The offerings and options for Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) for workstations and servers is well established, including Managed Detection and Response (MDR) managing it externally.
Mobile EDR Current State
But with so many of us modern world folks working from and accessing work assets and communications from our mobile phones, has EDR and XDR for mobile kept up? At SEIRIM we've scratched our heads on many occasions wondering why we don't have more options that jump out at us as the clear choice for our use cases for mobile, and here we explore why and what the current best choices are in the market.
To be sure - fully fledged solutions do exist and we detail them here. But our use case is often in the range of "SME that either opts for an open source or inexpensive option, something bootstrapped, but if it's just too expensive they'll just choose nothing." Well, we don't want our clients heading out into the world without protection, so we study, test and recommend here the solutions we think are the best bang for the buck.
What are our Goals for EDR?
- Enhanced Threat Detection: EDR solutions help identify malicious activity and potential threats on mobile devices in real-time. These solutions provide advanced detection capabilities, such as anomaly detection, behavioral analysis, and signature-based methods, to spot threats like malware, phishing, and unauthorized access attempts.
- Comprehensive Endpoint Visibility: With employees increasingly working remotely and using mobile phones for work, having full visibility into mobile devices' activities becomes crucial. EDR provides centralized monitoring of all devices, ensuring that security teams have detailed insights into potential vulnerabilities or attack vectors across all mobile endpoints.
- Rapid Incident Response: When an incident occurs on a mobile device, EDR, XDR, and MDR solutions provide automated response mechanisms, such as isolating the device, blocking malicious processes, or even remotely wiping compromised devices. This ensures quick containment and prevents the spread of threats across the network.
- Data Protection: Mobile phones are prone to data breaches, especially when employees access sensitive company data from unsecured or public networks. EDR solutions help to enforce security policies, such as encryption, secure access controls, and data loss prevention (DLP), to protect sensitive business information on mobile devices.
- Advanced Threat Intelligence: By leveraging threat intelligence feeds and security data from across the enterprise network, XDR and MDR solutions provide actionable insights into emerging threats. This information helps security teams proactively address vulnerabilities and threats that could target remote workers’ mobile devices.
- Behavioral Monitoring: These solutions use behavioral analytics to detect unusual activities on mobile devices, such as unauthorized access attempts, risky app installations, or abnormal data transfers. This proactive approach helps to catch sophisticated threats that might otherwise go undetected.
- Reduced Security Blind Spots: In remote and hybrid work environments, employees often use mobile devices to access corporate resources. EDR solutions eliminate potential security blind spots by continuously monitoring all devices, regardless of location, and ensuring consistent protection across the enterprise.
- Automated and Scalable Security: As the number of remote workers grows, managing the security of each mobile device manually becomes challenging. EDR, XDR, and MDR solutions provide automated security management, including patching, updates, and threat responses, ensuring that the security infrastructure scales with the growing workforce.
- Compliance and Regulatory Requirements: Many industries have strict compliance requirements for protecting mobile data, especially for remote work. EDR, XDR, and MDR solutions help organizations meet these regulatory standards (e.g., GDPR, HIPAA) by ensuring that mobile devices are adequately secured and monitored.
- Centralized Management: With a centralized security management console, IT and security teams can easily monitor, manage, and analyze security events across mobile devices. This simplifies incident management and response, reducing the time and effort needed to address security threats.
In essence, implementing these solutions on mobile phones enhances overall mobile device security, supports a strong remote work policy, and minimizes the risk of a security breach affecting the organization’s digital infrastructure.
EDR Solutions in Our Test:
There are actually many, but we narrowed the list down here to ones that appealed to us as being approachable for implementation, priced within reasonable ranges, and up to date and from reputable firms:
- Sophos Intercept X
- WithSecure Elements Mobile Protection
- Trend Vision One
- Xcitium
Sophos Intercept X for Mobile
Sophos Intercept X for Mobile offers a lightweight, user-friendly solution for managing mobile threats and enforcing corporate policy across both Android and iOS platforms. It integrates seamlessly into Sophos Central, the cloud-based console used to manage all Sophos products in one place.
