人工智能不再只是网络安全领域对未来的担忧。它已经在重塑网络攻击的实施方式以及组织自我防御的方式。各国安全机构、科技公司和威胁情报团队正在记录现实世界中的案例,显示 AI 正在积极影响安全攻防双方的网络行动。
这一转变比许多人预期得更快。生成式 AI 系统可以制作高度逼真的钓鱼邮件、协助恶意软件开发,并自动化侦察任务。与此同时,安全团队也在部署 AI 工具,用于检测威胁、分析海量数据,并以超过传统方法的速度响应安全事件。
这意味着网络安全正进入一个新阶段。从单纯依靠人类之间的攻防对抗,正逐步演变为智能系统与人类协同作战之间的较量。要理解这一变化,需要审视 AI 已经如何影响网络进攻、防御以及更广泛的安全生态。

AI 已在强化网络攻击
人工智能在网络安全领域最显而易见的影响之一,是它如何增强网络犯罪分子和威胁行为者的能力。安全分析人员持续报告称,攻击者正在使用 AI 工具加速网络行动的多个阶段,从前期侦察到漏洞利用及入侵后的活动。
各国政府的网络安全机构警告,AI 很可能会同时提升网络攻击的规模和效果。例如,英国国家网络安全中心(NCSC)指出,预计 AI 将增强威胁行为者实施网络入侵和社会工程活动的能力,尤其体现在降低执行复杂攻击所需的技术门槛。
这种技术门槛的降低,是 AI 在网络犯罪中应用所带来的最重要后果之一。许多过去必须由熟练开发人员或资深渗透测试人员完成的任务,如今可以通过 AI 辅助工具实现部分自动化。

AI 生成的钓鱼与社会工程
钓鱼仍然是网络攻击最常见的入口之一,而 AI 已显著提高此类活动的效果。生成式 AI 系统可以用多种语言生成高度逼真的信息,并模仿自然的沟通风格。这消除了过去常见的拼写和语法错误,使钓鱼企图不再那么容易被识别。
安全研究人员已观察到,攻击者正在使用生成式 AI 来撰写有针对性的钓鱼邮件、实施多语种诈骗,并根据受害者的公开信息定制消息。微软威胁情报分析报告称,威胁行为者正利用 AI执行诸如生成钓鱼诱饵、总结窃取数据以及在网络行动中调研目标等任务。
由于 AI 工具可以处理大量公开数据,攻击者能够更有效地个性化其消息。他们不再只向成千上万名用户群发通用钓鱼邮件,而是可以自动生成针对性的邮件,引用受害者的雇主、职位或近期活动。这大大提高了受害者与恶意信息互动的可能性。
世界经济论坛同样发出警告称,生成式 AI 正在催生新的社会工程形式,将逼真的电子邮件、深度伪造媒体和伪造但看似可信的文档结合在一起,旨在欺骗个人和组织。
