivers.
- Hacktivist activity continues to dominate reporting, representing almost 80% of recorded incidents and driven primarily by low-level distributed denial-of-service operations. While overall resulting in very low impact, these campaigns demonstrate how low-cost tools are scaled for ideology-driven operations.
- Sectoral targeting patterns reinforce the EU’ systemic exposure. Public administration networks remain the primary focus (38%), notably for hacktivists and state-nexus intrusion sets, while transport emerged as a high-value sector, particularly maritime and logistics. Aviation and freight operations have faced ransomware disruptions, while digital infrastructure and services remain strategic targets for both cyberespionage and ransomware operators.
- Social engineering tactics remain the primary entry point for threat actors, with phishing (including vishing, malspam, and malvertising) accounting for about 60% of observed cases.
- Exploitation of vulnerabilities (21.3%) remains a prevalent intrusion vector, followed by botnets (9.9%). Malicious applications represent 8%, showing that compromised or trojanised software and applications continue to play a role in system intrusions, while unauthorised access by insider threats (0.8%) contribute smaller but still relevant shares.
- Abuse of cyber dependencies have also intensified, as shown by compromises in open-source repositories, malicious browser extensions and breaches of service providers, amplifying risk throughout interconnected digital ecosystems.
- By early 2025, AI- supported phishing campaigns reportedly represented more than 80 percent of observed social engineering activity worldwide, with adversaries leveraging jailbroken models, synthetic media and model poisoning techniques to enhance their operational effectiveness.