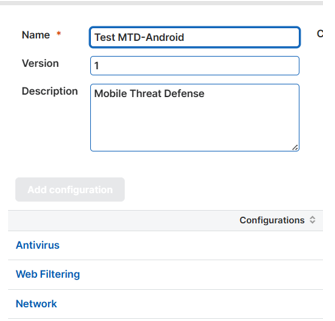
Below are key screenshots from the test run on both Android and iOS:
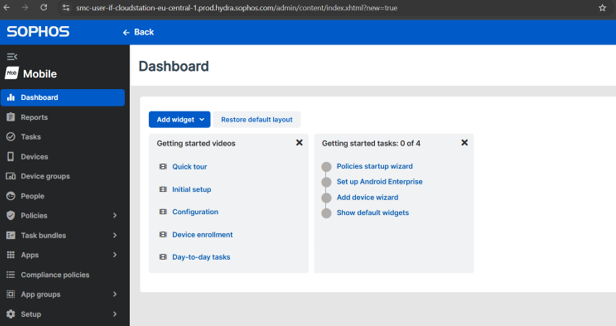
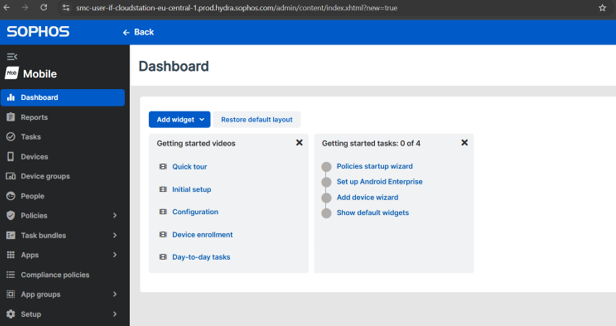
- Sophos Mobile Dashboard
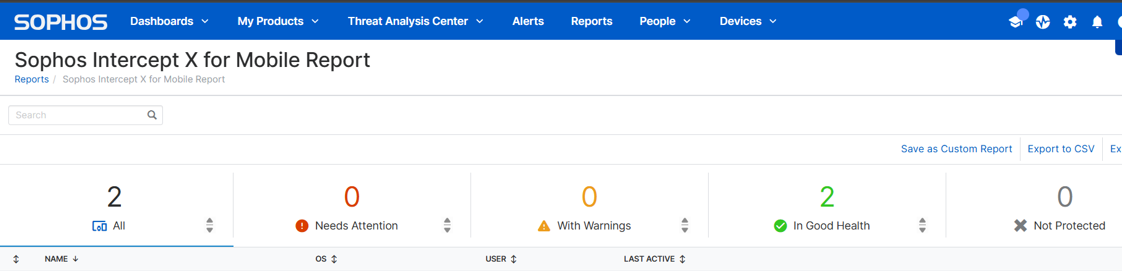