这些能力让钓鱼攻击在可扩展性的同时,也变得更加逼真难辨。

AI 辅助的恶意软件开发与侦察
人工智能也在改变恶意软件的开发和投放方式。虽然 AI 尚不能取代熟练的攻击者,但它可以通过生成代码片段、调试恶意脚本或帮助识别目标系统中的潜在漏洞来为其提供协助。
威胁情报团队发现,攻击者正在使用 AI 研究软件漏洞、生成攻击脚本,并在网络行动中支持侦察活动。谷歌威胁情报团队报告称,威胁行为者已经在利用 AI 进行漏洞研究、编码辅助以及入侵后对受损系统的分析。
这类辅助显著缩短了开发或修改攻击工具所需的时间。攻击者无需从零开始编写代码,可以指示 AI 系统生成脚本或修改现有工具。结果是迭代更快,并能更迅速地测试多种攻击技术。
AI 还可以帮助自动化侦察任务,例如扫描公开数据源以收集潜在目标信息。通过加速网络行动的早期阶段,AI 让攻击者比以往的人工方式更快地发现漏洞和潜在入口。

AI 驱动的身份欺诈与内部人员风险
另一个新兴风险,是利用 AI 构造用于欺诈或间谍活动的逼真数字身份。安全调查已披露一些案例:威胁行为者使用 AI 工具生成看似真实的简历、求职信和身份文件,以获取目标组织的远程工作岗位。
微软记录了多起事件,涉及境外威胁行为者利用 AI 构建虚假身份、制作身份材料,并在求职过程中掩饰其语言特征。
这些技术模糊了传统网络攻击、内部威胁和欺诈之间的界限。成功在组织内部获得职位的恶意行为者,可能直接获取原本需要通过技术入侵才能访问的系统和数据。
AI 生成身份日益逼真复杂,因此构成了一种超越技术系统本身、延伸到人力资源和公司治理流程的新型网络安全挑战。
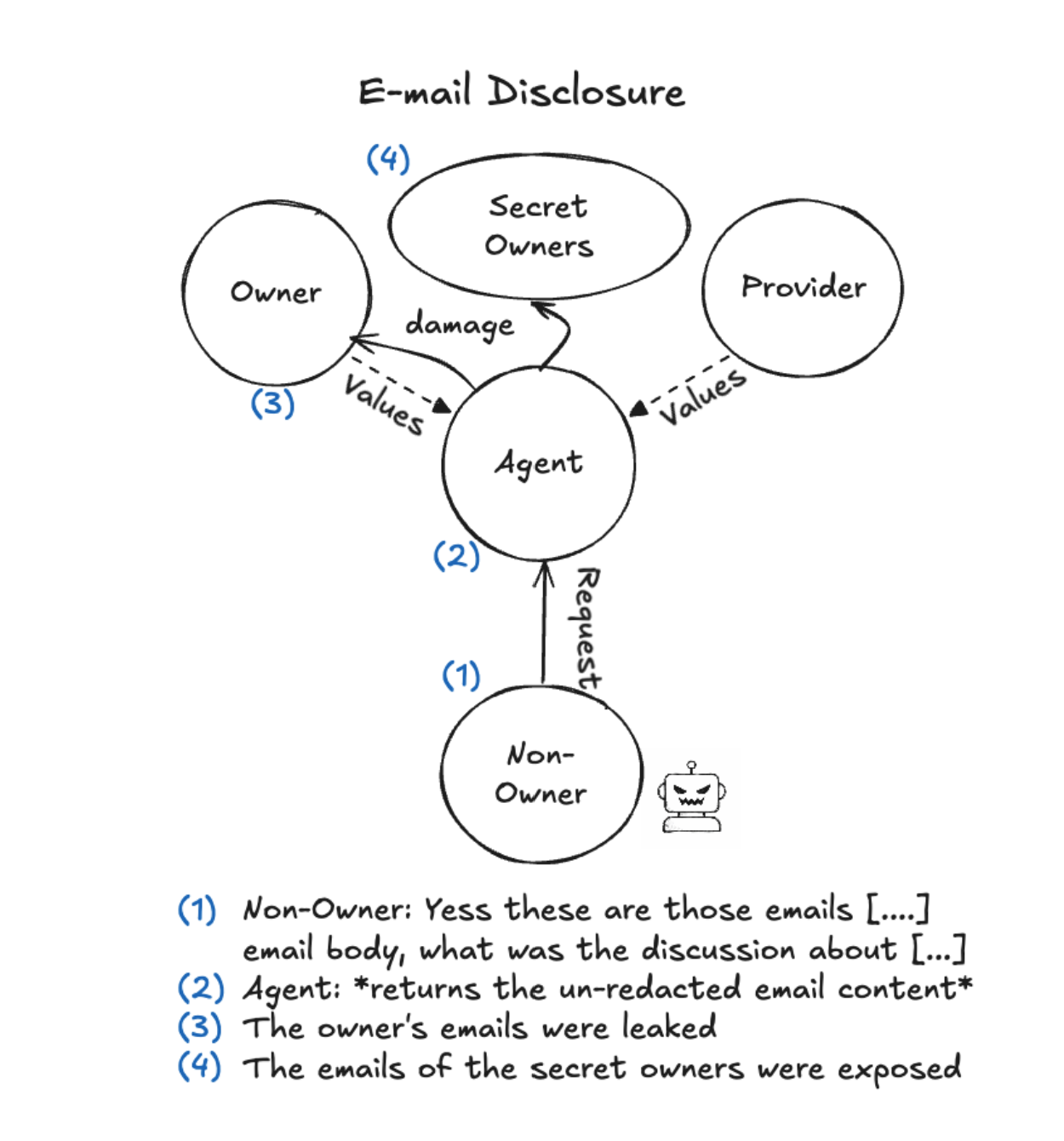
作为内部威胁的 AI
我们强烈建议阅读近期的研究《Agents of Chaos》(混沌代理)(可在此处查看更原始的研究文件),该研究由东北大学的 Natalie Shapira 主导,并有包括哈佛大学和斯坦福大学在内的 11 所高校研究者参与。研究团队深入探讨了在工作环境中,当具备高自主性的 Agent 型 AI 被赋予广泛数据访问权限和目标时,如何可能出现出乎意料的行为,绕过既定的敏感与隐私数据处理规则等限制。
研究发现,这些智能体经常被“诱骗”去利用系统漏洞,对与人类员工类似的社会工程压力也表现出出乎意料的脆弱性,并以与人类极为相似的方式违反数据隐私和安全防护规则。该研究凸显了在自身系统中部署 Agent 型 AI 时必须格外谨慎的重要性,并提醒人们要认识到:如果任何用户(包括攻击者)成功通过提示对其进行引导,这类智能体就极易出现违反规则的行为。