- Cyber threat activity is likely to further intensify along three dimensions: convergence, automation and industrialisation. AI will accelerate cycles of offensive innovation, enabling rapid campaign development and more effective deception techniques. Abuse of cyber dependencies will remain a strategic priority, while the persistence of hacktivism and disinformation campaigns will continue to influence public perception and policy debates.
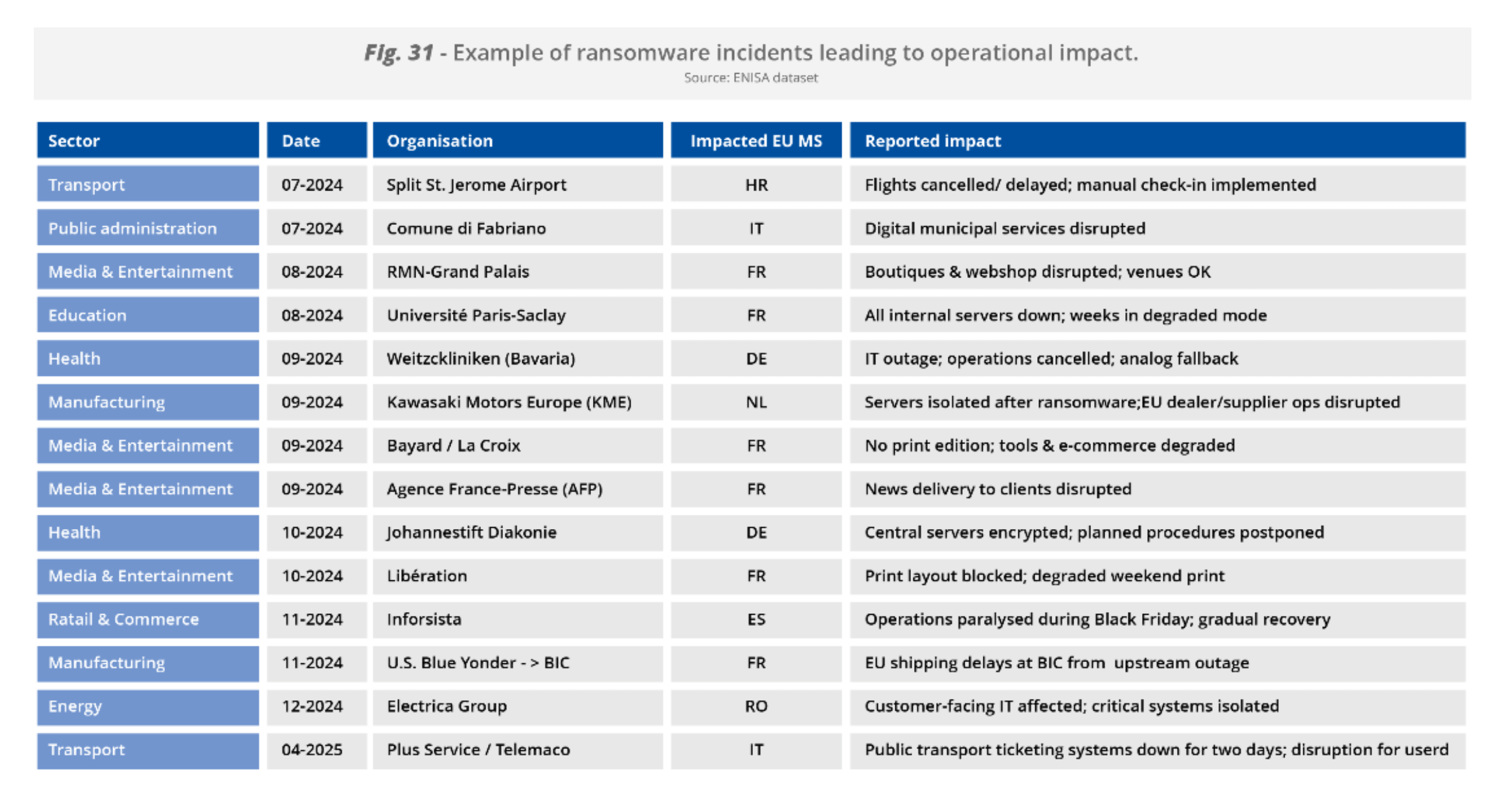
ENISA - Examples of ransomware incidents and impacts
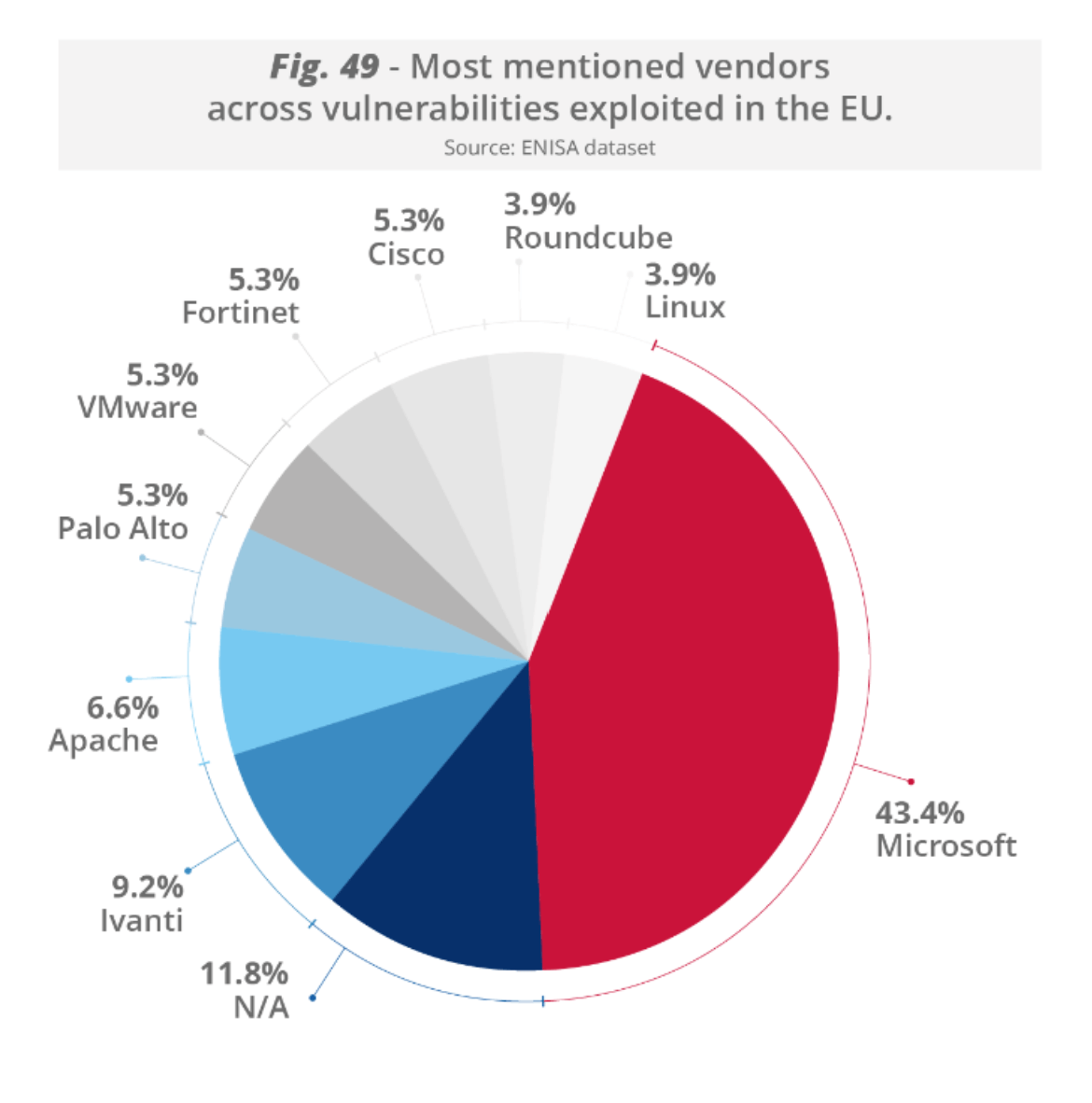
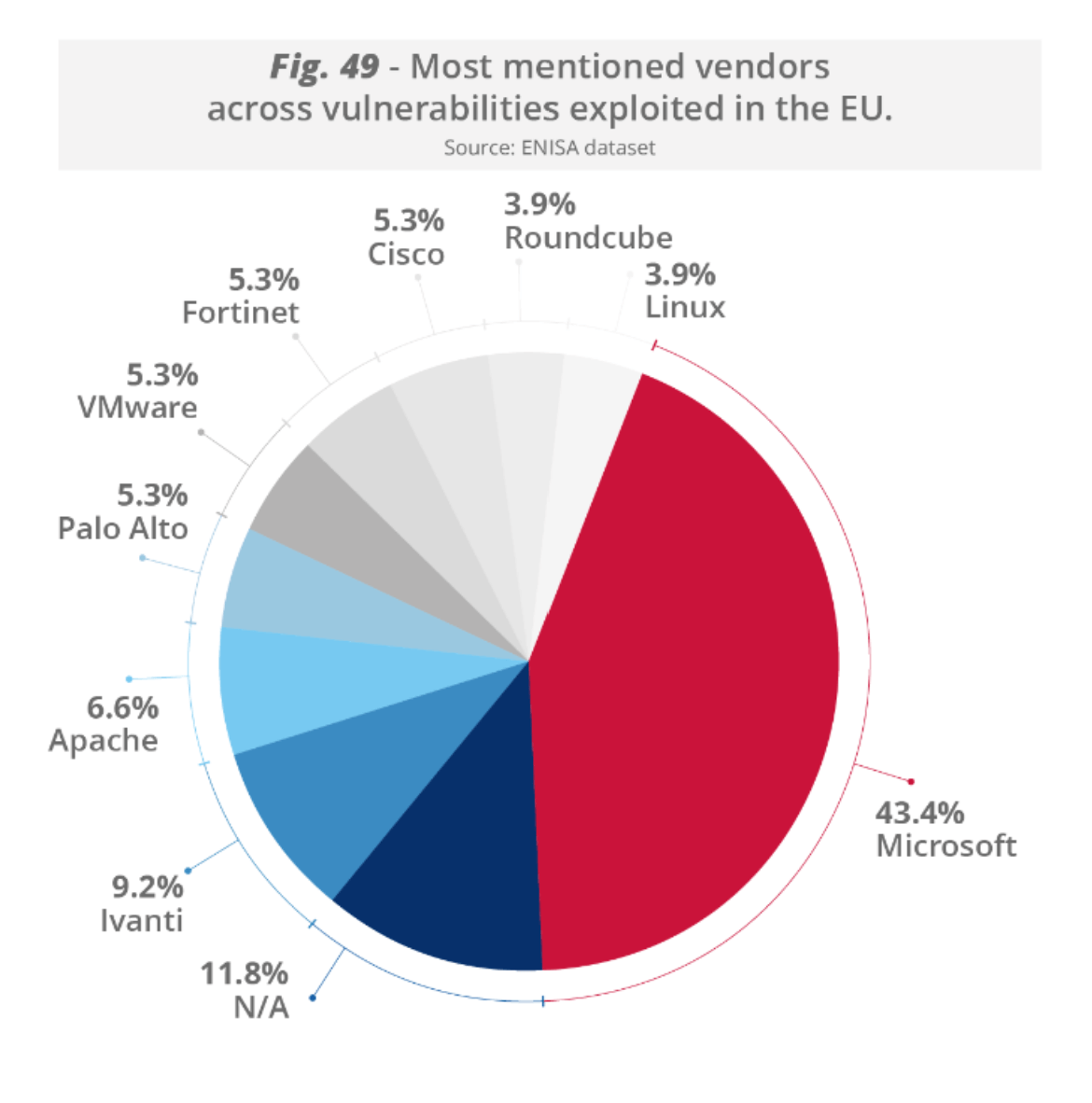
ENISA - Most mentioned vendors vulnerabilities
Australian Signals Directorate
Title: Annual Cyber Threat Report 2024-2025
Link: https://www.cyber.gov.au/about-us/view-all-content/reports-and-statistics/annual-cyber-threat-report-2024-2025
Great for:
A perspective from an APAC country that also bridges the west, with a lot of attraction for state-sponsored and crime-for-profit actors. Good case