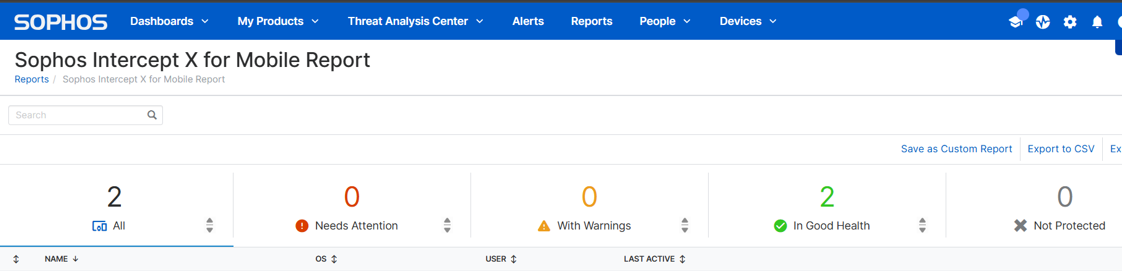
- Sophos Intercept X for Mobile Report
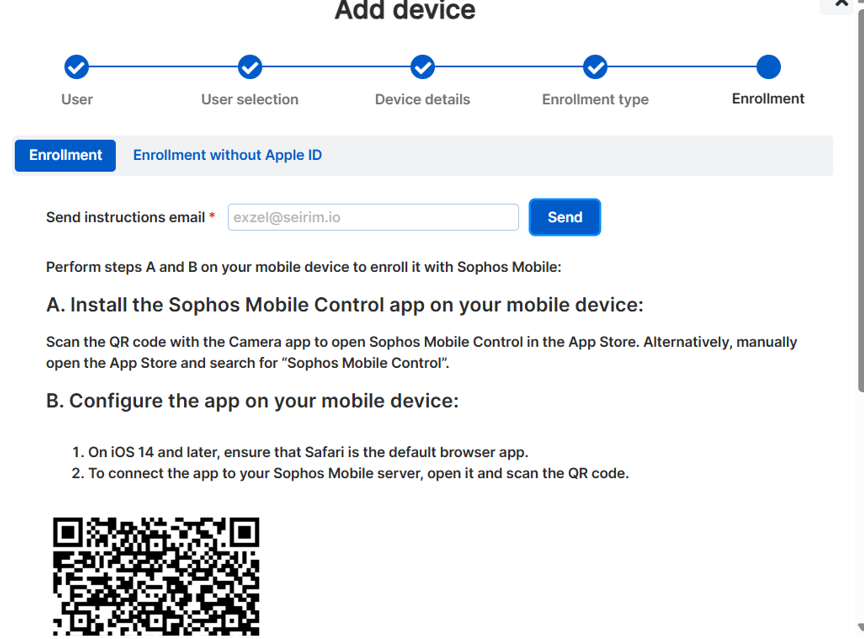
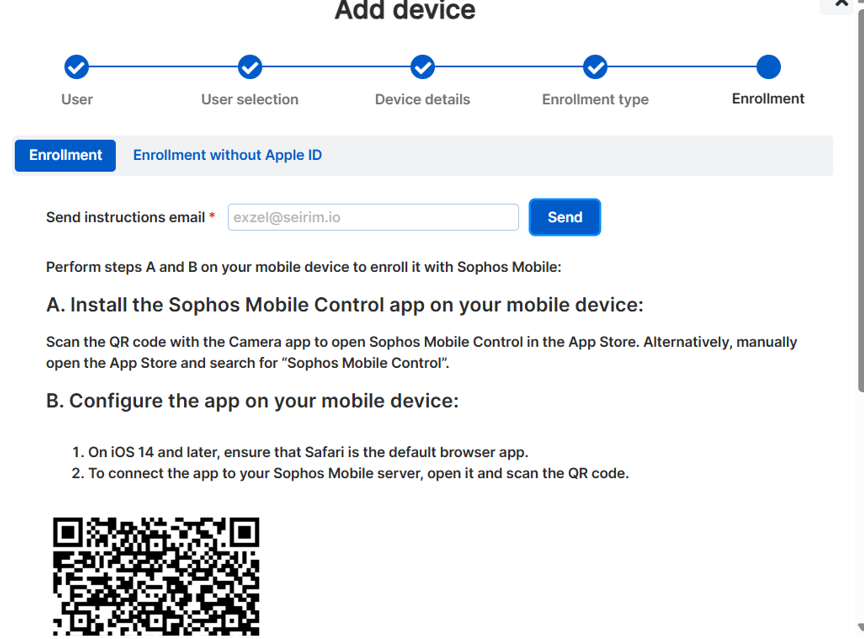
- Mobile Device Enrollment View Process in Sophos Mobile
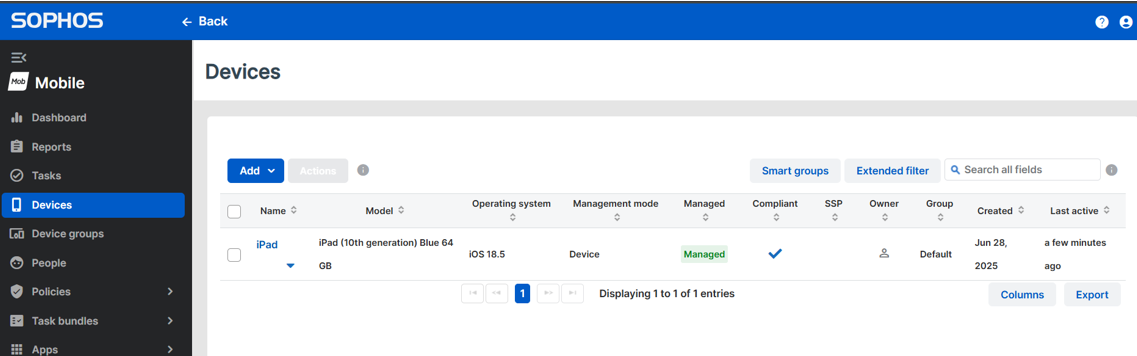