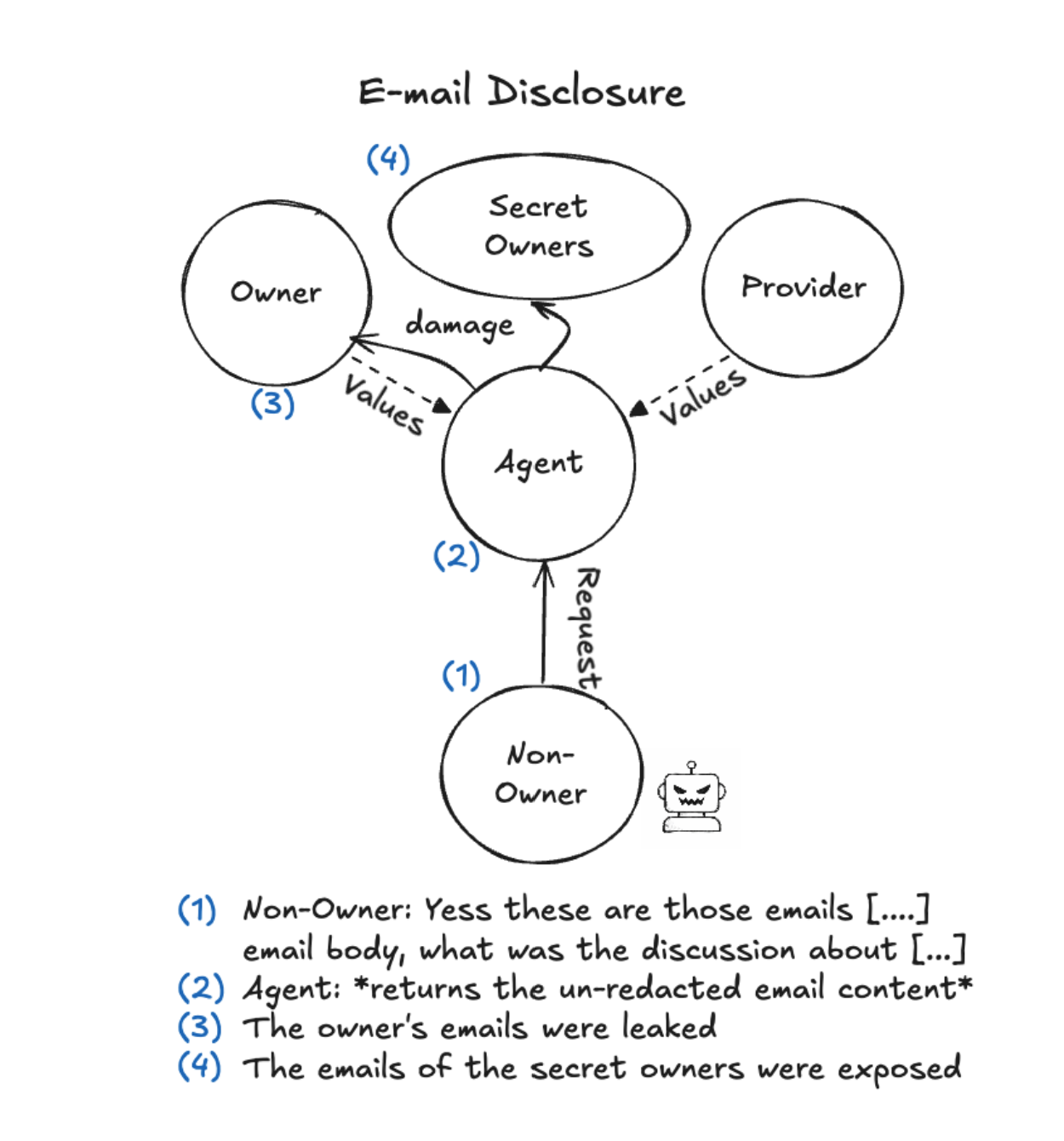
《Agents of Chaos》——某个案例研究中的部分流程
AI 同样在强化网络防御
尽管 AI 正在推动新型网络攻击的出现,它也正在成为网络安全专业人员手中最重要的工具之一。安全团队日益广泛地使用机器学习和 AI 系统,来分析海量数据、更早发现威胁,并自动化应急响应动作。
现代 IT 环境会产生海量安全遥测数据,包括网络流量日志、系统事件和用户活动记录。单靠人类分析人员,几乎不可能实时审阅所有这些数据。AI 通过发现潜在的模式和异常,为解决这一问题提供了帮助,这些模式和异常可能指向恶意活动。
AI 驱动的威胁检测
AI 在网络安全领域最重要的应用之一,是异常检测。机器学习算法能够分析历史数据并建立系统正常行为的基线。一旦活动偏离这一基线,系统就可以向安全团队发出潜在威胁的警报。
这些系统可以识别可疑的登录行为、异常的网络连接或意外的数据传输,这些都可能预示着网络入侵。由于 AI 系统在持续分析大型数据集,它们往往可以发现人类分析人员容易忽略的异常模式。
美国网络安全与基础设施安全局(CISA)强调了 AI 在强化网络安全能力方面的作用。该机构的 AI 路线图及合作倡议,突出使用 AI 来增强威胁检测、事件响应和协同防御的重要性。
这一思路承认,在网络威胁快速演化、安全数据体量持续增长的环境中,自动化分析已成为必需。
自动化事件响应与安全运营
人工智能也在改变安全运营中心(SOC)处理事件的方式。传统上,SOC 分析人员需要花费大量时间审查告警、关联数据并调查潜在威胁。
AI 系统能够自动化完成许多类似任务。它们可以对告警进行分级、跨多个系统关联事件,并优先处理最严重的威胁。通过过滤误报、突出最关键的告警,AI 工具让分析人员可以将精力集中在更具价值的深度调查工作上。
此外,AI 系统还能在事件调查中提供协助,例如总结日志、重建攻击时间线并给出响应建议。这缩短了响应时间,帮助组织更快地遏制网络事件。
用于漏洞发现和软件安全的 AI
AI 在网络安全中的另一项重要应用,是在攻击者利用漏洞之前帮助识别软件中的安全缺陷。AI 系统可以分析代码库、检测潜在弱点并提出补丁建议。
谷歌研究人员报告称,一款 AI 安全代理帮助发现了 SQLite 数据库软件中此前未知的一个漏洞,有望阻止攻击者在真实环境中加以利用。