studies and insight into some sectors and attack types that aren't covered as deeply in other reports, i.e. looks at bulletproof hosting and dark web commerce. Good insight also into how a proactive government works with affected businesses, industry infrastructure and other stakeholders to help protect their constituents. Recommendations section is very easy to understand and good for non-IT staff to get a good clear view for placing priorities. 5 out of 5 stars recommend to take a look.
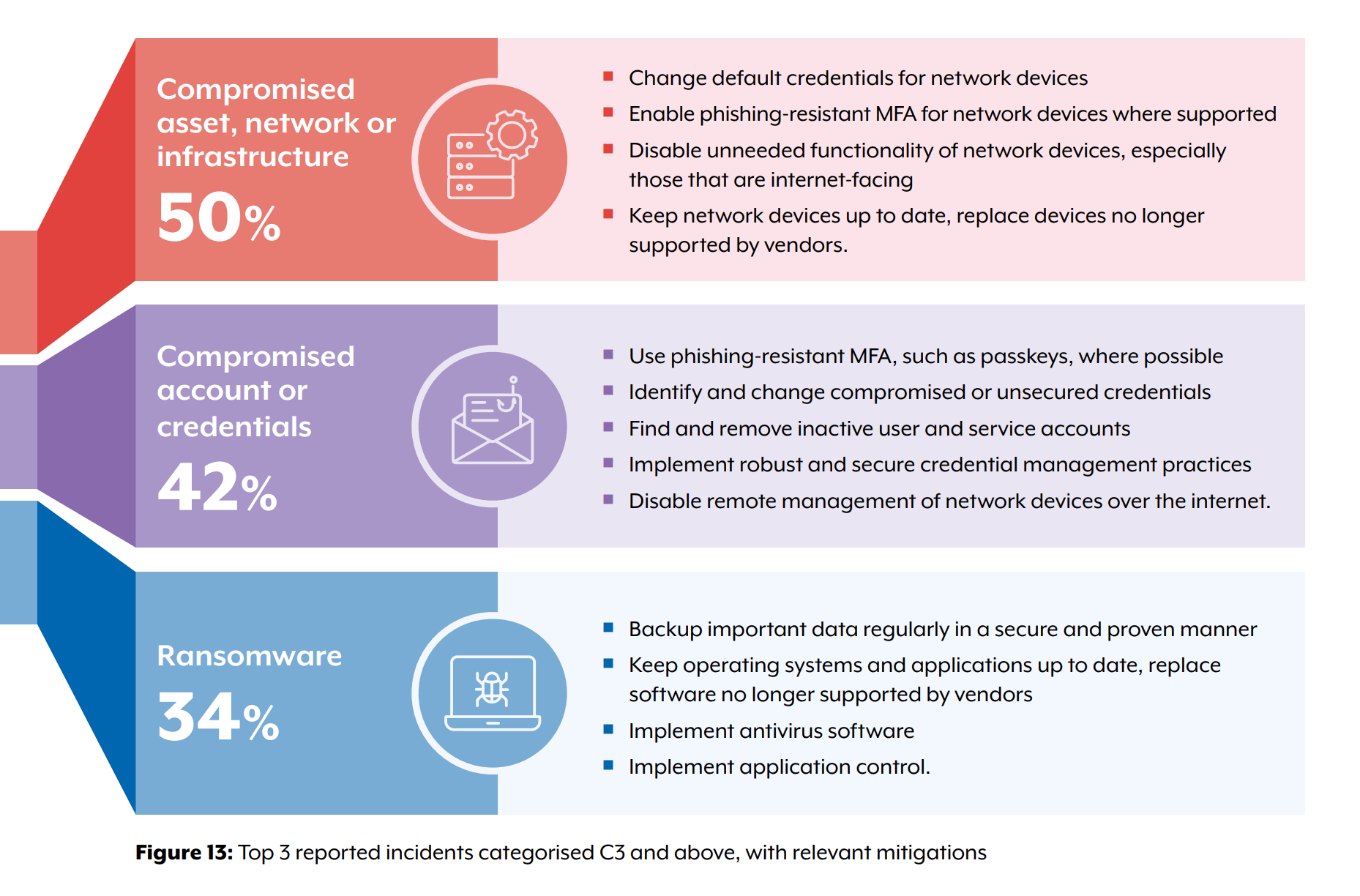
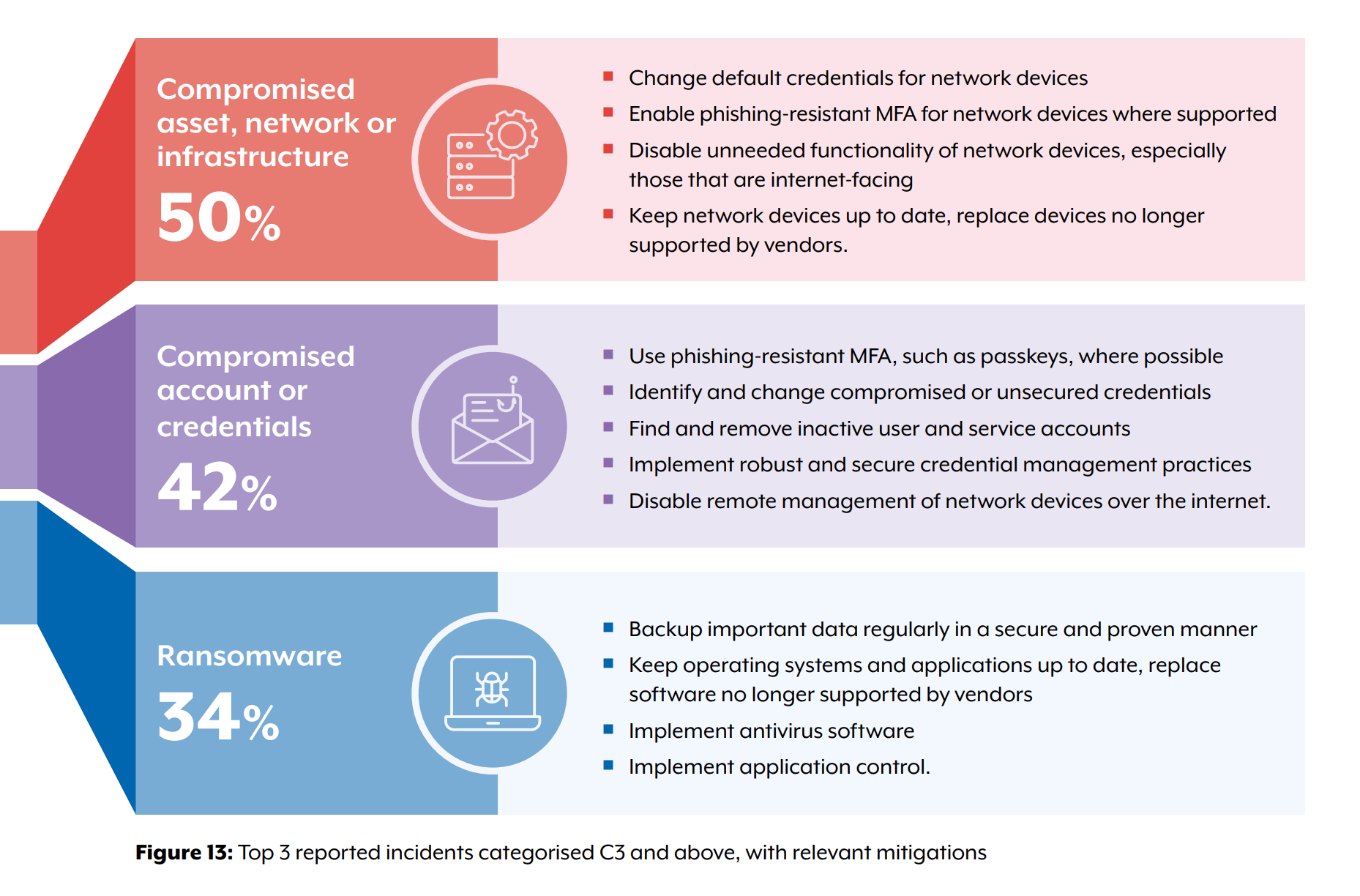
ASD - Incident types and relevant mitigations
Sample takeaways:
- Average self-reported cost of cybercrime per report for businesses, up 50% overall ($80,850)
- Small business: $56,600 (up 14%)
- Medium business: $97,200 (up 55%)
- Large business: $202,700 (up 219%)
- Sample Case Studies covered in the doc that were quite illuminating:
- As part of its ongoing mission to protect Australians online, ASD’s ACSC is proactively leveraging trusted strategic industry partnerships. By using Cloudflare’s established API-based abuse reporting, it has been able to programmatically report malicious websites for prompt review and action. This prompt reporting by ACSC helps Cloudflare verify and then display a phishing warning page that warns Australians of the potential dangerous activity. The warning page requires the user to physically click through to ignore the warning and this critical intervention serves as an immediate, frontline defence for Australians. This has protected not only ASD’s ACSC partners, but also all Australians interacting with the infrastructure from personal computers and portable devices.
- On 12 February 2025, the Australian Government imposed targeted sanctions, under the Autonomous Sanctions Regulations 2011, on a cyber infrastructure entity – ZServers – and 5 of its Russian employees. The sanctions were in response to ZServers’ role in providing BPH services to host and disseminate data stolen from compromises of Australian and other organisations in 2022. Australia’s cyber sanctions are strengthened by tri-lateral sanctions imposed by the US and UK against these malicious cyber actors, demonstrating our collective resolve to combat cybercrime.
- In April 2025, AFP’s Operation Firestorm collected intelligence that a scam centre in Bangkok, Thailand, was being established to target Australians with investment bond scams. Information indicated that during a previous scam operation between January and February 2025, the syndicate successfully deceived Australian victims into investing $28 million. In June 2025, under Operation Firestorm-Apiarist, AFP investigators supported the Royal Thai Police with the disruption of the identified scam centre resulting in the arrest of 13 persons, including 5 Australian nationals.