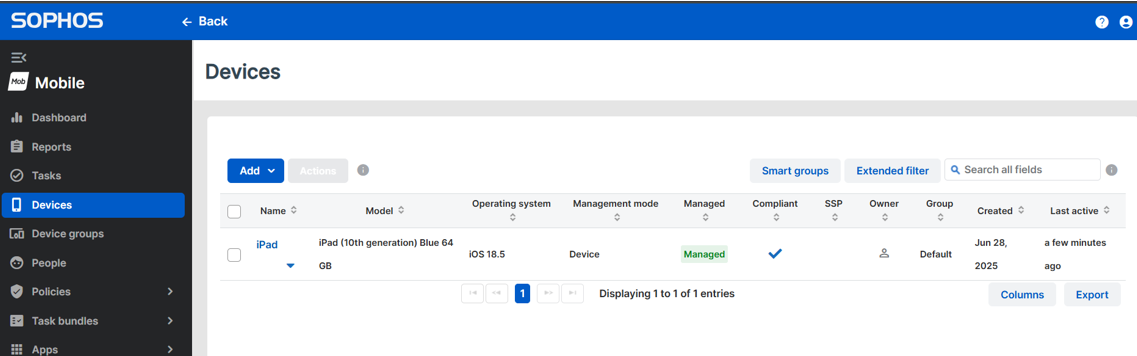
- Confirmation of a Successful Mobile Device Enrollment
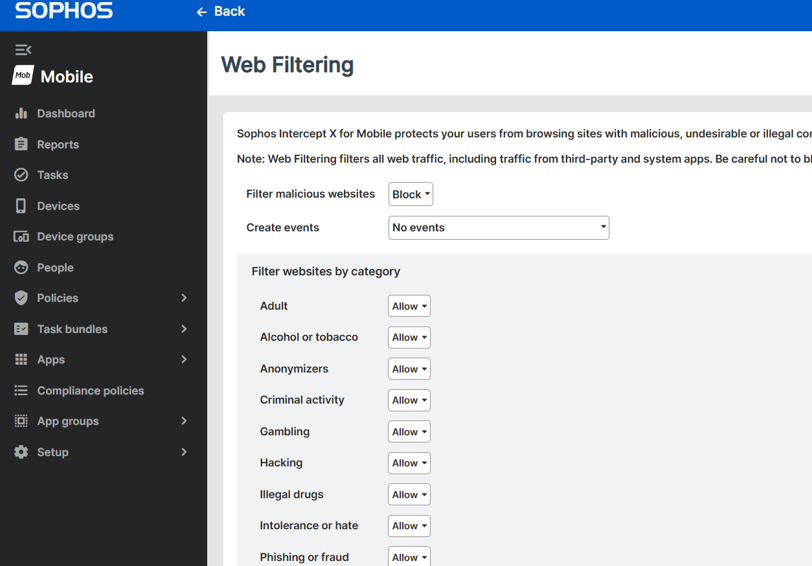
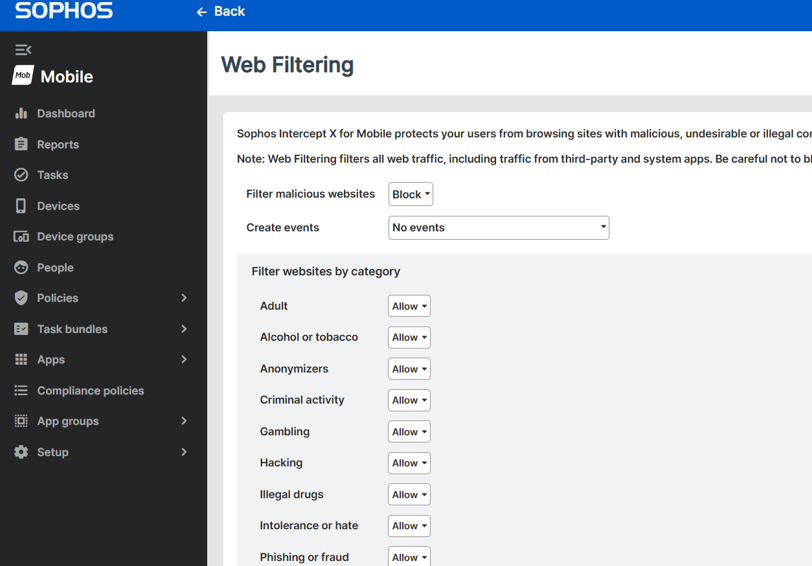
- Web Filtering Policy Applied to Mobile Endpoints
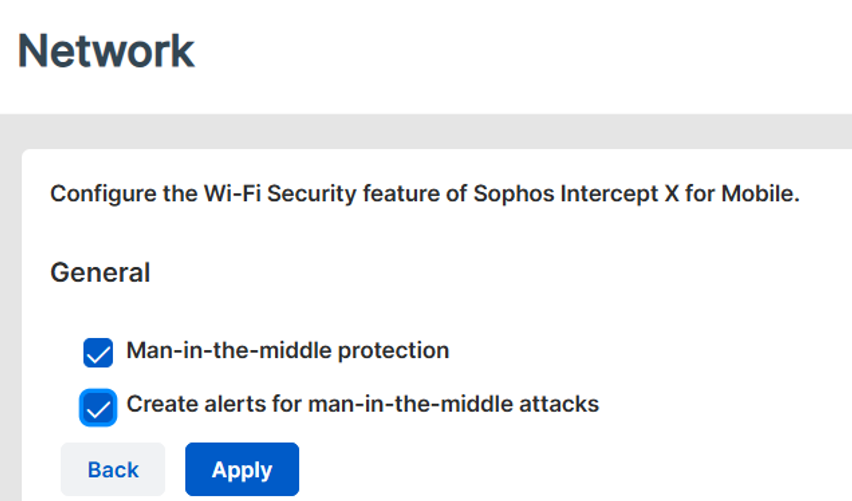