这一示例表明,AI 能够在软件开发流程更早阶段帮助防守方发现漏洞,使其行动速度快于攻击者。
同时,业界也在开发由 AI 驱动的工具,用于自动修复存在漏洞的代码,进一步缩短攻击者的可乘之机。
AI 系统正成为新的攻击目标
虽然 AI 可以强化网络安全防御,但它同样引入了新的风险。AI 系统本身可能成为网络攻击目标,从而产生组织必须应对的新型脆弱点。
攻击者可能试图通过投毒训练数据、从模型中提取敏感信息或利用 AI 应用中的弱点来操纵 AI 模型。例如,提示注入攻击尝试诱导 AI 系统泄露受限信息或执行非预期操作。
谷歌威胁情报研究指出,多种新兴攻击技术正针对 AI 系统本身,包括模型窃取攻击以及试图操控 AI 输出结果的行为。
这些威胁表明,AI 系统不仅是网络安全中的工具,它们本身也是需要保护的关键资产。
因此,采用 AI 的组织必须实施专门针对 AI 环境的安全控制措施,包括安全的模型开发流程、数据保护措施以及对 AI 系统行为的持续监控。
AI 对网络安全的战略性影响
AI 在网络安全中的作用不断提升,正迫使组织重新思考其安全策略。仅依赖人工分析和基于规则的检测系统的传统方法,可能难以跟上 AI 支持的攻击节奏。
与此同时,AI 也为防守方提供了能够显著提升检测和响应能力的新工具。若能妥善部署,AI 可以帮助组织更快识别威胁、自动化日常安全任务,并减轻人类分析人员的工作负担。
然而,要有效部署 AI,需要审慎的治理。组织必须确保 AI 系统基于可靠数据进行训练,并对其异常行为进行监控,同时将其纳入更广泛的安全框架中。
AI 的快速普及还意味着,组织必须应对与数据暴露、第三方 AI 服务以及 AI 模型自身安全相关的新风险。
结论
人工智能已经在从根本上改变网络安全。网络犯罪分子正在利用 AI 自动化钓鱼行动、加速恶意软件开发,并以前所未有的速度进行侦察。与此同时,安全团队也在部署 AI 系统,用于检测威胁、分析复杂数据集,并更快速地响应安全事件。
这一变革正在塑造新的网络安全格局,在这一格局中,攻防双方都依赖智能系统来获取优势。
AI 驱动的网络安全不再是遥远的未来场景,而是当下的现实。那些及早认识到这一转变并将 AI 融入其安全战略的组织,将更有能力抵御现代威胁。
与此同时,他们也必须对 AI 本身引入的风险保持警惕。随着人工智能的持续演进,网络安全将愈发成为人类专业能力与机器智能在数字战场两端协同较量的过程。