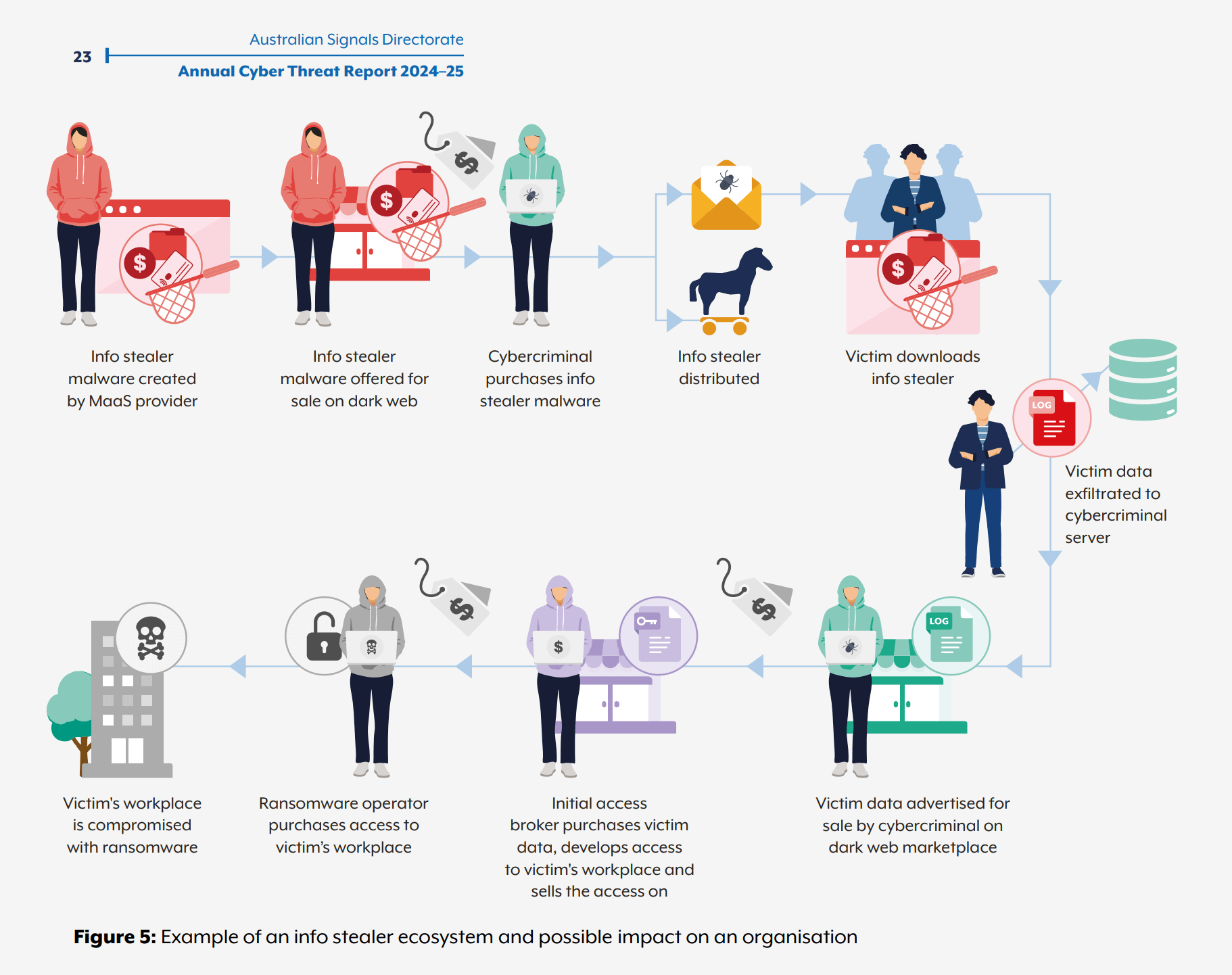
ASD - Infostealer economy life cycle infographic
Conclusion
Overall, we highly recommend these well-researched annual cybersecurity surveys based on in most cases very large datasets and surveys. Reading through them can help bring you and your company executives up to date on the always changing security landscape. It isn't hyperbole or cliché to say that the threats and risks are changing, they actually are with AI, technical complexity resulting in more vulnerabilities and always adapting bad actors making it important to know the latest news to be able to defend against them.

 2026-03-11 - 网络安全
2026-03-11 - 网络安全 2026-02-02 - 网络安全
2026-02-02 - 网络安全