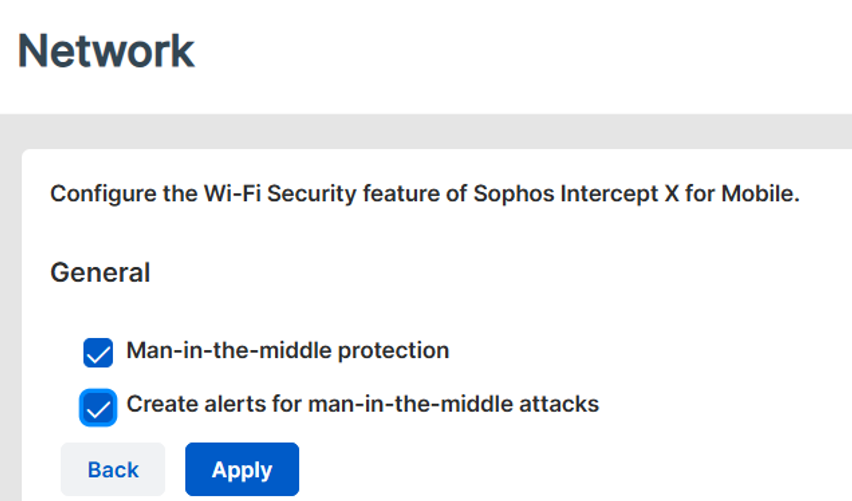
- Network Protection Configuration
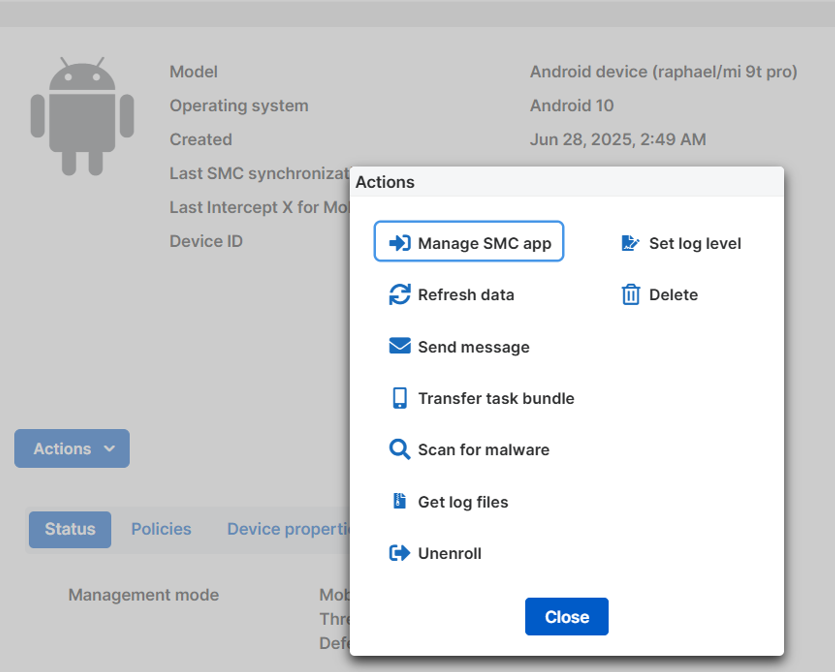
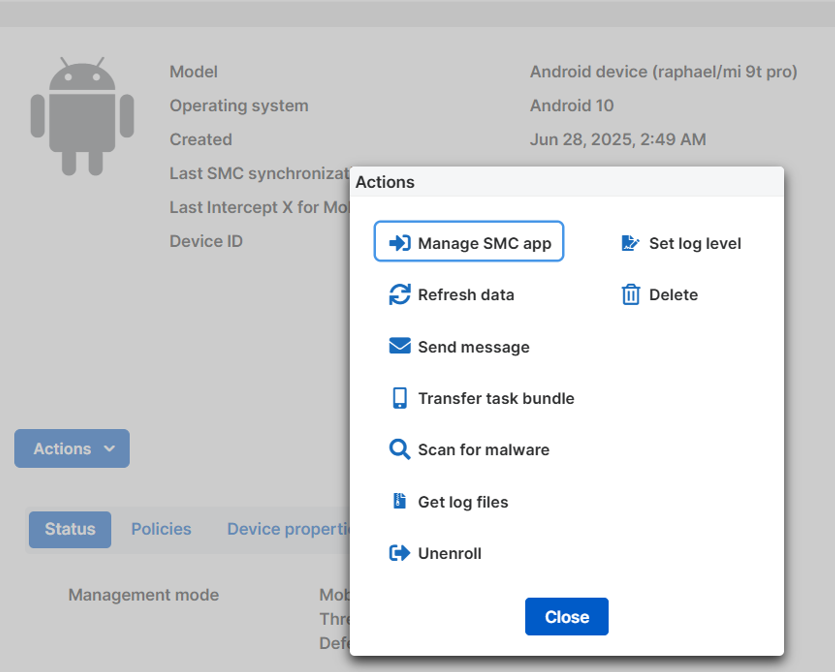
- Available Remote Actions for Android Devices
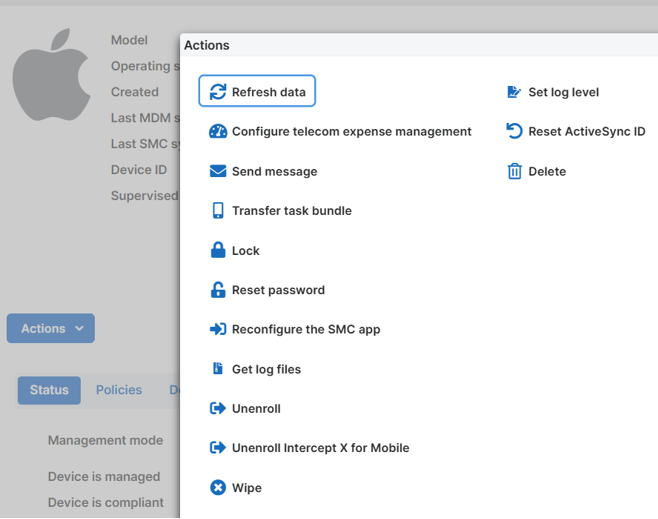
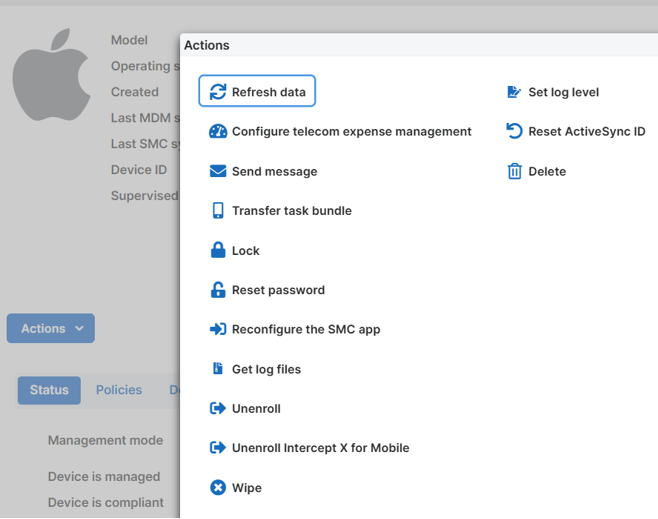
- iOS Device Actions Limited by OS Restrictions
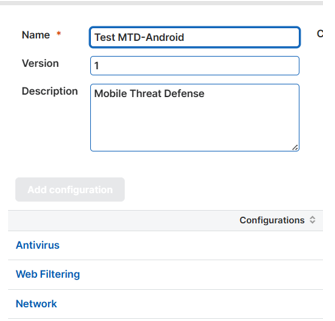
- Custom Android Security Policy Settings
Pros
- Unified Endpoint Management: Supports iOS, Android, Windows, and macOS devices.
- Web Filtering: Blocks access to malicious and inappropriate website categories, which works well on Android
- Network Threat Protection: Detects suspicious network activity like man-in-the-middle attacks.
- Centralized Management: Lets you apply policies, push updates, track threats, and remotely scan, lock, or wipe devices
- Policy-based Compliance Enforcement: Devices out of compliance can be flagged or restricted from accessing corporate data
- SMS Filtering (iOS): With the SMS Filtering configuration, you define domain names for the SMS Filtering feature of Sophos Intercept X for Mobile.
Cons
- No malware scanning on iOS: Due to Apple’s restrictions, iOS devices cannot be scanned for malware like on Android
- No advanced EDR/XDR capabilities on mobile: There’s no behavioral analysis, threat hunting, or live response like in desktop EDR solutions - it’s more MTD than true mobile EDR
- Android-only Malware Scanning: Real-time scanning for apps and sideloaded files only exists on Android. iOS relies on configuration and network monitoring
- SMS filtering not available on Android: Unlike iOS, where SMS filtering can be enabled in the policies, the option doesn’t appear for Android devices
Summary
Sophos Intercept X for Mobile is a strong contender if you need basic mobile security, especially if you’re already within the Sophos ecosystem. It’s more of a Mobile Threat Defense (MTD) tool than a full EDR solution, but for many organizations, that’s already a good start. Android support is good, while iOS is understandably limited due to platform restrictions.
Vocabulary
A little vocabulary to help us navigate the usefulness of tools among all the jargon and marketing speak:
- Endpoint Detection and Response (EDR): A cybersecurity solution focused on detecting, investigating, and responding to threats on endpoint devices (such as laptops, desktops, and mobile phones) in real-time. EDR systems provide detailed visibility into endpoint activities and allow for automated responses to security incidents.
- Extended Detection and Response (XDR): An advanced version of EDR, XDR extends threat detection and response capabilities beyond endpoints to include networks, servers, cloud environments, and other critical infrastructure. It integrates data from multiple security layers for improved threat detection, faster incident response, and a unified view of the security landscape.
- Managed Detection and Response (MDR): A managed security service that provides organizations with external, 24/7 monitoring, threat detection, and incident response capabilities. MDR providers use advanced tools to detect threats and manage responses on behalf of the organization, offering expert assistance in handling security events.
- Mobile Device Management (MDM): MDM refers to a set of security and management tools used to monitor, manage, and secure mobile devices such as smartphones, tablets, and laptops within an organization. MDM solutions allow IT administrators to enforce security policies, manage apps, track devices, and remotely wipe data in the event of theft or loss, ensuring that mobile devices comply with organizational security standards.
Other technologies working similarly or connected to EDR include:
- Security Information and Event Management (SIEM): SIEM systems aggregate and analyze log data from various sources within an organization’s IT infrastructure to detect potential security threats. SIEM tools provide centralized monitoring, event correlation, and real-time alerts, making them crucial for threat detection, compliance monitoring, and incident response. SIEM can integrate with EDR, XDR, and MDR systems to enhance visibility and provide deeper insights into security events.
- Security Orchestration, Automation, and Response (SOAR): SOAR platforms help automate and streamline security operations by integrating security tools, processes, and workflows. SOAR enables faster incident response by automating repetitive tasks, such as threat remediation and reporting, and it allows security teams to respond to incidents more efficiently. SOAR can work alongside EDR, XDR, and MDR to enhance response times and improve incident management.
- Mobile Threat Defense (MTD): MTD solutions focus on identifying and mitigating threats specific to mobile devices, such as malware, phishing, and unsafe network connections. MTD is closely related to MDM but focuses more on detecting and responding to mobile-specific threats rather than just device management. Combining MTD with MDM offers a comprehensive mobile security solution for managing and protecting mobile endpoints.

 2026-03-11 - 网络安全
2026-03-11 - 网络安全 2026-02-02 - 网络安全
2026-02-02 - 网络安全